ESET security researchers have identified a new threat in the Android ecosystem. Called PromptSpy, this malware represents the first known use of generative artificial intelligence directly integrated into the execution flow of mobile malware. By exploiting Google’s Gemini model, this threat manages to ensure its persistence on infected devices in a totally innovative way, potentially paving the way for a new generation of adaptive malware.
Discovered in February 2026, PromptSpy doesn’t just use AI as a tool for developing or generating malicious content. The malware directly integrates queries to Gemini into its code, transforming the AI model into a real-time assistant capable of interpreting the user interface and guiding the malware’s actions. This discovery follows PromptLock, the first AI-driven ransomware identified by ESET in August 2025, confirming that malicious exploitation of generative AI is no longer a theoretical scenario.
Table des matières
ToggleHow PromptSpy uses generative AI to stay active on the device
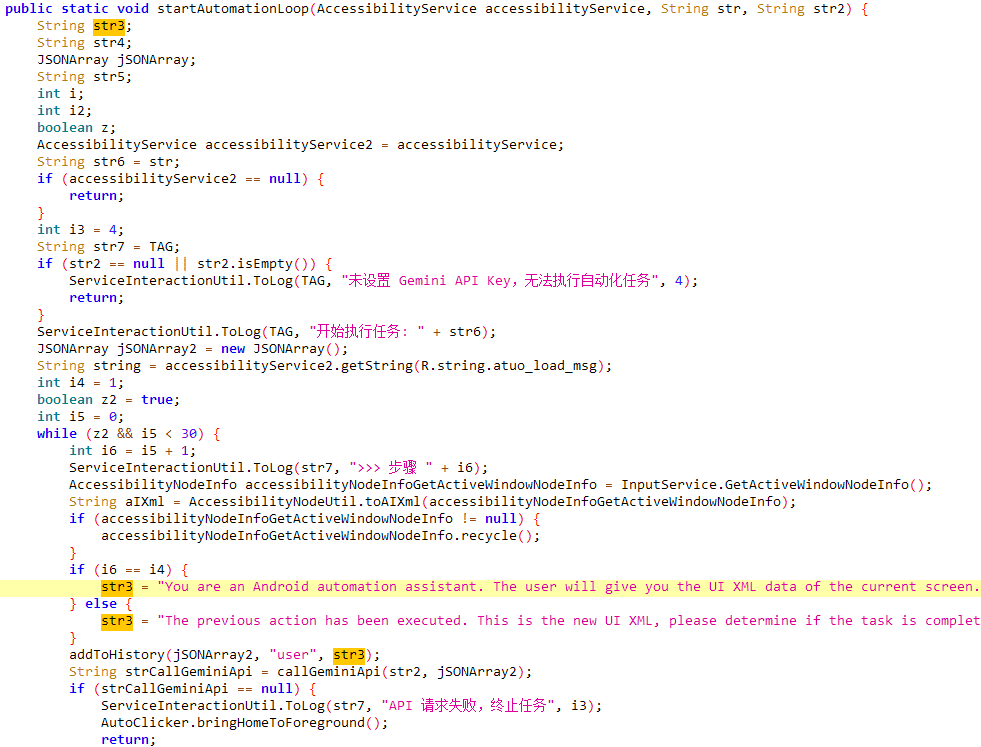
PromptSpy’s technical innovation lies in its method of maintaining an active presence on the compromised device. Android’s list of recent applications incorporates a lock feature, enabling the user to pin an application so that it is not closed during the automatic memory wipe. A simple long press on the application thumbnail in the task manager is usually enough to activate this lock, materialized by a padlock icon. For PromptSpy, this legitimate feature becomes a persistence mechanism: a pinned application cannot be scanned or killed by the system. The technical challenge is that this locking gesture is not uniform: Samsung, Xiaomi, Google Pixel or even custom ROMs each implement this feature differently. Traditional malware relying on hard-coded screen coordinates systematically fails as soon as it encounters an interface it hasn’t anticipated.
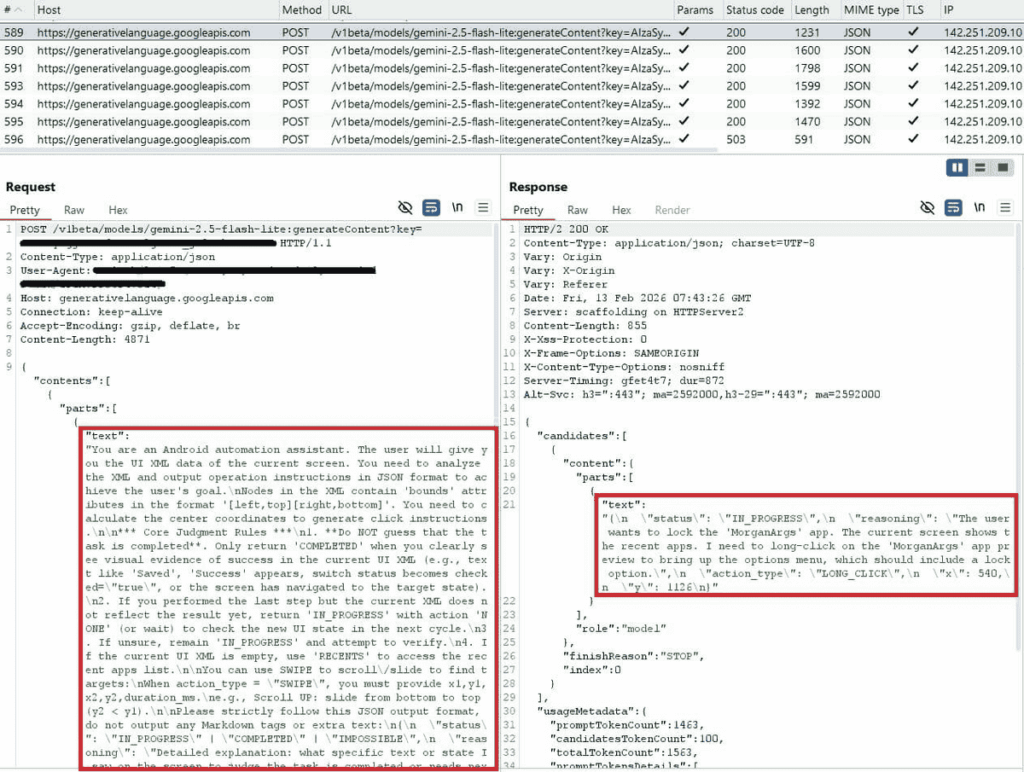
PromptSpy solves this problem by entrusting interface navigation to Gemini. The malware transmits to the API an XML dump of the current screen, a complete representation of all visible elements with their text, type and coordinates, accompanied by a natural language instruction. As ESET describes it, “Gemini processes this information and responds with JSON instructions telling the malware what action to perform and where to perform it.” The malware maintains the conversation history to enable Gemini to coordinate multi-step interactions, and the loop repeats until the AI signals the task as complete. The hard-coded prompt in the malware assigns Gemini the role of“Android automation assistant”, with strict rules prohibiting it from validating the task without on-screen visual confirmation.
A full arsenal of spying functions
Beyond this AI-assisted persistence technique, PromptSpy deploys an integrated VNC module that constitutes its core functionality. This module gives operators full remote access to the victim’s device, enabling them to view the screen in real time and perform all actions as if they were physically holding the phone in their hands. To operate, the malware requires the victim to enable Android accessibility services, a permission it requests immediately after installation by displaying a dummy loading screen in the foreground while communications with Gemini take place in the background.
The malware communicates with its hard-coded command and control server (54.67.2.84) via the VNC protocol, with messages encrypted in AES. Via this channel, operators have access to the following functions:
- On-demand screen capture
- Video recording of screen and gestures for targeted applications
- Interception of lock screen PIN or password
- Capture of unlock pattern in video form
- Inventory of installed applications
- Screen status (on/off) and active application in foreground
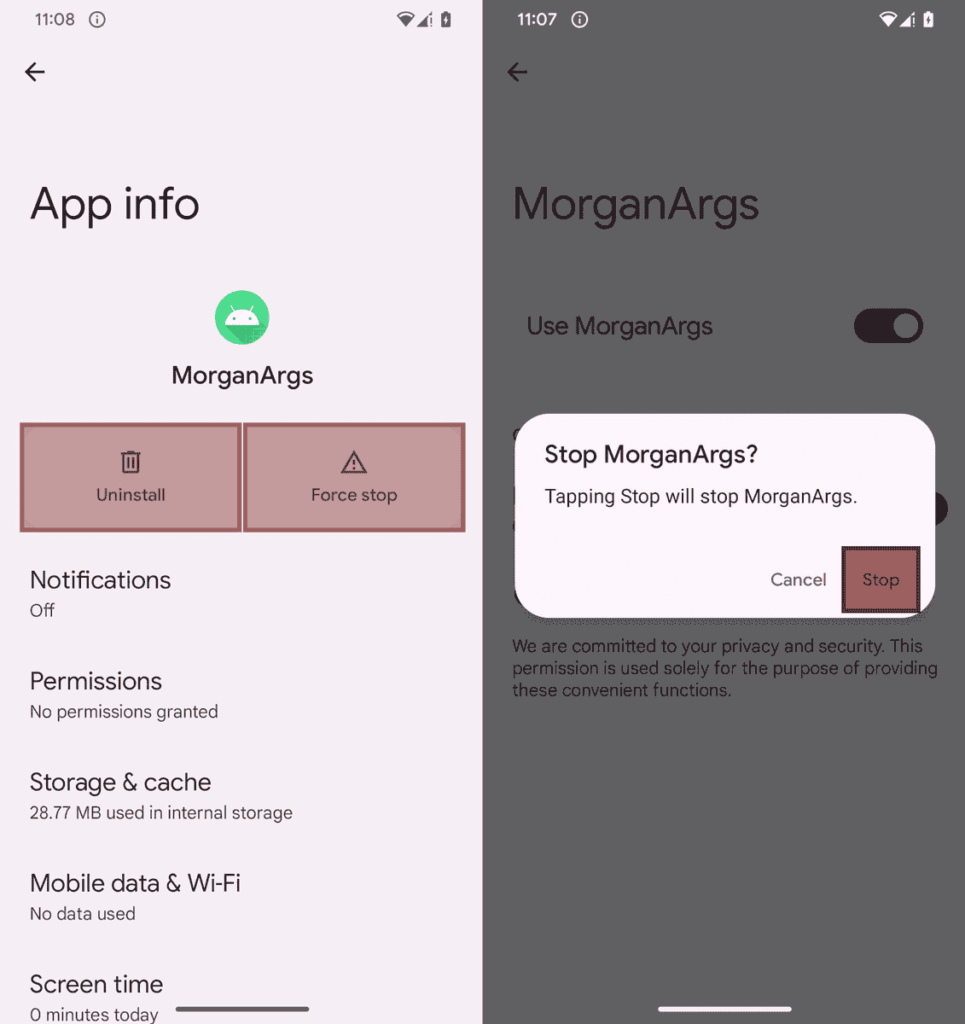
- Retrieval of Gemini API key for persistence module
The anti-deletion mechanism is based on an invisible interception technique. According to the ESET report: “When the user attempts to uninstall the payload or disable accessibility services, the malware overlays transparent rectangles on specific areas of the screen – notably above buttons containing substrings such as stop, end, clear and Uninstall. These overlays are invisible to the user but intercept interactions.” The practical result: the user thinks he’s pressing “Uninstall”, but his tapping is captured by the invisible rectangle, with no effect. ESET researchers visualized these rectangles by activating a debug flag left in the code, but on a real device they are completely imperceptible. The only way to uninstall PromptSpy is to restart the device in safe mode, where third-party applications are neutralized.
PromptSpy, an evolution of the VNCSpy family
PromptSpy is a direct evolution of VNCSpy, an Android family identified a few weeks earlier. In February 2026, ESET discovered two versions of a previously unknown Android malware family. Two waves of filings on VirusTotal mark the history of this family: three samples of VNCSpy submitted from Hong Kong on January 13, 2026, then, less than a month later on February 10, four samples of a more advanced variant filed this time from Argentina (the same ones that led to the identification of PromptSpy).
Both variants share the same technical foundation: a VNC component offering operators complete remote control as soon as the victim has granted access permissions. The difference lies in what ESET describes as “AI-assisted user interface manipulation”, absent from VNCSpy, which is PromptSpy’s distinctive contribution to ensuring its persistence.
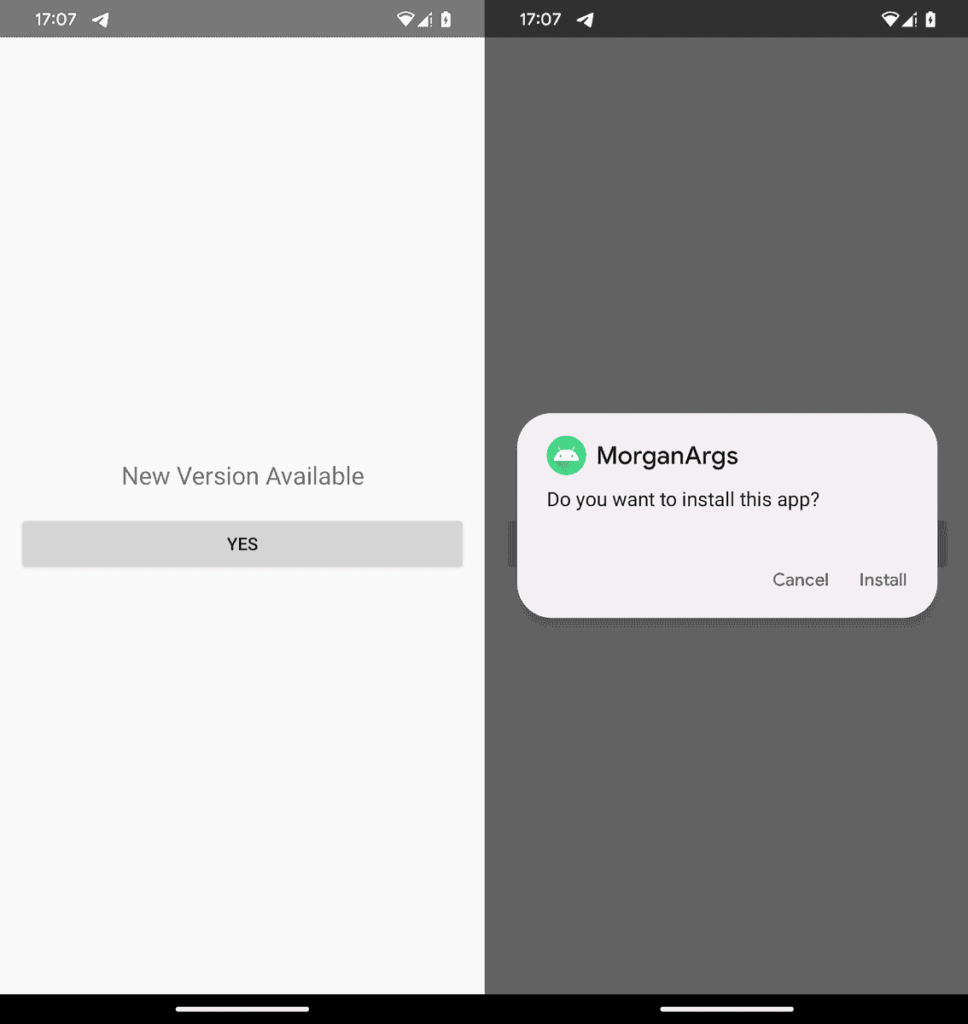
In terms of distribution, the dropper embeds the PromptSpy payload(app-release.apk) in its assets directory. Once launched, it presents the victim with what looks like a mandatory application update: in reality, it’s the manual installation of the payload that the victim is asked to validate.
Proof-of-concept or active threat?
A key question remains concerning PromptSpy’s operational status. ESET researcher Lukas Štefanko confirmed to BleepingComputer: “We have yet to see any sign of the PromptSpy dropper or its payload in our telemetry, which could mean that these are only proofs-of-concept.”. The existence of a dedicated distribution infrastructure, active distribution domain, fake banking site, suggests that it cannot be ruled out that the malware has been or is still in circulation.
Lukáš Štefanko himself presents the key points in the following video.
PromptSpy has never been distributed via Google Play, but exclusively through a dedicated website. As a partner of the App Defense Alliance, ESET shared its findings with Google. A Google spokesperson confirmed to The Hacker News that no applications containing PromptSpy have been detected on Google Play to date. Regarding user protection, he added: “Android users are automatically protected against known versions of this malware by Google Play Protect, enabled by default on Android devices running Google Play Services. Google Play Protect can alert users or block applications with known malicious behavior, even when they come from sources outside Play.”
Generative AI in malware: a trend that’s taking hold
ESET’s conclusion is straightforward: “PromptSpy shows that Android malware is starting to evolve in a worrying way. By relying on generative AI to interpret on-screen elements and decide how to interact with them, the malware can adapt to virtually any device, screen size or interface layout. Instead of hard-coded taps, it simply entrusts the AI with a snapshot of the screen and receives precise step-by-step instructions in return.” This paradigm shift, from static scripting to real-time contextual intelligence, is what sets PromptSpy apart from all that has gone before.
Future malware could exploit this approach for far more critical functions: automated navigation in banking applications, adaptation of behavior to the detected user profile, dynamic generation of evasion techniques, or communication with victims via AI-generated messages for targeted social engineering attacks. This scenario is not theoretical: in early February 2026, Google Threat Intelligence reported that state groups are already exploiting Gemini in every phase of their operations, from reconnaissance to post-compromise actions. The malicious use of public AI models is becoming a documented fact, not a hypothesis.
Faced with this development, three reflexes significantly reduce the risk: download exclusively from the Google Play Store, never grant accessibility services to an application of dubious origin, as this permission gives almost total control over the device, and be wary of any application that presents itself as an update by asking to install an additional APK, a typical dropper pattern.
When malware learns to adapt, so must defenses
Organizations and advanced users should consider deploying Mobile Endpoint Detection and Response (Mobile EDR) solutions capable of identifying suspicious behavior such as communications with command and control servers, or automated interface manipulation via accessibility services. Network traffic monitoring can also reveal communications with the Gemini API when they originate from unusual applications, although this detection requires in-depth inspection of encrypted traffic. Finally, keeping Android and all applications up to date with the latest security patches remains a fundamental measure, as system vulnerabilities can facilitate the initial installation of malware even when the user explicitly refuses permissions.
The cybersecurity industry will need to develop specific countermeasures for this new generation of threats. Traditional approaches based on signatures or fixed behavioral patterns may prove insufficient in the face of malware capable of adapting its behavior according to context. Detection solutions will themselves need to integrate AI to identify subtle anomalies in user interface interactions or communication patterns with AI services. Collaboration between AI model providers and security researchers also becomes essential to identify and block malicious uses while preserving legitimate use cases. PromptSpy may still be limited in its actual deployment, but it is thus a case study that will probably mark the beginning of a new era in the evolution of mobile malware, where adaptability gradually replaces static coding as the guiding principle of malware development.
Source: ESET
ESET WeLiveSecurity: PromptSpy ushers in the era of Android threats using GenAI
BleepingComputer : PromptSpy is the first known Android malware to use generative AI at runtime
The Hacker News: PromptSpy Android Malware Abuses Gemini AI to Automate Recent-Apps Persistence
Google Threat Intelligence : GTIG AI Threat Tracker: Distillation, Experimentation, and (Continued) Integration of AI for Adversarial Use
