Figures published at the end of February 2026 by Chainalysis paint a paradoxical picture of the ransomware economy in 2025: global payments have fallen, the rate of victims giving in to attackers’ demands has reached an all-time low, and yet ransomware has never struck so hard or so often. This paradox is worth examining.
Table des matières
TogglePayment rates plummet while attacks explode
In 2025, on-chain payments (i.e. recorded directly on the blockchain, and therefore traceable by transaction analysis) linked to ransomware stood at around $820 million, down 8% on the $892 million estimated for 2024. Chainalysis points out, however, that this figure is set to approach 900 million as new payments are awarded, as was the case for 2024, whose initial estimate was 813 million.
Even more striking is the trend in payment rates: in 2025, only 28% of identified victims paid a ransom, compared with 62.8% in 2024 and 78.9% in 2022. This decline has been part of a continuous trend for four consecutive years, and has even accelerated with each passing quarter. Coveware’s data, drawn from its own intervention files, confirms and amplifies this observation: the payment rate fell to 23% in the third quarter of 2025, then to around 20% in the fourth quarter, levels never seen before.
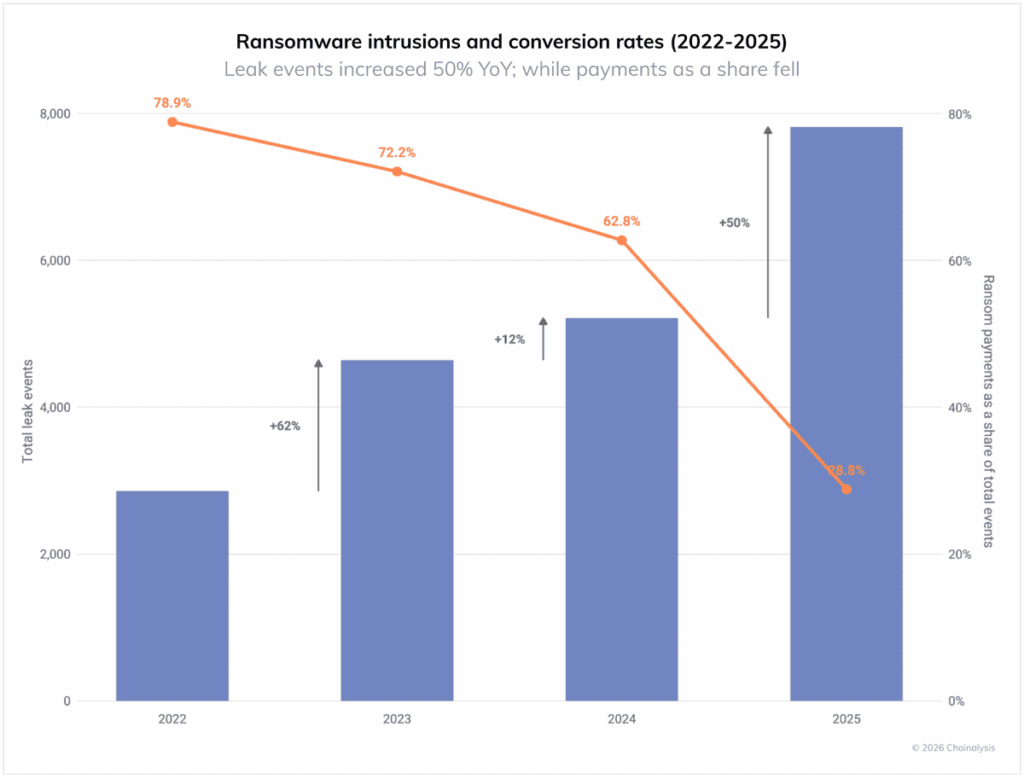
This contraction in payments comes against a backdrop of amassive increase in attacks, which have never been so numerous. The number of victims claimed on leak sites rose by 50% year-on-year in 2025. As Corsin Camichel, founder of eCrime .ch, sums up: ” We ‘ re seeing a structural shift in targeting, with fewer headline-grabbing major intrusions and more volume focused on small and medium-sized businesses. The assumption is simple: smaller victims pay faster. However, Chainalysis data shows a downward trend in payments despite a record number of public complaints. ” The logical consequence of this discrepancy between the volume of attacks and the volume of payments is that cyber attackers are seeing their returns melt away, even as they redouble their efforts.
Several factors combine to explain this trend:
- improved incident response capabilities and growing regulatory pressure ;
- coordinated law enforcement action against operators and their infrastructure;
- the fragmentation of the RaaS market into a multitude of smaller, more independent groups;
- in some cases, ransomware – as was the case with VolkLocker – features design flaws that enable decryption by experts specialized in recovering ransomware-encrypted data.
Ransomware rises despite falling payments
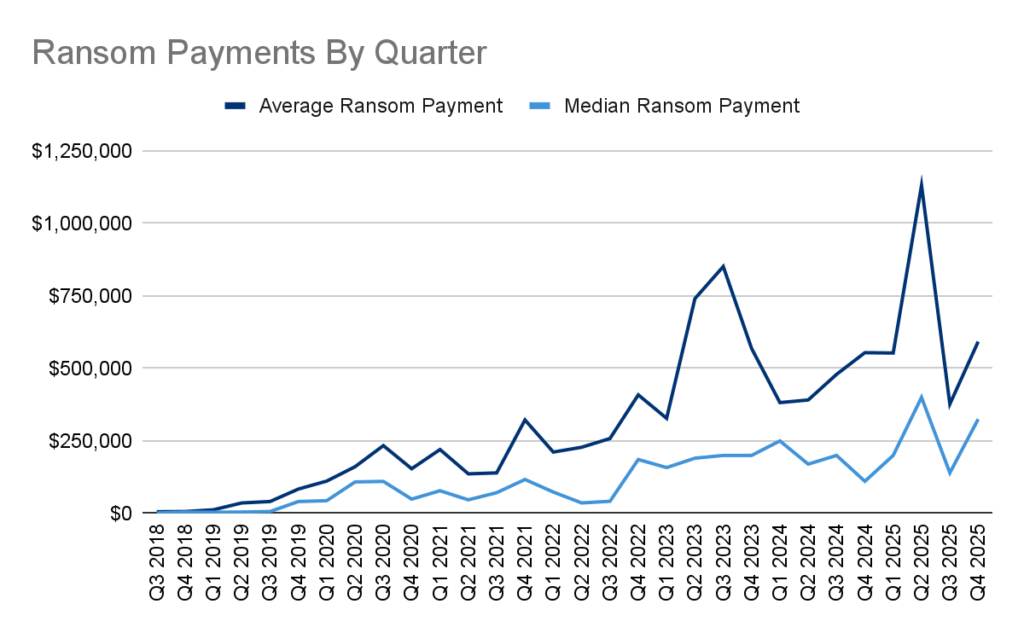
The overall drop in revenue masks a more nuanced reality: the median ransom rose by 368% between 2024 and 2025, from $12,738 to $59,556. This leap reflects a concentration of efforts on higher-potential victims, capable of paying more.
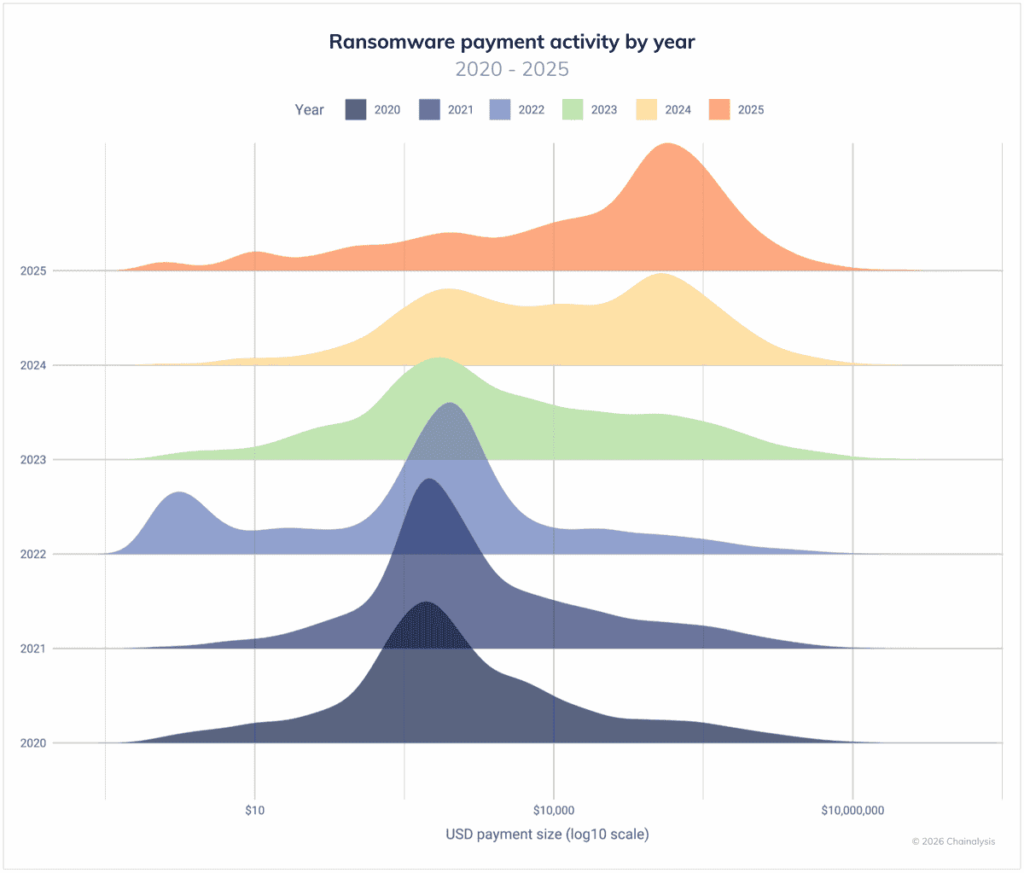
Coveware’s data for Q4 2025 points in the same direction, although it measures a different perimeter (cases handled directly by the company, which include larger organizations): the average payment reached $591,988 (+57% on Q3) and the median $325,000 (+132%). The marked divergence between average and median reflects a reality well known to experts: a few large-scale settlements, linked to incidents where business stoppages could not otherwise be resolved, pull the average upwards without reflecting the general case.
This shift towards medium-sized and larger targets is also well documented: the Akira and Qilin groups, which between them accounted for 44% of all attacks recorded in the third quarter of 2025, have clearly repositioned their activity towards SMEs deemed more likely to pay. The median size of victim companies in the fourth quarter of 2025 was 200 employees, marking a clear decline on the previous quarter, with a high concentration of attacks in structures with 11 to 100 employees.
The most significant cyberattacks of 2025: an alarming balance sheet
The magnitude of these statistics is illustrated by the major cyber incidents of 2025. The attack on Jaguar Land Rover brought international production lines to a halt, generating losses estimated at almost £2 billion, a record in the UK’s economic history. For its part, Marks & Spencer, a target of the Scattered Spider group, suffered prolonged disruption and a significant depreciation in its stock market value. Interlock ‘s offensive against DaVita, the American dialysis specialist, exposed the sensitive data of 2.7 million patients. At the same time, CL0P exploited a zero-day vulnerability in Oracle E-Business Suite to compromise a hundred companies in just a few weeks.
Beyond the ransom, the real consequences of these attacks – business interruption, financial losses, damage to reputation – often far exceed the amount demanded by cybercriminals. The ransomware actors are relentless in their reactivity. Rather than targeting a particular sector, they systematically take advantage of security flaws, faulty configurations or recently revealed vulnerabilities to orchestrate their attacks.
Unencrypted exfiltration literally no longer pays
For years, double extortion – combining data encryption with the threat of publication of stolen information – has redefined the landscape of ransomware cyberattacks. Today, this model remains the most formidable. But a fundamental trend is running through it: one of its pillars is crumbling. Campaigns based solely on data exfiltration, without encryption, are rapidly losing their ability to monetize the threat.
Organizations have now understood the real cost-benefit ratio of paying to “delete” stolen data. Paying does not remove legal notification obligations, does not significantly reduce the risk of litigation, and does not prevent attackers from retaining, selectively disclosing or reusing data. Coveware goes further, pointing out that even engaging in dialogue with cybercriminals represents a growing risk in itself, with malicious actors no longer hesitating to resort to SWATting: sending armed intervention units to executives’ homes to force them to pay.
The result? In Q3 2025, Coveware measured that the payment rate in cases ofexfiltration alone (without encryption) had fallen to 19%, an all-time low for this sub-category. In Q4, this rate rose slightly to ~25%, but remains structurally low, well below historical norms. The signal is clear: threatening to publish data without having encrypted it is no longer convincing.
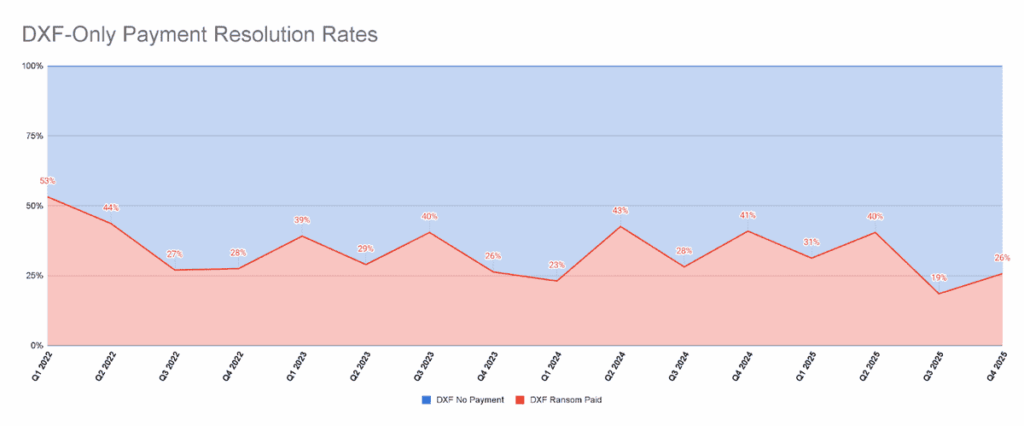
It’s no coincidence that Akira (14% of attacks) and Qilin (13%) dominate the ranking of the most active groups in Q4 2025: both base their model on encryption as their main lever. Coveware even anticipates a strong comeback for pure encryption – groups that had relied on exfiltration alone may well revert to what has always worked.
Digital identity, the first vector of intrusion
Payment statistics tell only part of the story. To understand why attacks are exploding despite falling revenues, we need to look at the gateway, and that gateway is very often identity.
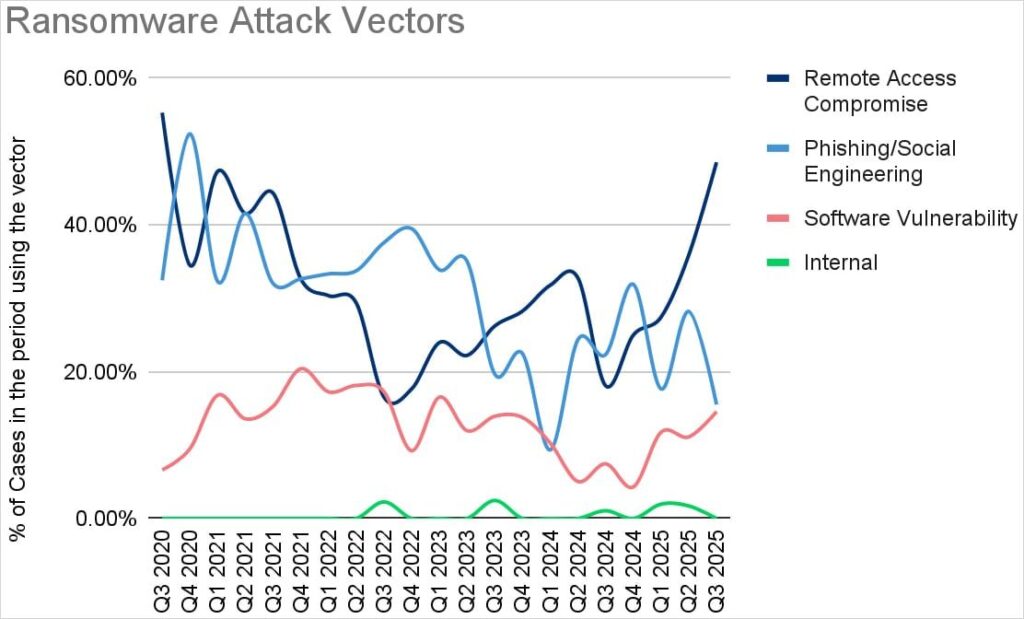
In the third quarter of 2025, compromised remote access accounted for more than half of all incidents observed by Coveware: insecure VPNs, exposed cloud gateways, SaaS integrations, non-renewed OAuth tokens. This quarter also highlighted a worrying convergence: social engineering has merged with remote access compromise. Attackers are no longer trying to break into systems, they’re convincing humans to open the door for them, by impersonating IT support, manipulating a real-time authentication session, or bypassing an otherwise robust MFA.
It is precisely this mechanism – compromising identity rather than infrastructure which is at the heart of the campaign by the Scattered LAPSUS$ Hunters alliance, including the ShinyHunters group, led a large-scale vishing offensive against the SSO accounts of over 100 global enterprises in 2025, managing to bypass even the most robust multi-factor authentication systems.
Initial Access Brokers (IABs), the discreet cogs in an industrialized ecosystem
Ransomware relies on an ecosystem of specialized criminal services, of which Initial Access Brokers (IABs ) are a key link. These players specialize in compromising systems and reselling access to ransomware operators, a model found at the heart of the Scattered LAPSUS$ Hunters coalition, some of whose members act precisely as large-scale initial access providers before moving on to extortion.
In 2025, IABs received at least $14 million in on-chain payments, a stable amount compared to 2024, representing just 1.7% of total ransomware payments. The return on investment for buyers is therefore massive. Chainalysis also points out that peaks in IAB activity are a leading indicator: significant increases in IAB transactions precede peaks in ransom payments and new victim publications by around 30 days.
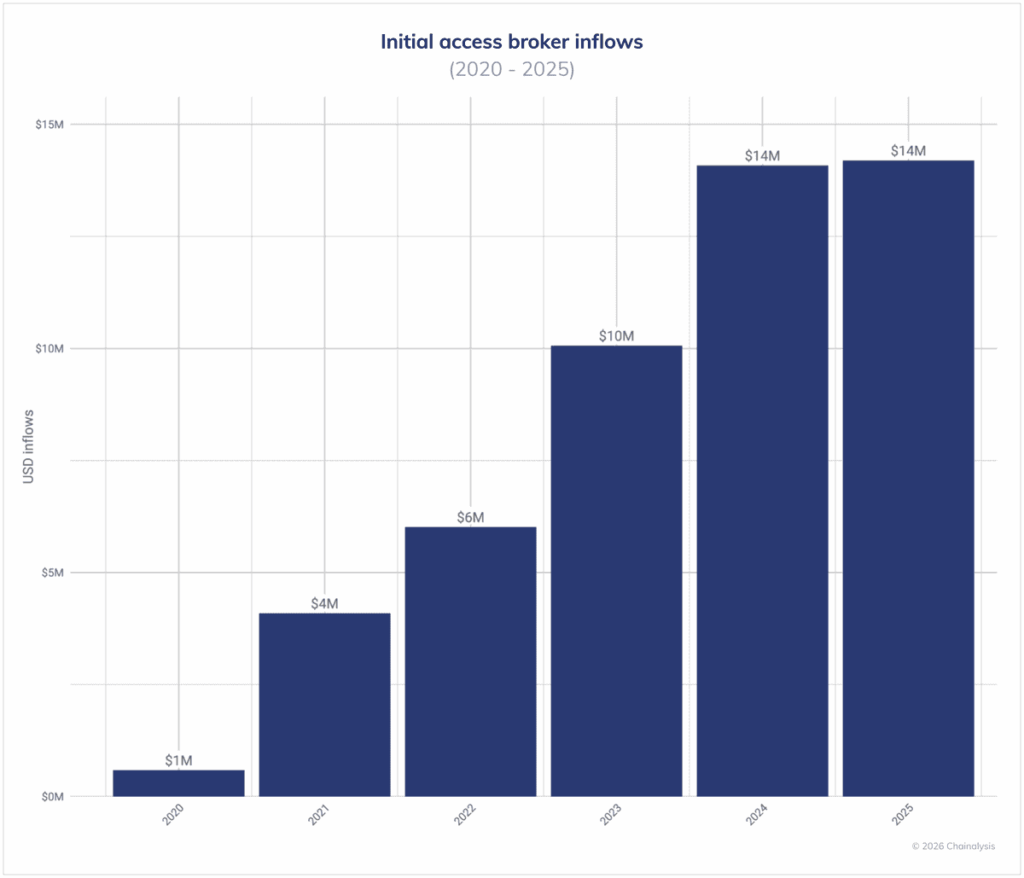
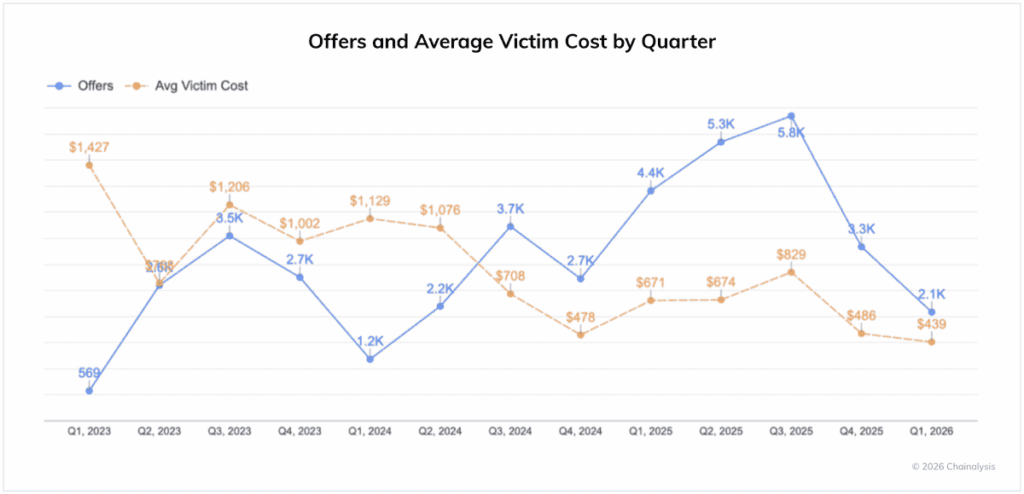
The access market is also in the process of industrialization. According to Darkweb IQ, the average price of a network access dropped from $1,427 in Q1 2023 to $439 in Q1 2026. This deflation is explained by automation, the use of AI-assisted tools and the oversupply generated by infostealer logs (databases of credentials stolen by malware specialized in the silent extraction of credentials, etc.) . A divide has opened up in this market: generic access is being sold off, while high-privilege access (domain control, administrator access) remains at premium prices.
Fragmentation of the RaaS market: more groups, fewer giants
The RaaS landscape has changed radically. Checkpoint counted 85 active extortion groups in the third quarter of 2025, an unprecedented figure against a backdrop of collapsing market concentration: the ten most active groups now accounted for just 56% of published victims, compared with 71% at the start of the year. The space once dominated by a few major platforms such as LockBit, dismantled during Operation Cronos in early 2024, has fragmented into a nebula of smaller, more independent and harder-to-trace players: 47 of these 85 groups claimed fewer than ten victims, a sign that affiliates are now operating solo, with no shared infrastructure or known brand.
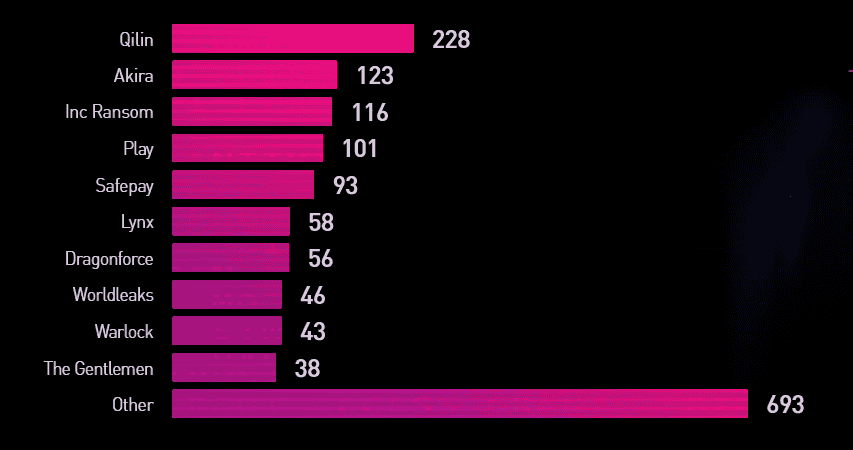
This fragmentation has ambivalent effects. On the one hand, it contributes to the decline in overall revenues and complicates the rise of high-impact groups. On the other, it redistributes affiliates rather than eliminates them: the closure of RansomHub in April 2025 directly propelled Qilin, which doubled its rate to 75 victims per month in the third quarter, compared with 36 at the start of the year. As Corsin Camichel rightly puts it in the Chainalysis report: disrupting a group no longer guarantees ecosystem-wide impact, and the most effective pressure points are now upstream, on the side of IABs and tools shared between players.
Geographically, leak sites are still concentrated in developed economies: the United States remains by far the most frequent target, ahead of Canada, Germany and the United Kingdom. The sectors most affected are manufacturing, financial and professional services.
Dismantling infrastructure rather than individual groups
Faced with this fragmentation, the authorities have evolved their doctrine. In 2025, repressive actions increasingly targeted shared service providers, bulletproof hosts (hosting that deliberately tolerates criminal activity), residential proxy networks and loaders, which feed the entire ecosystem independently of the groups that exploit them. Operation Endgame, led by Europol and the FBI, was thus extended in May 2025 to neutralize several families of malware used as entry vectors in numerous ransomware campaigns, while OFAC sanctions have targeted hosts such as AEZA Group and Zservers, associated with LockBit.
What the figures mean in concrete terms
All this data points to several areas of attention for organizations:
- improved backups and incident response are measurable: this is the primary reason why payment rates are falling;
- paying ransomware to recover stolen data offers no real guarantee: data is frequently retained, resold or reused for later re-extortion;
- SMEs are the main target: 69% of cases observed by Coveware in the fourth quarter of 2025 concerned organizations with fewer than 1,000 employees;
- digital identity is now the primary intrusion vector: compromising remote access (VPN, RDP, OAuth tokens, SaaS access) is the dominant vector, often made possible by obsolete credentials or insufficient access hygiene.
As Chainalysis points out, the decline in apparent revenues does not mean that the threat has weakened: ransomware is adapting, diversifying its extortion levers and continuing to produce major operational and economic effects.
Are you a victim of ransomware? Contact our 24/7 assistance service. We provide an exclusive technical response to ransomware incidents, to help you recover your data and get back to business quickly.
Sources :
Chainalysis: Crypto Ransomware: 2026 Crypto Crime Report
BleepingComputer: Ransomware payment rate drops to record low as attacks surge
BleepingComputer: Ransomware profits drop as victims stop paying hackers
Coveware: Mass Data Exfiltration Campaigns Lose Their Edge in Q4 2025
Coveware: Insider Threats Loom while Ransom Payment Rates Plummet
The Record: Ransomware payments dropped in 2025 as attack numbers reached record levels
Check Point Research: The State of Ransomware in Q3 2025
The Hacker News: VolkLocker Ransomware Exposed by Hard-Coded Master Key Allowing Free Decryption
