On April 6, 2026, Microsoft Threat Intelligence published a consolidated analysis of the operations of Storm-1175, a China-based cybercriminal actor it has been tracking since at least July 2024. Already associated with the deployments of Black Basta and Akira via a VMware ESXi flaw, Storm-1175 is now focusing its operations on the Medusa ransomware, which it deploys with formidable efficiency. Able to go from initial access to complete network encryption in less than 24 hours, this group targets Internet-exposed systems in the healthcare, education and finance sectors, mainly in Australia, the UK and the USA. Its main weapon: the ultra-rapid exploitation of recently disclosed vulnerabilities, sometimes even before the patch has been released.
Storm-1175 is just one cog in a larger ecosystem. Medusa functions as a RaaS platform shared between Chinese, Russian and North Korean affiliates. This geopolitical diversity makes attribution complex and dismantling operations particularly difficult. To understand Storm-1175 is to grasp how the RaaS model enables an isolated actor to inflict disproportionate damage by relying on a shared infrastructure.
Table des matières
ToggleMedusa, a RaaS platform that crosses borders
Identified for the first time in June 2021, and really coming into its own from 2023 onwards, Medusa illustrates the maturity of the RaaS model: a single technical platform, operators with radically different profiles.
Affiliates with multiple allegiances
Check Point Research points to Russian operators, based on the fact that the malware never targets organizations in Russia or Moscow’s allied countries, and that it actively circulates on Russian-speaking forums on the dark web. In February 2026, Broadcom (via its Symantec and Carbon Black teams) identified theuse of Medusa by the North Korean group Lazarus in attacks targeting US healthcare infrastructures and non-profit organizations. Storm-1175, identified by Microsoft as based in China and financially motivated, completes a picture of affiliates with diverse interests and sponsors. This scattering of Russian, North Korean and Chinese affiliates illustrates the maturity of the RaaS model: the platform survives and prospers independently of its operators, as is the case for other brands of the same type, from RansomHub to DragonForce.
The extent of the damage documented by the FBI
In March 2025, the FBI, CISA and MS-ISAC issued a joint advisory warning that Medusa had already affected over 300 critical infrastructure organizations in the USA, in the healthcare, education, legal, insurance, technology and manufacturing sectors. The Medusa leak site has since claimed more than 500 victims since the operation was launched in early 2023. The FBI has also documented a case that could amount to a form of triple extortion: after paying a ransom, a victim was allegedly recontacted by another Medusa actor claiming that the first negotiator had embezzled the funds, and demanding payment of half the amount already paid to provide the “real” decryptor. Authorities are cautiously characterizing this incident as a potential triple extortion scheme, a practice that goes beyond the double extortion mechanisms usually employed by the group.
From hospitals paralyzed to counties cut off from the network
The consequences of Medusa’s operations can be measured directly in disrupted human lives. At the end of February 2026, the University of Mississippi Medical Center (UMMC), Mississippi’s largest hospital and the state’s only Level I trauma center, was paralyzed for nine days. Clinics were closed, scheduled surgeries cancelled, and nursing staff forced to revert to pen and paper to manage pediatric and trauma emergencies. The ransom demanded was $800,000, with the threat of publication of the stolen data. The hospital suffered a 20% drop in revenue over the month.
A few days after UMMC, Passaic County in New Jersey lost access to all its computer systems and phone lines in a separate attack using the same ransomware. Medusa had also in the past targeted leading companies, including Toyota Financial Services for an $8 million ransom. The group has not disappeared, and is still active on all fronts: healthcare, communities and the private sector.
Correction window shrinks until it disappears
Storm-1175’s tactical signature relies on the exploitation of N-day vulnerabilities (recently disclosed vulnerabilities for which a patch exists but has not yet been widely deployed). Since 2023, Microsoft has observed the exploitation of more than 16 vulnerabilities in 10 different software products: Microsoft Exchange, PaperCut, Ivanti Connect Secure, ConnectWise ScreenConnect, JetBrains TeamCity, SimpleHelp, CrushFTP, GoAnywhere MFT, SmarterMail and BeyondTrust. All are enterprise software products exposed on the Internet, often deployed en masse, and whose patch window can extend over weeks.
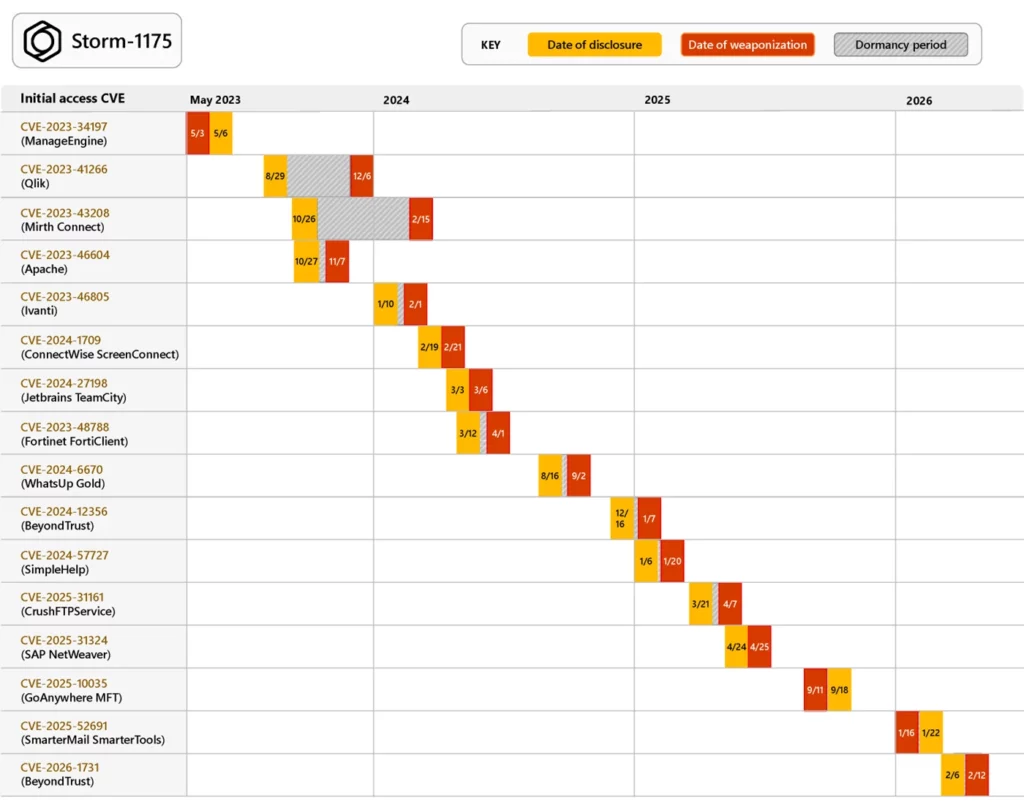
The time between disclosure and exploitation can sometimes be counted in hours. In the case of the SAP NetWeaver flaw (CVE-2025-31324), Storm-1175 began exploiting it the day after it was publicly disclosed, on April 25, 2025.
From N-days to zero-days: expanding the arsenal
Microsoft has documented the use of at least three zero-day vulnerabilities by Storm-1175. One of the most recent, CVE-2026-23760, affects the SmarterMail mail server and was exploited a week before its public disclosure. CVE-2025-10035, a critical flaw in GoAnywhere MFT, followed the same pattern: exploitation a week before the patch was released.
This zero-day capability marks a significant evolution. Microsoft notes that Storm-1175 “demonstrates advanced development capability or new access to resources such as exploit brokers”. However, Microsoft qualifies its own finding: GoAnywhere MFT had already been targeted by other ransomware groups (notably Cl0p in 2023), and the SmarterMail flaw showed similarities to a previously disclosed vulnerability, which may have facilitated the development of the exploit.
Storm-1175 is also capable of chaining several exploits together. On on-premises Microsoft Exchange servers, the group combined CVE-2022-41080 (initial access via Outlook Web Access) and CVE-2022-41082 (remote code execution), a technique publicly documented under the name OWASSRF. Its attack surface is not limited to Windows: Microsoft has identified exploits of Oracle WebLogic instances under Linux in late 2024.
An attack chain calibrated for speed
Once the initial access has been obtained by exploiting a vulnerability, Storm-1175 deposits a web shell or remote access payload, then accelerates towards the final objective. In the fastest cases, the ransomware is deployed in less than a day. The majority of attacks take place over five to six days.
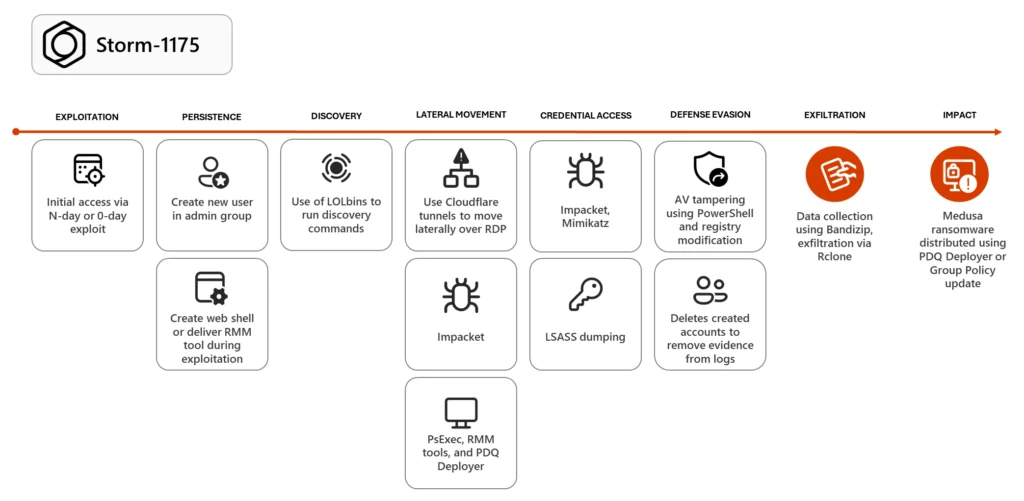
Persistence and lateral movement through abuse of legitimate tools
The first post-compromise action is to create a new user account added to the local administrator group. From this position, Storm-1175 conducts its reconnaissance and lateral movements by relying heavily on tools that IT teams use on a daily basis.
Native Windows binaries (LOLBins, for Living Off the Land Binaries) are the first lever: PowerShell for command execution, PsExec for remote deployment. The group also uses Cloudflare tunnels, renamed to mimic legitimate system binaries such as conhost.exe, to pivot via RDP (Remote Desktop Protocol). If RDP is not enabled in the target environment, Storm-1175 directly modifies the Windows firewall policy to enable it.
The arsenal also includes a range of RMM (Remote Monitoring and Management) tools diverted from their legitimate use: Atera, Level RMM, N-able, DWAgent, MeshAgent, ConnectWise ScreenConnect, AnyDesk and SimpleHelp. These tools offer unobtrusive persistence, an alternative command and control channel, and the ability to deploy additional payloads without triggering conventional alerts.
PDQ Deployer, a software deployment tool for system administrators, plays a central role in Storm-1175 operations. It enables the silent installation of applications across the entire IT estate, including the final deployment of the ransomware itself via a script named RunFileCopy.cmd.
Credential theft and escalation to the domain controller
Storm-1175 exploits Impacket, a collection of open source Python classes, for the lateral movement and dumping of credentials (identifiers stored in memory) via LSASS (Local Security Authority Subsystem Service, the Windows process that manages authentication). The Mimikatz tool completes this arsenal of documented intrusions in 2025. The group also uses living-off-the-land techniques: modifying the UseLogonCredential registry key to reactivate the WDigest cache, or using Task Manager to dumper LSASS credentials.
Once sufficient privileges have been obtained, Storm-1175 pivots to a domain controller to access the NTDS.dit file (the Active Directory database containing accounts and passwords for the entire domain) and the SAM hive. Microsoft has also observed the use of a dedicated script to extract passwords stored in Veeam Backup, an attack vector reminiscent of the Veeam vulnerabilities exploited by other ransomware groups.
Neutralizing defenses and deploying Medusa
Before launching the encryption, Storm-1175 modifies Microsoft Defender Antivirus registry settings and uses encrypted PowerShell commands to add the C:\\ drive to the antivirus exclusion list, preventing any detection of the payloads. Data exfiltration takes place via Bandizip (archiving) and Rclone (synchronization to a cloud controlled by the attacker), enabling continuous, automated transfer throughout the attack.
The Medusa ransomware is then deployed network-wide via PDQ Deployer or, in some cases, via a Group Policy Update (GPO) exploiting the privileges obtained on the domain controller.
How to protect yourself against ransomware that strikes in 24 hours
Storm-1175 illustrates an operational reality: the window between the disclosure of a vulnerability and its exploitation can be reduced to a single day. For organizations whose assets are exposed on the Internet, there are five concrete steps to take.
1. Map the external attack surface
An External Attack Surface Management (EASM) tool can be used to identify exposed assets affected by a vulnerability before it becomes public knowledge. This is the first line of defence against an actor who targets only assets exposed on the Internet.
2. Enable tamper protection and DisableLocalAdminMerge
Tamper protection prevents the antivirus from being deactivated by an attacker with elevated privileges. The DisableLocalAdminMerge parameter prevents the creation of antivirus exclusions via GPO. Combined, these two parameters directly neutralize the antivirus exclusion technique observed in Storm-1175.
3. Deploy Credential Guard
Credential Guard, enabled by default on Windows 11 and available on earlier versions of Windows, isolates credentials stored in the LSASS process in a virtualized environment inaccessible to conventional dumping tools. This feature must be activated before joining the domain. It protects LSASS credentials, the primary target of Storm-1175’s Impacket and Mimikatz arsenal.
4. Monitor unapproved RMM installations
Any installation of an unauthorized RMM tool (Atera, AnyDesk, SimpleHelp, etc.) should trigger an immediate alert and password reset of the accounts used for the installation. Storm-1175 uses up to eight different RMM tools; any unauthorized installation is an intrusion signal.
5. Apply Microsoft Defender ASR rules
Microsoft Defender’s Attack Surface Reduction (ASR) rules specifically block credential theft from LSASS, process creation via PsExec and WMI, and web shell creation on servers. These three vectors are documented by Microsoft in Storm-1175 operations.
Zero-day warfare, the new RaaS terrain
Storm-1175 embodies a fundamental trend in the ransomware ecosystem: the zero-days race is no longer reserved for state actors. A financially motivated RaaS affiliate can now access vulnerabilities before they are fixed, whether through exploit brokers or in-house research capabilities. In July 2024, Microsoft had already linked Storm-1175, alongside three other cybercriminal groups, to attacks exploiting Akira and Black Basta via an authentication bypass flaw in VMware ESXi, illustrating the versatility of this player within the RaaS ecosystem.
As long as systems remain exposed on the Internet without up-to-date patches, players like Storm-1175 will continue to find entry points. Storm-1175’s ability to exploit zero-days, combined with the resilience of a RaaS platform that has been active for five years and is shared by numerous affiliates around the world, sketches a threat model that is likely to continue to strengthen.
Sources
- Microsoft Threat Intelligence: Storm-1175 focuses gaze on vulnerable web-facing assets in high-tempo Medusa ransomware operations
- BleepingComputer: Microsoft links Medusa ransomware affiliate to zero-day attacks
- LeMagIT: Storm-1175: a vulnerability exploitation specialist at Medusa’s service
- CISA / FBI / MS-ISAC: #StopRansomware: Medusa Ransomware
- Check Point Research: Medusa Ransomware Group: A Rising Threat in 2025
- Symantec : North Korean Lazarus Group Now Working With Medusa Ransomware
- The Record: Medusa ransomware gang claims attacks on prominent Mississippi hospital, New Jersey county
