On March 24, 2026, the European Commission detected an intrusion into the AWS cloud infrastructure hosting its Europa(.)eu sites. Three days later, the ShinyHunters group claimed responsibility for the attack and published a first archive of 90 GB, claiming to have exfiltrated over 350 GB in total, including email backups, databases and contractual documents. The institution responsible for the Union’s cyber regulatory arsenal (NIS2, Cyber Solidarity Act, January 2026 cybersecurity package) finds itself in the position of victim, for the second time in eight weeks.
The Commission confirms the incident on March 27, just after BleepingComputer was the first to reveal the affair. But the E.C. remains evasive on the exact nature of the data exposed. Among the most worrying elements put forward by security researchers: DKIM signature keys which, if compromised, would make it possible to forge authenticated emails from the institution’s official domains. The investigation is ongoing, and the scope of the leak has yet to be determined.
Table des matières
ToggleThe Commission confirms the attack, but is stingy with details
In its press release of March 27, the Commission states that it took immediate action as soon as the incident was detected, ensuring the continuity of its sites without interruption of service. The official message is measured: “The initial findings of our ongoing investigation suggest that data has been extracted from these websites. The Commission is duly notifying EU entities that may have been affected.”
The institution’s internal systems have not been compromised: the affected perimeter is limited to the cloud infrastructure hosting the Europa(.)eu public sites. This point is emphatically repeated in the press release, which provides little information on the nature of the data actually exposed, nor on the attack vector used. The targeted infrastructure was based on AWS (Amazon Web Services) accounts. AWS was careful to deny any failure of its platform: “AWS did not suffer any security incident, and our services functioned as expected”, a spokesperson told BleepingComputer. This response is in line with the cloud’s shared responsibility model: AWS secures its infrastructure, but account and configuration management remains the customer’s responsibility.
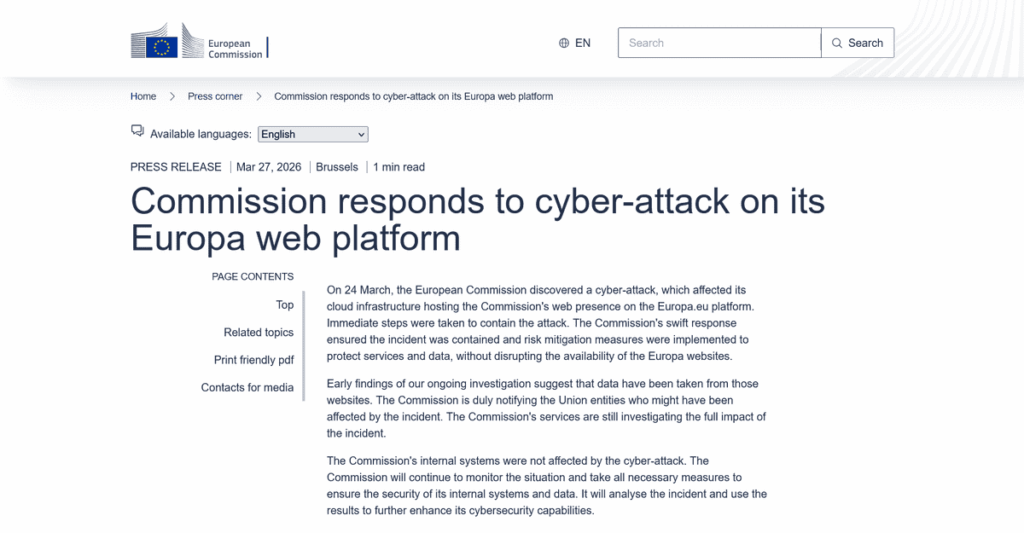
Interviewed by the press on March 28, spokesman Thomas Regnier confirmed that parts of the Europa platform were hosted on cloud infrastructure provided by Amazon, while seeking to minimize the scope of the incident. He insisted that the domains affected were limited to the public Europa(.)eu sites and that “the internal infrastructure was absolutely unaffected”. As for the data potentially exposed, Regnier asserted, “We’re talking about data that is potentially already in the public domain.” The Commission did not specify what data may have been accessed, how many users may have been affected, and declined to comment on whether personal data was involved, citing the ongoing investigation.
Mail, databases, contractual documents: the loot claimed by ShinyHunters
On their dark web site, the attackers describe their booty in these terms:
“European Commission (
*.europa.eu)– Over 350 GB of data has been compromised, including mail server backups, databases, confidential documents, contracts and much other sensitive information.”ShinyHunters, on their leak site
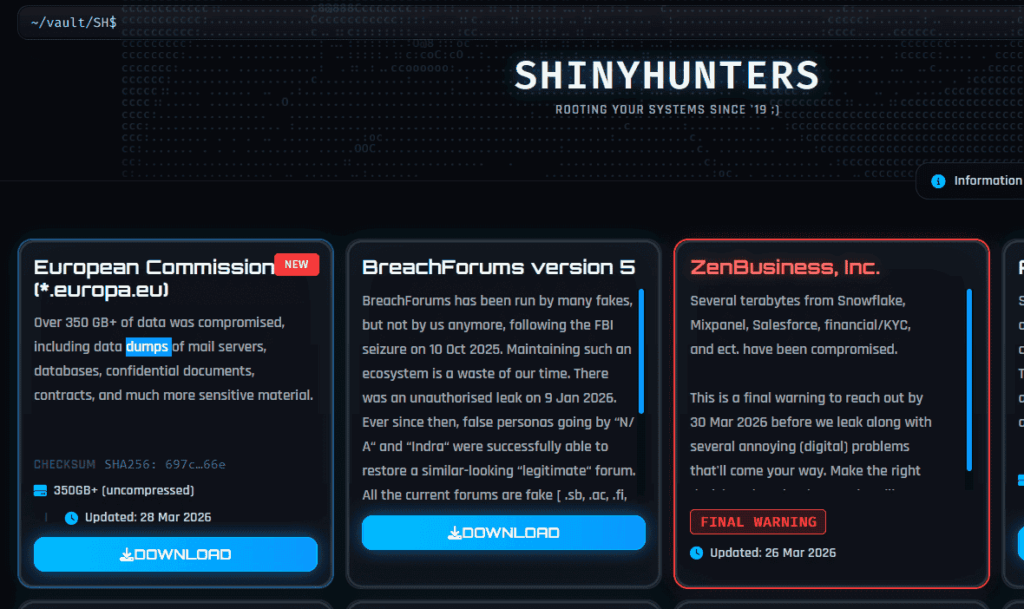
According to external security researchers, the exfiltrated data also included DKIM signature keys, internal administration URLs, data from the NextCloud collaboration platform and the Athena military funding mechanism, as well as potentially the entire SSO directory. These elements have not been independently confirmed at this stage.
ShinyHunters has told BleepingComputer that it has no intention of extorting the Commission, but plans to publish the full data at a later date. A stance that in no way diminishes the seriousness of the situation. Nick Tausek, security automation architect at Swimlane, puts it plainly: “The fact that the attacker says he has no intention of extorting doesn’t make the incident any less serious, it simply changes the modus operandi. A silent leak can be just as damaging to trust, diplomacy and ongoing investigations.”
The DKIM risk: when a data leak becomes a phishing vector
Among the elements claimed, the potential exposure of DKIM (DomainKeys Identified Mail) signature keys is the one that has most caught the attention of security researchers. These cryptographic keys are used to authenticate emails sent from a domain: they enable the recipient server to verify that a message originating from, say, an @ec.europa.eu domain has not been forged.If these keys have indeed been exfiltrated, anyone in possession of them can forge emails that pass standard authentication checks (SPF, DKIM, DMARC) from official Commission domains, a capability directly exploitable for spear-phishing campaigns targeting member states, partner governments or companies contracted by Brussels.
Reacting to a thread published on March 29 on X by International Cyber Digest, which has since been widely reposted, announcing the cyberattack, cybersecurity commentator z3n sums up the diagnosis: “The fact that DKIM signature keys and AWS configuration snapshots were compromised in the same breach is catastrophic. Using DKIM keys, cybercriminals can forge emails that pass the authentication of European Commission domains, which is ideal for carrying out spear-phishing attacks against EU member states.”
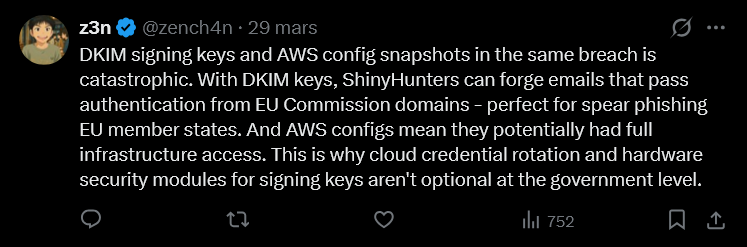
This is precisely why the rotation of cloud credentials and the use of hardware security modules (HSMs) for signing keys are not optional on the scale of a government institution. However, this scenario is subject to confirmation that these elements are indeed among the exfiltrated data.
The risk is not limited to ShinyHunters: the first 90 GB archive is accessible on the group’s leak site, and any organization that has downloaded it can potentially take advantage of it. Until the Commission has confirmed the extent of the attack, or rotated all the affected keys if necessary, organizations that regularly exchange messages with European institutions would do well to step up their vigilance on incoming messages from these domains, and ensure that their filtering rules don’t silently let DKIM validation failures through.
Ivanti vulnerability in January, AWS accounts in March: two attack surfaces in eight weeks
This isn’t the first time in 2026 that the Commission has found itself in a tricky position. On January 30, its central mobile device management (MDM) infrastructure was the target of a cyber attack. The incident was contained within nine hours, and no mobile devices were compromised. However, staff data – names and telephone numbers – may have been exposed, according to the official statement issued at the time, which was made public in February.
The January incident was part of a series of attacks that also affected the Dutch Data Protection Authority and Valtori, a Finnish government agency attached to the Ministry of Finance – all exploiting code injection vulnerabilities in Ivanti Endpoint Manager Mobile (EPMM).
Two separate incidents, two different attack surfaces, in the space of eight weeks. The first exploited a known software vulnerability (code injection in Ivanti EPMM); the second pointed to an account or configuration compromise in an AWS cloud environment, a vector of an entirely different nature. The first was contained within nine hours. The second, by the scale of the data potentially exfiltrated and the nature of the elements evoked (messaging, contractual data, possible exposure of cryptographic keys), places the Commission in a much more uncomfortable position, all the more so as the investigation has not yet established the exact scope of the leak. Two such close compromises could also signal to opportunistic actors that an institution is momentarily exposed or mobilized for crisis management, inviting further attempts in the wake.
ShinyHunters: from database theft to mass exfiltration
ShinyHunters first appeared around 2020, and quickly earned a reputation for high-profile operations targeting major corporations, including Ticketmaster, Santander and AT&T. The group is primarily motivated by greed, and operates on a double extortion model: stealing data, demanding ransom to prevent disclosure, then publishing on dark web forums if the target refuses to pay.
Its preferred method is vishing, combined with real-time phishing kits capable of bypassing multi-factor authentication. The attackers pose as IT support, directing the victim to a fake login page synchronized with the real authentication flow, and intercepting MFA credentials and tokens in the process. It is through this technique that the group has compromised SSO accounts at over a hundred organizations in recent months, a massive campaign we detailed in a dedicated analysis. Recent victims who have publicly confirmed intrusions include Infinite Campus, CarGurus, Canada Goose, Panera Bread, Betterment, SoundCloud and the Match Group.
ShinyHunters operates within Scattered LAPSUS$ Hunters, a cybercriminal alliance that federates Scattered Spider, LAPSUS$ and ShinyHunters, and in which the latter occupies the role of data exfiltrator and monetizer. A wave of arrests linked to Scattered Spider in the summer of 2025 partially slowed down the group, without putting an end to its operations.
In the case of the European Commission, the initial attack vector remains unknown to this day. The Commission has not formally attributed the attack: the link to ShinyHunters is based on the group’s own claims and on analyses by independent researchers. Nor has the group communicated how it gained access to the AWS accounts, making it difficult to assess the residual risk to other EU institutions.
European cybersecurity put to the test
On January 20, 2026, ten days before the first incident, the Commission presented a new cybersecurity legislative package designed to strengthen the Union’s collective defenses. It also draws on a dense regulatory arsenal: the NIS2 Directive, the Cyber Solidarity Act and the Cybersecurity Regulation, which sets out a protection framework for the staff, data and decision-making processes of EU institutions.
What this incident reveals is the structural difficulty of securing complex cloud environments, even in organizations with dedicated teams and strict regulations. The Commission relies on CERT-UE, the central cybersecurity service for all EU institutions and bodies, which provides 24/7 surveillance with automated alert systems. It was this system that enabled the rapid detection of the January 30 attack. In the case of March 24, detection was also rapid, but did not prevent exfiltration. The question that will emerge from the investigation is less one of reactivity than of the window of exposure: how long did the attackers have access to the systems before being detected and blocked, and what did they actually take with them?
The incident also reopens a debate that Brussels would no doubt prefer to keep at bay: that of digital sovereignty. That the Commission’s public infrastructure, the Union’s digital showcase, is hosted by an American cloud provider has not gone unnoticed, in a context where the EU is precisely pushing to reduce dependence on suppliers deemed sensitive.
Sources :
- BleepingComputer: European Commission confirms data breach after Europa.eu hack
- BleepingComputer: European Commission investigating breach after Amazon cloud account hack
- Hackread: ShinyHunters Claims 350GB Data Breach at European Commission
- SecurityAffairs: ShinyHunters claims the hack of the European Commission
- Infosecurity Magazine : European Commission Confirms Cloud Data Breach
- ComplexDiscovery : The DKIM Problem: Why the European Commission Breach Threatens Inboxes Worldwide
- European Commission: The Commission responds to a cyber-attack on its web platform (IP_26_748)
- European Commission: The Commission responds to a cyber-attack on its mobile device management system (IP_26_342)
- The Record: European Commission downplays ShinyHunters cyber claim
