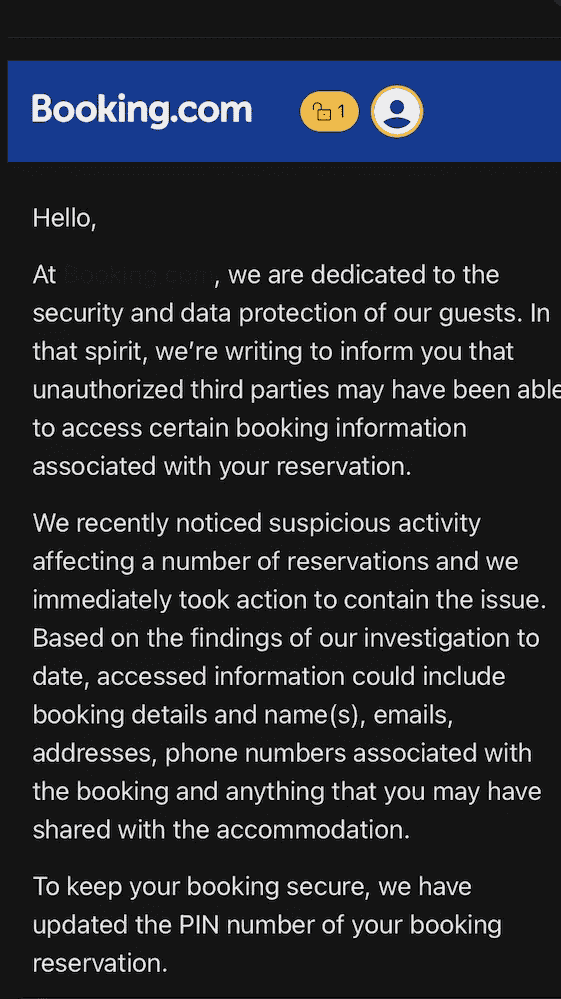
Booking.com customer reservation data is in the hands of attackers, and is already being used for targeted phishing campaigns. On April 13, 2026, the online booking platform, which lists over 30 million accommodations worldwide, confirmed that unauthorized access had allowed third parties to view personal information associated with certain bookings. Booking has reset the PIN codes of the reservations concerned and notified customers by email. The incident is contained, according to the Dutch company.
But the timeline of events tells a different story. At least one user reported on Reddit that he had received a phishing message via WhatsApp containing his actual booking data, two weeks before receiving the official notification. This time lag suggests that the compromised data was circulated and exploited long before customers were alerted. For those affected, the main risk is not the intrusion itself, but what follows: scam attempts of a precision difficult to distinguish from legitimate communications.
The data exposed and the incident’s grey areas
According to the notifications sent to customers, the data accessible to the attackers included booking details, full names, email addresses, phone numbers and “anything you may have communicated to the establishment“, read the emails received by customers. When questioned by BleepingComputer, Sage Hunter, the company’s communications manager, confirmed the incident: “We recently became aware of suspicious activity involving unauthorized third-party access to some of our customers’ booking information. As soon as we detected these activities, we took steps to remedy the problem. We updated the PIN code associated with these bookings and informed our customers.” The platform confirmed to The Guardian that financial data (payment or credit card information) had not been compromised.
However, the company did not reveal the number of customers affected, the regions concerned, the precise chronology of the intrusion, or the technical vector used by the attackers. Nor did it specify whether its own systems had been compromised or whether access had been gained by other means, a distinction that would help determine the true scale of the incident. TechCrunch reports that the company also refused to answer specific questions about the number of people affected.
A further detail fuelled the confusion: notifications were only sent by email from the address noreply@Booking .com, with no corresponding alert in the mobile application. Many users initially suspected phishing before realizing that the message was genuine, a situation that illustrates the difficulty of communicating about a data leak when the attackers are using exactly the same channels as the legitimate platform.
Data already exploited for targeted phishing
The value of booking data to attackers does not lie in names or email addresses taken in isolation; this information is often found in countless previous leaks. What makes this compromise particularly exploitable is the combination of an identity with a precise travel context: a name associated with a specific hotel, dates of stay, a reservation number. A fraudulent message that incorporates all these elements is considerably more convincing than a generic phishing message, because it reproduces exactly what a customer expects to receive from the platform or accommodation.
The most likely exploitation scenarios follow a pattern already documented in the field of travel bookings: false requests for credit card verification prior to arrival, messages imitating the accommodation to demand additional payment, or notifications of technical problems requiring urgent confirmation of bank data. These messages arrive by email, SMS or WhatsApp, and are based on information that only the platform and the accommodation are supposed to know, giving them an appearance of legitimacy that is difficult to question. What’s more, travel booking data is particularly sensitive because of its temporal dimension. As departure approaches, the fear of seeing a booking cancelled or a stay compromised pushes travellers to react in a hurry rather than checking the legitimacy of the message received. Scammers know this bias and exploit it methodically: phishing attempts are concentrated in the days leading up to a trip, at the precise moment when vigilance gives way to haste. These data find an outlet in exploitation infrastructures that existed long before the April 2026 incident.
A documented pattern of reservation operations
In November 2025, Sekoia documented in detail the “I Paid Twice” campaign, illustrating the level of maturity reached by these operations. The scheme is based on a two-stage attack: first, operators compromise the accounts of partner accommodations, via phishing emails imitating the platform and exploiting the ClickFix technique to deliver the PureRAT infostealer, then they use these compromised accounts to access bookings and send, from the official interface, fraudulent requests for payment. Travelers thus receive a second invoice for a booking already paid for, via a message that passes through legitimate channels and contains all the exact information about their stay.
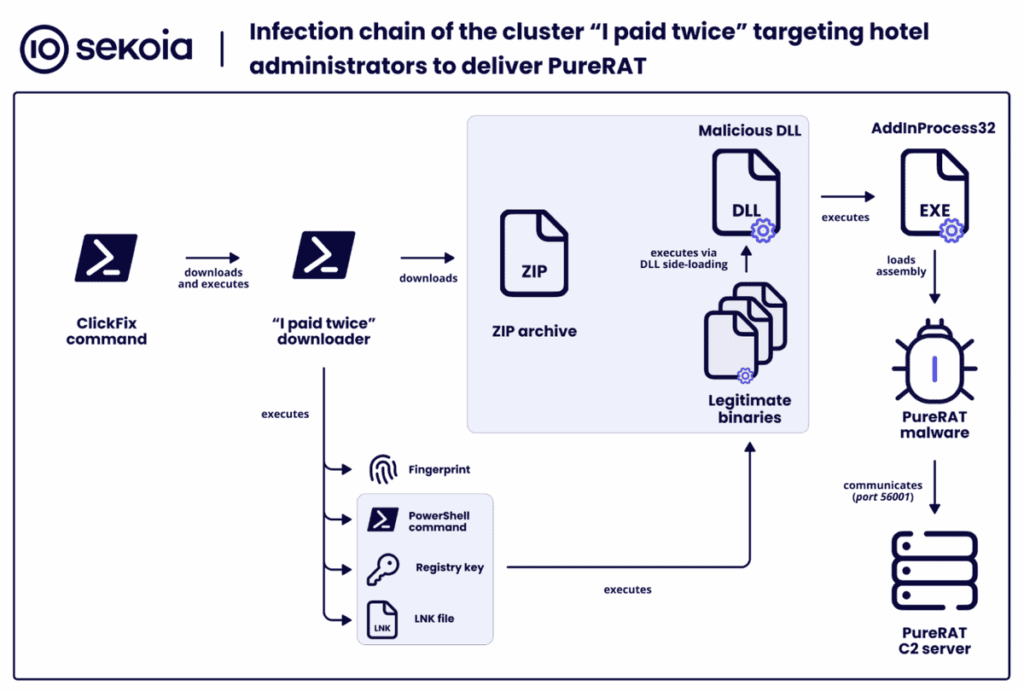
Microsoft Threat Intelligence reported back in March 2025 on a similar campaign targeting hotel staff with emails impersonating Booking, designed to deliver infostealers via ClickFix. The objective was identical: to retrieve access credentials to the partner portal in order to reach downstream customer data.
While these campaigns have no established technical link with the April 2026 intrusion, they do show that the infrastructure for exploiting reservation data is operational, and that the data resulting from this new compromise has an immediate outlet.
Booking.com has reiterated in its notifications that it never requests bank details by email, telephone, WhatsApp or SMS, and that it never requires a bank transfer other than the payment terms set out in the booking confirmation. This reminder is necessary, but it comes after the data has already been exploited. However, the phishing documented on Reddit precedes this notification, meaning that data was being exploited before customers were alerted.
A long-targeted booking ecosystem
The online booking ecosystem has been the subject of repeated attacks for several years, following a pattern that systematically targets the hotel link to reach travelers.
In 2018, crooks used phone phishing techniques to steal the login credentials of hotel employees in the United Arab Emirates, gaining access to the booking data of over 4,000 customers. Booking.com reported the leak to the Dutch regulator 22 days late, resulting in a fine of 475,000 euros.
In late 2023, Secureworks and Sophos researchers documented a campaign using the Vidar infostealer to steal credentials from hotel administration portals. Once in possession of these credentials, attackers would send fraudulent payment requests directly to customers via the platform’s internal messaging system, messages that appeared in the official interface and appeared perfectly legitimate.
From 2025 onwards, campaigns became more industrialized, with the adoption of techniques such as ClickFix and the use of specialized infostealers, as detailed above. The frequency of documented campaigns (March 2025 by Microsoft, November 2025 by Sekoia, January 2026 by Cybernews) indicates sustained and growing activity.
The pattern is consistent: the attacker compromises a partner hosting’s account, accesses customer data via the platform, then targets travelers with messages containing their real booking information. This two-stage attack model – compromising the partner, then exploiting customer data – makes every accommodation listed on the platform a potential vector for social engineering.
The trajectory from 2018 to 2026 shows a clear progression. Artisanal telephone phishing targeting a few hotels in the Emirates has given way to campaigns equipped by infostealers, ClickFix kits sold on criminal forums and automated double-billing infrastructures. In a context where AI-assisted social engineering continues to grow in sophistication, the very architecture of intermediary reservation platforms, where each registered accommodation constitutes an entry point to the set of reservations it manages, makes them structurally exposed targets.
What to do if you are a Booking.com customer
Booking has indicated that its customer support services are available 24 hours a day in several languages. Beyond this assistance, the basic measures apply: changing passwords, activating two-factor authentication, and changing logins on any service where the same password is reused. These concrete actions reduce exposure to scam attempts that exploit compromised data.
Anyone with a current or future reservation should be extra vigilant. If in doubt about a message received concerning a stay, contact the accommodation directly by telephone, using the number listed on the establishment’s official website, not the one contained in the suspect message. Never give out your ID, passport number or bank details in response to an unsolicited request, even if it seems to come from the accommodation.
Finally, it’s important to remain vigilant over the coming weeks. Targeted phishing attempts are more likely to occur closer to the holiday dates, when the traveler’s perceived urgency is greatest. Keeping an eye on bank statements over the coming weeks remains a justified measure of caution: the booking platform claims that financial data has not been affected, but until the exact attack vector has been communicated, the true extent of the compromise cannot be assessed.
Booking platforms, structural targets of social engineering
The intrusion confirmed by Booking.com adds to a track record that shows that intermediary booking platforms concentrate a quantity and precision of personal data that make them prime targets for social engineering. It’s not the name or email address that interests attackers, it’s the combination of this information with a verifiable travel context that makes phishing operational.
By failing to communicate the number of people affected, the attack vector or the chronology of the incident, the company leaves its customers unable to assess their own level of exposure. This lack of information also affects partner hosts: a Reddit user who received the notification as a partner suggests that the compromise was not limited to the client side of the platform. If partner accounts have been used as entry points or have been exposed, hosting providers need to know this in order to secure their own access and protect the travelers’ data they manage.
Source:
- BleepingComputer: New Booking .com data breach forces reservation PIN resets
- CybersecurityNews: Booking .com Confirms Data Breach
- TechCrunch: Booking .com confirms hackers accessed customers’ data
- The Guardian: Booking .com warns customers of hack that exposed their data
- Sekoia: Phishing Campaigns “I Paid Twice” Targeting Booking.com Hotels and Customers
- Microsoft: Phishing campaign impersonates Booking.com, delivers a suite of credential-stealing malware
- Sophos: Vidar Infostealer Steals Booking.com Credentials in Fraud Scam
