In 2025, phishing e-mails containing a malicious QR code rose from 47,000 in August to 249,000 in November, a five-fold increase in the space of three months. This is not a statistical anomaly: it reflects the massive and accelerated adoption of a technique that architecturally bypasses email defenses without having to fight them. Quishing isn’t quite a variant of phishing, it’s a calculated response to a structural limitation of security systems, and the figures show that it’s working.
Table des matières
ToggleWhat is quishing?
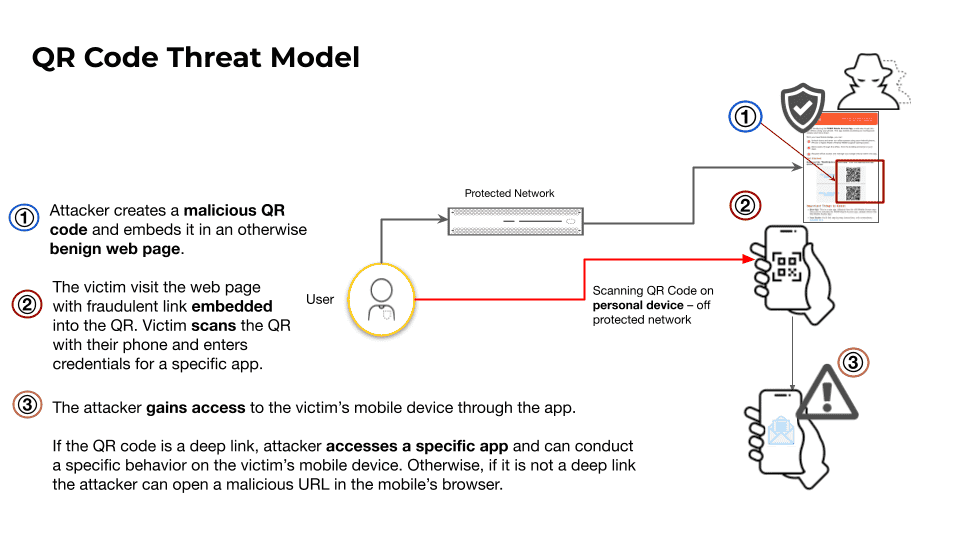
Quishing is a contraction of “ QR code ” and ” phishing “. It refers to a phishing technique in which a malicious QR code replaces the traditional hypertext link. The mechanics are straightforward: an attacker embeds a QR code in an email, document or physical medium; the victim scans it with his or her smartphone; the malicious payload is executed from the mobile device, outside any controlled security perimeter.
What fundamentally distinguishes quishing from classic phishing is an inherent property of QR codes: they hide their destination until the moment they are scanned. A hypertext link can be inspected, hovered over and analyzed before being clicked. A QR code image, on the other hand, escapes this inspection entirely, as email security gateways examine URLs in plain text, not images encoded in a matrix of pixels.
What most users don’t realize is thata QR code can do much more than open a web page. It can trigger a payment, link a new device to an e-mail account, inject a calendar invitation, register a contact or connect the phone to a WiFi network controlled by an attacker. This mismatch between user expectation and technical reality is the structural weakness that today’s campaigns methodically exploit. The standardization of QR codes during the COVID-19 pandemic installed a trust reflex that is now turning against users: paying a bill, joining a WiFi network, accessing a restaurant menu have become gestures as natural as clicking on a link.
An architectural blind spot that traditional defenses can’t fill
Quishing doesn’t try to fight email defenses, it bypasses them by changing the terrain. The malicious email arrives in a protected inbox, but execution takes place on a personal smartphone, in a browser outside the corporate perimeter, with security controls generally inferior to those of a managed workstation. Every major vendor acknowledges this limitation in its own documentation.
Traditional detection systems rely on pattern recognition and similarity analysis between campaigns. However, quishing campaigns have an average Jaccard similarity of just 0.209, well below the 0.30 threshold at which pattern-based detection becomes effective. For targeted campaigns, this similarity even drops to 0.134. This level of dissimilarity presents defenders with an insoluble dilemma: an aggressive setting generates a catastrophic false positive rate, while a cautious setting accepts an equally catastrophic non-detection rate. The Mimecast recommendation itself advocates a 90% detection threshold for QR analysis, de facto accepting a 10% non-detection rate, as higher sensitivity overwhelms analysts with false positives.
Documented progress over three years
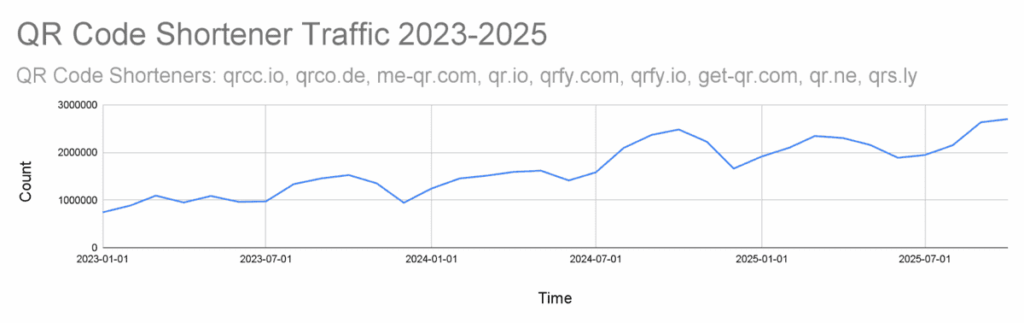
Palo Alto Networks Unit 42 telemetry records an average of 75,000 QR code detections per day in its web crawlers, 15% of which lead to malicious destinations, i.e. over 11,000 daily detections of malicious QR codes. Over three years, traffic to QR code shortening services increased by 55% between the first half of 2023 and the first half of 2024, and by a further 44% between the first half of 2024 and the first half of 2025.
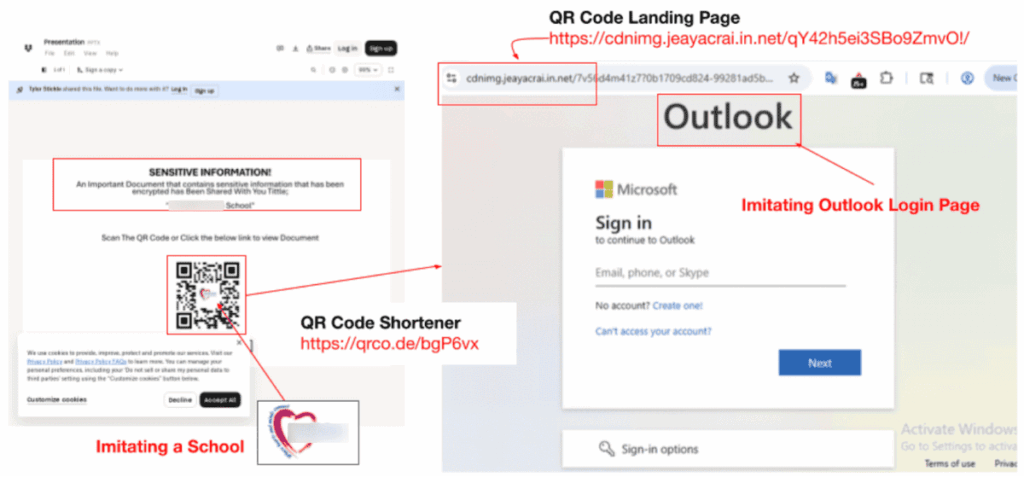
Statistics compiled by Keepnet Labs confirm this trajectory: in 2025, 12% of all phishing attacks will contain a QR code, compared with 0.8% in 2021. The most significant increase can be seen in raw volumes: phishing emails based on QR codes rose from around 47,000 in August 2025 to over 249,000 in November 2025. More than half of these campaigns imitate the Microsoft environment, a logical choice given the prevalence of Microsoft 365 in targeted organizations.
Sectoral concentration of attacks
Sector analysis reveals a consistent targeting logic. As far as compromised QR code shorteners are concerned, financial services account for 29% of detections, despite generating just 4.8% of global traffic for these services, an overrepresentation that signals clear intentionality. High-tech (19%) and wholesale/retail (14%) complete the picture.
The picture is different for phishing emails containing malicious QR codes: the energy sector leads with 29% of incidents detected in a sample of over 1,000 infected emails, followed by manufacturing, insurance, technology and financial services. This disparity between the two analyses suggests that attackers are adapting their vectors according to sector: QR shorteners for financial institutions, targeted emails for critical infrastructure operators.
Three documented attack vectors
The Palo Alto Networks Unit 42 study identifies three distinct vectors, each exploiting a specific QR code capability to move the malicious payload to the victim’s device, outside any controlled security perimeter.
1. QR code shorteners
QR code shorteners are the most widespread vector. These services transform a static image into a dynamic endpoint: the redirection destination can be changed at will, even after a malicious e-mail has already been delivered to inboxes. The good reputation of shortening platforms is enough to bypass blacklists. Unit 42’s telemetry identifies qrco. de, me-qr. com and qrs. ly as the services most used in malicious campaigns, with the latter accounting for 7.3% of observed malicious URLs, a notable emergence compared to previous Anti-Phishing Working Group reports.
Redirection chains further complicate detection. Attackers chain together two to three trusted services such as AWS S3, Cloudflare Workers, Google Cloud, and sometimes intersperse a CAPTCHA page before reaching the final phishing page, filtering out automated analysis tools. The ephemeral nature of the infrastructure is itself a tactic: 67% of malicious domains are registered within 30 days of use, with attackers launching an average of two to three attacks per domain before pivoting. What’s more, 68% of attacks use infrastructure hosted by cloud providers renowned for their multi-stage redirection chains, making it almost impossible for an email gateway to reliably reach the final destination.
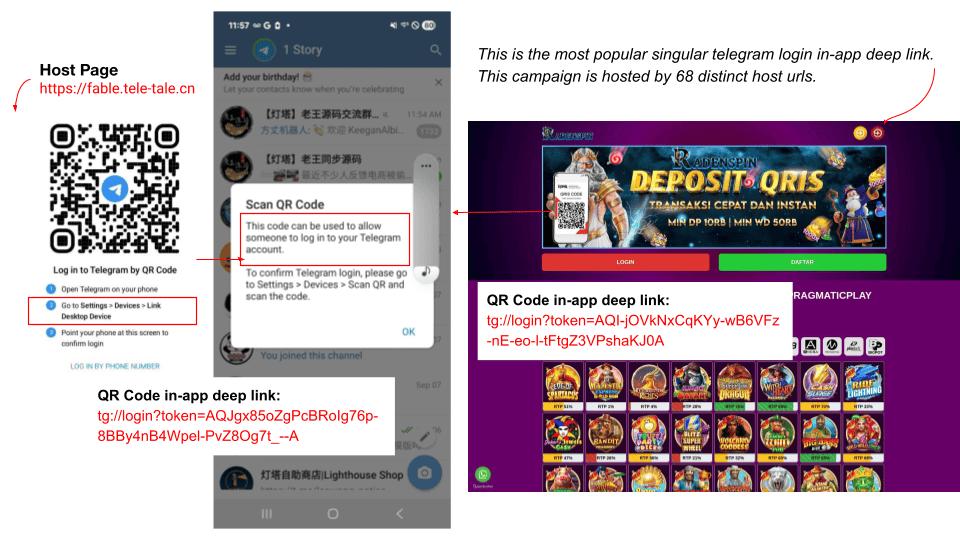
2. Application deep links
Deep application links account for around 3% of QR codes detected in telemetry, but represent a technically more sophisticated and still largely underestimated threat. These special links open specific content within mobile applications and trigger specific functions without ever passing through a web browser, making them invisible to standard web security tools. Their effective detection requires a mobile sandbox environment with the target application installed, a major operational constraint for the vast majority of security teams.
Telegram accounts for 44.7% of the malicious deep links identified. Researchers identified over 35,000 QR codes containing Telegram deep links, 97% of which use the login function: one designed to link a new device to an existing account. This link grants the QR code creator full access to the account, enabling messages to be sent in the victim’s name and conversation history to be exfiltrated. Around one in five Telegram QR codes leading to a login page is considered malicious. Signal and WhatsApp are targeted by the same mechanism: Russian-aligned actors have notably documented the exploitation of this vector to compromise Signal accounts of Ukrainian users. Beyond account takeover, deep links enable other scenarios: financial fraud via payment applications with pre-filled recipient and amount (Bitcoin, Ethereum, MetaMask, WeChat Pay, Alipay), calendar poisoning via vCalendar invitations containing phishing links, injection of malicious vCard contacts, or automatic connection to a WiFi network controlled by the attacker.
3. Direct APK download
Direct APK downloads exploit the trust established around application download QR codes to distribute Android Package Kit files hosted directly on attackers’ servers, completely bypassing the security controls of official app stores. Unit 42 identified 59,000 page detections distributing 1,457 distinct APK files in this way. Gambling apps make up the majority of these distributions, hosted on thousands of unique URLs and requesting worrying Android permissions: precise location, phone status, camera access, reading and writing to external storage, installation of additional packages. Other applications found, presented as optimization tools or educational social networks, requested audio recording and account authentication, with several antivirus editors detecting them as suspicious or malicious.
Fancy QR codes: escape by design
The most recent technical breakthrough documented in security literature concerns “fancy QR codes”, visually stylized QR codes whose design disrupts detection mechanisms even before URL analysis can intervene. In contrast to standardized black-and-white grids, these codes adopt rounded, stretched or recolored modules, integrate logos at their center and blend background images into the code matrix. These modifications preserve scanning capacity while breaking the structural assumptions on which existing detection tools, which estimate module size and position on the basis of standardized grids, are based. According to reports published in 2024 by Insikt Group and ReliaQuest, 22% of QR code attacks were already quishing, marking a 248% increase on 2023.
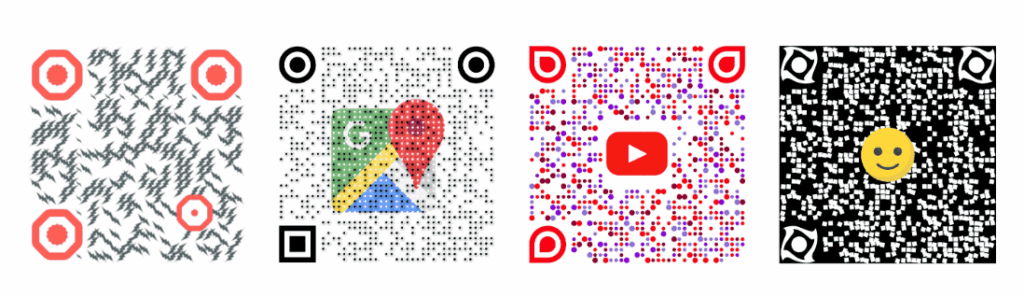
Researchers at Deakin University have demonstrated that these modifications are sufficient to bypass conventional detectors, and in response have developed ALFA (Anti-phishing Layer for Fancy QR code Attacks), a method that assesses the legitimacy of a QR code by analyzing its graphic structure before any access to its content. Rather than looking for where the code leads, the system determines whether its design presents suspicious characteristics, a complete inversion of the detection paradigm based on URL reputation. ALFA is based on the extraction of 24 structural features subjected to a pre-trained machine learning model, and integrates a complementary tool called FAST which analyzes and restores the four types of standardized patterns present in any QR code. Experimental results show a false-negative rate of 0.06%, with an average processing time of 3.4 seconds per code. The approach is still in the experimental phase, but it illustrates the direction that defense must take: treating the QR code no longer as a simple link, but as a digital object whose structure can betray hostile intentions.
These stylized codes are not confined to e-mails. When affixed to physical equipment or integrated into printed media, they enjoy an additional psychological advantage: a QR code with a neat design and recognizable logo inspires more trust than a black-and-white grid, even though this visual sophistication can mask precisely what it appears to legitimize.
Emerging evasion techniques
In January 2026, 12% of detected quishing attacks used QR codes based on ASCII text, textual representations of the matrix rather than images. Detection systems designed to identify and extract pixelated QR codes cannot recognize these textual forms, creating an additional blind spot in existing detection chains.
Another notable development is the imitation of security language. Campaigns faithfully reproduce OAuth and multi-factor authentication terminology to neutralize user distrust. As tools for abusing the OAuth device flow become more accessible, they will create attacks that destination URL analysis cannot detect, as these attacks exploit legitimate security protocols to mask their intentions.
The integration of large language models into the attack chain represents a distinct qualitative evolution. The accompanying texts for quishing lures are now automatically generated, grammatically flawless and tailored to individual targets on a large scale. The mistakes and awkward wording that traditionally served as warning signals for vigilant users are gradually disappearing from the threat landscape.
What the data reveal about human exposure
Only 36% of quishing incidents were correctly identified and reported by their recipients. This detection gap leaves the majority of active campaigns with no feedback to security teams, further delaying incident response.
68% of attacks specifically targeted mobile users in 2025, a logical choice: smaller screens make URL inspection difficult, and the vast majority of users scan a QR code without checking its destination. Executives were 40 times more likely to fall victim to quishing attacks than the average employee, a concentration that can be explained by access to sensitive information and the return on investment represented by the compromise of an account with decision-making power. The retail sector also has the highest non-detection rate: the familiarity of employees and customers with QR codes, for payments, loyalty programs and promotions, paradoxically translates into reduced vigilance.
Identity theft is the dominant objective: 89.3% of incidents were aimed at stealing login information. Access to a compromised corporate mailbox opens the door to compromised business email attacks, data exfiltration and lateral movement within the organization’s systems. The data also show that targeted training improves detection capability by 87% within three months of deployment, a result which, when set against the current non-detection rate, underlines the scale of the awareness deficit.
Reduce exposure surface
The architectural limitations of email defenses against quishing cannot be overcome by existing technical solutions alone. Reducing the surface of exposure relies on a combination of complementary measures.
Training teams in the reality of QR codes means going beyond classic phishing to cover the full range of actions that a QR code can trigger: payment, device linking, application installation, calendar injection. This training must include fancy codes, whose careful design is no guarantee of legitimacy. Establishing a strict scanning policy means prohibiting the scanning of QR codes received by email from unknown senders, or in contexts imitating OAuth or multi-factor authentication processes.
On a technical level, email solutions must be able to analyze QR codes and track redirection chains, including those passing through reputable cloud providers, and detect QR representations in both image and ASCII modes. Deploying a Mobile Threat Defense solution for devices accessing corporate resources, whether personal or professional, enables analysis of network traffic generated after scanning. SIEM alerts should be configured to detect unusual links from new devices to corporate e-mail accounts outside business hours, or from unusual geolocations. Finally, blocking domains registered for less than 30 days and restricting access to QR shorteners documented as abused in network filtering policies mechanically reduces the reach of a significant proportion of active campaigns.
The terrain has shifted, and defenses must follow
Quishing illustrates an attack logic that shifts execution where defenses cannot follow. The three vectors documented by Unit 42, shorteners, deep links and APK, share this property: they shift the malicious payload to a personal mobile device, beyond any organizational control. Fancy QR codes add a layer of visual evasion that even precedes URL analysis. The ALFA approach, still experimental, signals the direction in which detection must evolve: analyze the object before its content. In the meantime, the combination of clear organizational policies, targeted training and technical controls tailored to mobile vectors remains the most robust response available to a threat that evolves faster than signatures.
Sources :
- Palo Alto Networks Unit 42: Phishing on the Edge of the Web and Mobile Using QR Codes
- Keepnet Labs: QR Phishing Statistics: Quishing Trends
- Deakin University: ALFA: A Safe-by-Design Approach to Mitigate Quishing Attacks Launched via Fancy QR Codes
- Help Net Security: QR codes are getting colorful, fancy, and dangerous
- Continuity Insights: QR Code Phishing Is Evading Email Security
