Four years after its launch, LeakBase no longer responds. In place of the forum, an FBI seizure banner. Behind this familiar image lies an operation of uncommon scope: fourteen countries mobilized, a hundred or so simultaneous actions on several continents, and above all the complete capture of a database that exposes tens of thousands of members who thought they were anonymous to legal proceedings. What Operation Leak illustrates above all is not just the collapse of a platform, but the effectiveness of a well-honed international cooperation, mobilizing fourteen countries around a common target.
Table des matières
ToggleLeakBase, a market for stolen data accessible to all
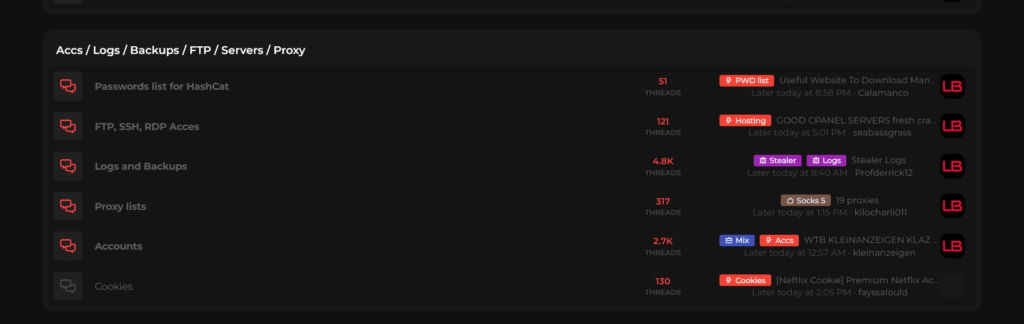
Since 2021, LeakBase had established itself as one of the key points of passage for the trade in compromised data in the English-speaking world. The platform continuously archived databases resulting from compromises, stealer logs (files generated by malware infostealers, which automatically extract logins, passwords, session cookies and form data from infected machines), and more generally any data useful for downstream attacks: credential stuffing, bank fraud, identity theft.
What set LeakBase apart from many similar platforms was its ease of access. The forum operated on the open web, bypassing Tor, operated in English, and offered free registration. This combination enabled it to reach a much wider spectrum of profiles than forums confined to the dark web, including players with no particular technical skills. Threat intelligence firm Flare described it as “one of the most sophisticated forums on the dark web, both in terms of the volume of sensitive data available and the maturity of its approach to discovery and commerce”. A somewhat paradoxical formulation for a platform accessible via a simple browser, but one that testifies to the level of structuring achieved by LeakBase. The forum combined a marketplace and discussion areas.
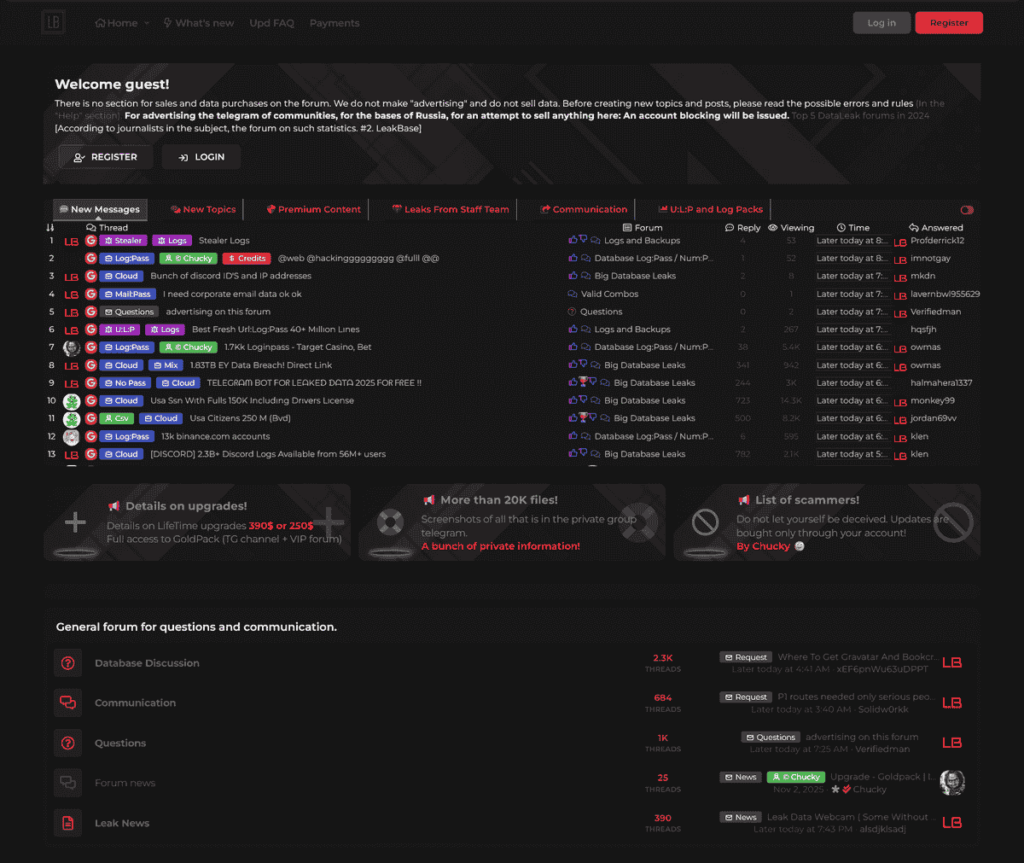
At the end of December 2025, the forum had over 142,000 registered members, around 32,000 posts and more than 215,000 private messages exchanged. The hosted databases contained hundreds of millions of login/password pairs from large-scale compromises targeting companies and individuals, particularly in the USA.
How the LeakBase forum worked
LeakBase didn’t emerge from nowhere. Its rapid growth owes much to the successive closures of its predecessors: the seizure of RaidForums in 2022, then the dismantling of BreachForums in 2023, each time unleashing a community of several hundred thousand users in search of a new platform. LeakBase inherited it, with the networks, data and reputation that went with it. This fits a well-documented cycle: every time a major platform is dismantled, another one takes over to absorb its community.
The forum had been launched with the support of cybercriminal group ARES, and had refined its model over time. Registration was free, but premium access was available for a one-off subscription fee of a few hundred dollars. A system of credits and reputation structured exchanges between members: each contribution of data or transactions strengthened the status of its author within the community, thus maintaining a sustained level of activity. The platform also incorporated an escrow payment mechanism to secure transactions.
The offer covered credit card numbers and routing data, reusable identifiers for mass attacks, personal and corporate information, as well as areas dedicated to programming, hacking, social engineering, cryptography and opsec guides. A significant proportion of the available databases had been obtained by SQL injection against unpatched web applications.
A notable rule reported by several sources: the forum forbade users to publish data relating to Russia, a recurring restriction on this type of platform that tends to suggest a settlement or tolerance in this geographical area. Security researchers suspect that LeakBase’s administrators are of Russian origin; despite the forum’s dismantling, they are probably still at large.
A threat the FBI has prioritized for several years
It wasn’t the sheer size of the forum alone that led to it becoming a priority target for the Salt Lake City FBI office. Brett Leatherman told The Record that LeakBase had become “a place where users were increasingly sharing information to access U.S. networks, potentially critical infrastructure”. It was this dimension – the forum as a vehicle for initial access to sensitive systems – that kept LeakBase at the top of the FBI’s priority list for several years before the operation came to an end.
Leatherman also clarified the profile of the victims as investigators are beginning to piece it together: “These are victims of opportunity. In many cases, the hackers were able to break in and gain access to authentic credentials, which could concern small and medium-sized businesses or large corporations. We’ll be learning a lot more very soon.”
The two-phase operation
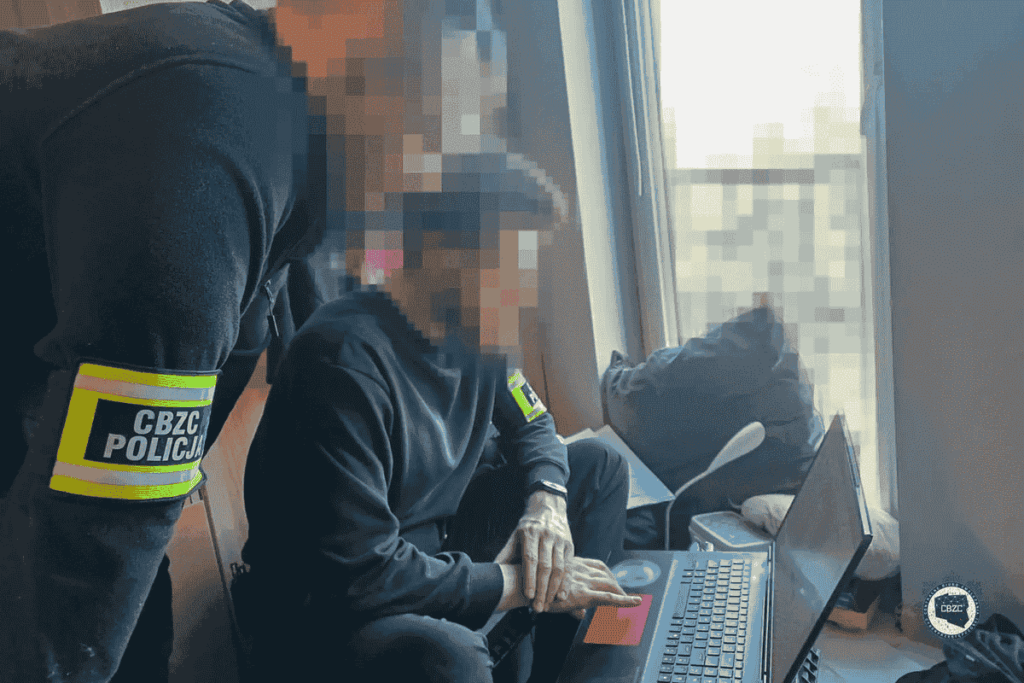
Operation Leak unfolded according to a two-phase timetable, on March 3 and 4, 2026, at the end of an investigation conducted over several years.
On March 3, the authorities carried out around 100 coordinated actions in numerous countries, targeting 37 of the platform’s most active members. The results include 13 arrests, 32 searches, interviews with 33 suspects, as well as so-called “knock-and-talk” interventions, home visits without arrest warrants, whose aim is as much to identify individuals as to alert them to the fact that they are known to the authorities. None of the arrests took place on American soil, said Brett Leatherman.
On March 4, the technical phase was launched: the forum’s two domains(leakbase[.]la and leakbase[.]ws) were seized and redirected to FBI servers(ns1.fbi.seized.gov / ns2.fbi.seized.gov). The seizure was based on two separate court orders, one issued by the US District Court for the District of Utah, the other by a German court, reflecting the multinational legal architecture required for an operation of this nature. The .ws domain had been registered on February 7, 2026, less than a month before the seizure, a sign that the forum was still in full operational expansion when the investigators struck.
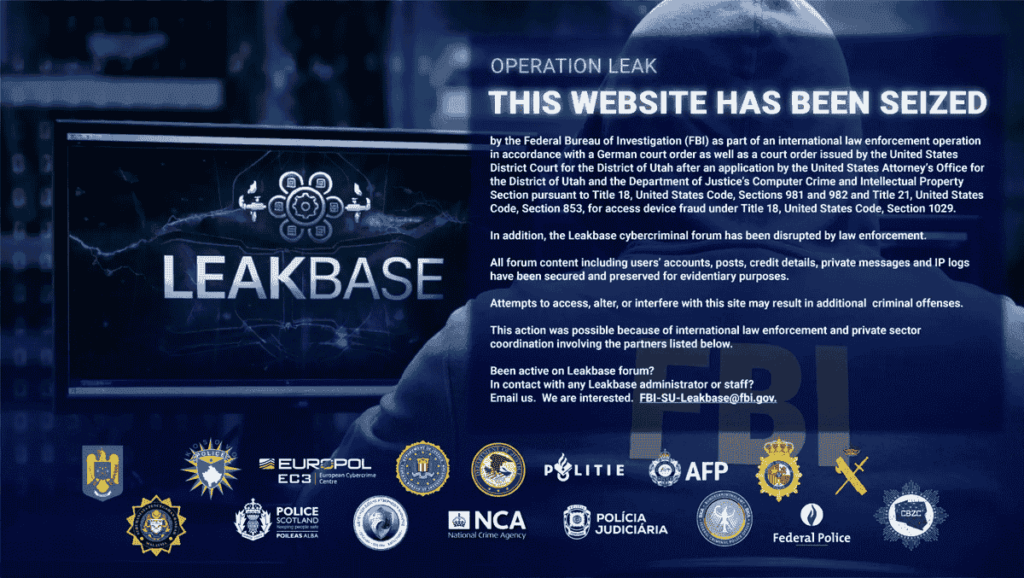
The banner displayed on the site addresses an explicit warning to former members: “All forum content, including user accounts, posts, banking information, private messages and IP address logs, has been secured and retained for evidentiary purposes.”
The countries involved in the operation are: Australia, Belgium, Canada, Germany, Greece, Kosovo, Malaysia, the Netherlands, Poland, Portugal, Romania, Spain, the United Kingdom and the United States.
Europol at the heart of the coordination system
Central coordination was provided by Europol from The Hague, as part of the Joint Cybercrime Action Taskforce (J-CAT). In addition to logistical coordination, the European Cybercrime Center (EC3) carried out in-depth analytical work, mapping the forum’s infrastructure, cross-referencing data with ongoing investigations across Europe and beyond, and identifying suspects and victims on the basis of available digital evidence. A data scientist dedicated to the operation took charge of extracting and structuring millions of data points to produce leads directly exploitable by the investigation teams.
On the day of action, a joint command post enabled the fourteen participating countries to share updates and intelligence in real time, as enforcement measures were deployed.
Edvardas Šileris, Director of Europol’s European Cybercrime Centre (EC3), summed up the significance of the message sent to cybercriminals: “This operation shows that no corner of the Internet escapes the attention of international law enforcement authorities. What began as an obscure forum dedicated to stolen data has now been dismantled, and those who thought they could hide behind anonymity are being identified and held accountable.”
Seizing the database as a means of identification
The seizure of the forum’s entire internal database is probably the most far-reaching aspect for members of the platform. Accounts, posts, private messages, IP logs and payment details: this data enables investigators to lift the supposed anonymity of users who have not yet been identified, long after the forum has been closed down.
The authorities have also chosen to contact certain suspects directly via the digital channels they used for their forum activities. The signal sent was deliberate: the investigators knew who they were and how to reach them. Brett Leatherman was explicit about what happened next: “If these players migrate to another platform believing in their anonymity, they should know that we’ll be following them.” The investigation is still ongoing.
A day of coordinated strikes
On the same day as Operation Leak, Europol and Microsoft jointly announced the dismantling of Tycoon 2FA, a PhaaS (Phishing-as-a-Service) sold for $350 a month on Telegram and Signal, used by thousands of cybercriminals to bypass multi-factor authentication via Adversary-in-the-Middle attacks. Microsoft, which led the operation alongside Europol, authorities in six countries and eleven cybersecurity companies, seized 330 domains making up the heart of the infrastructure. The scale of the service is striking: in mid-2025, Tycoon 2FA accounted for around 62% of all phishing attempts blocked by Microsoft, with over 30 million e-mails intercepted in a single month. Tycoon 2FA’s downfall is a reminder that Adversary-in-the-Middle (AiTM) attacks are set to gain further momentum with the integration of AI, as evidenced by cybersecurity experts’ predictions for 2026.
The actions against LeakBase and Tycoon 2FA are part of a sequence of operations that demonstrate a shift in law enforcement posture: the aim is no longer just to arrest individuals, but to target the service infrastructures that enable the cybercriminal ecosystem to function, from forums to phishing kits to malware marketplaces.
What this dismantling reveals about the state of the threat
The history of cybercriminal forums is, however, a sobering one: RaidForums has been replaced by BreachForums, BreachForums by LeakBase. Precedents therefore suggest that a new platform is likely to emerge, the question being how quickly. The challenge now lies in investigators’ ability to exploit the database seized to trace back the channels before new platforms emerge.
Even before the official announcement, there were signs of this recomposition: hours before the DOJ release, discussions were circulating on several Telegram channels, with members warning their contacts to assume that their data had been collected and to act accordingly.
For the organizations, this takedown is a reminder of a structural reality: data extracted during a compromise does not disappear. It circulates, is resold, fragmented, recombined, and can resurface months or years later to fuel phishing campaigns, identity fraud or mass attacks. Leaked companies can see their data reused long after the initial incident, often without their knowledge. Implementing unique passwords per service and multi-factor authentication remains the most direct response to this resale cycle.
Sources :
- Europol: Major data leak forum dismantled in global action against cybercrime forum
- U.S. Department of Justice: United States Leads Dismantlement of One of the World’s Largest Hacker Forums
- Security Affairs: FBI and Europol dismantle LeakBase cybercrime forum
- Hackread: LeakBase Cybercrime Hacker Forum Seized
- The Record: Sprawling FBI, European operation takes down Leakbase cybercrime forum
- Flare: FBI Seizes Leakbase
