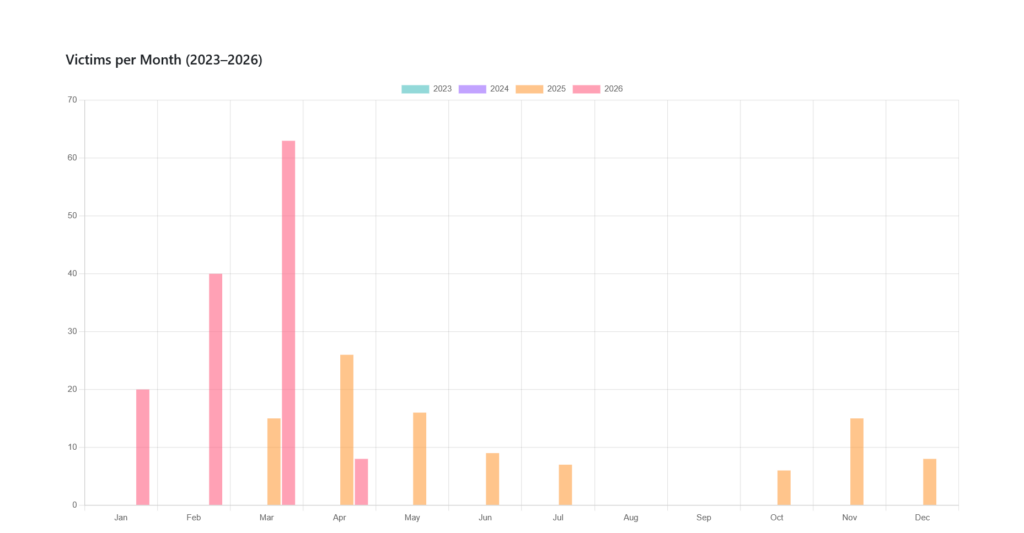
More than 200 victims in just over a year, an increasingly sophisticated GB payload, and, in its early days, a server hostname that displayed the operator’s pseudonym in cleartext. NightSpire illustrates a rare trajectory in the ransomware landscape of 2026: a group that emerged with the operational shortcomings of a novice player, yet managed to escalate at remarkable speed, to the point where it now ranks among the most active groups in the ecosystem.
Table des matières
ToggleFrom Rbfs to NightSpire: a rebrand that deceives no one
NightSpire is most likely the successor to Rbfs, a little-known group whose online presence ceased precisely when NightSpire emerged at the beginning of March 2025, although the first operations were probably earlier, according to some sources. Evidence of the link is manifold: at least two victims featured on the NightSpire leak site had previously been claimed by Rbfs, the two groups share common operators, and any reference to Rbfs on crime forums disappeared with the emergence of NightSpire.
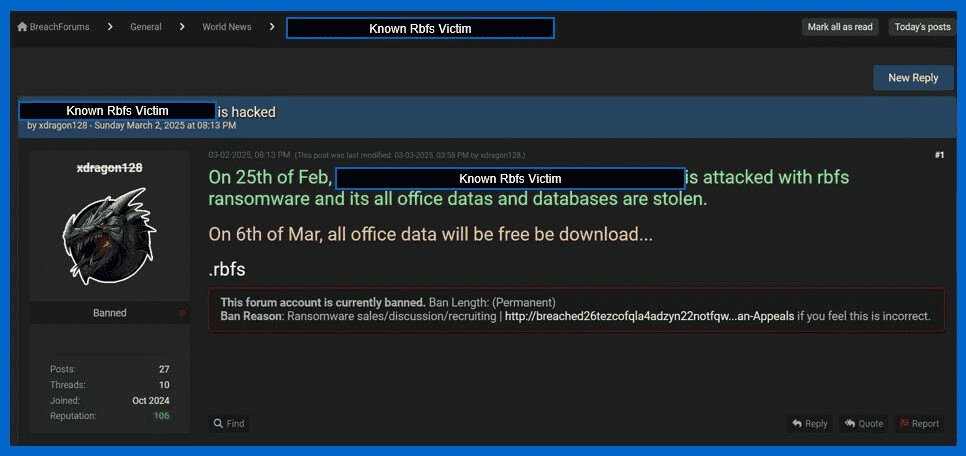
Two individuals are identified as affiliated with the group: xdragon128 (aka xdragon333) and cuteliyuan. The transition occurred rapidly in March 2025: xdragon128 was still posting Rbfs victims on BreachForums 2, while cuteliyuan was sharing Telegram links to the same victims. A few days later, xdragon128 attempted to recruit NightSpire affiliates on BreachForums 2, a platform that prohibits ransomware-related content (and which had been seized by law enforcement in May 2024 before reappearing). The initiative earned it a permanent ban.
Xdragon128 is no novice in the cybercriminal ecosystem. According to CYFIRMA’s research (December 2024), a developer using the pseudonym Paranodeus – an identity linked to xdragon128 – has been marketing a suite of tools developed in Python on underground forums since September 2024: Parano Stealer, Parano Ransomware and Parano Screen Locker. These tools, documented with anti-VM, anti-analysis, persistence and cryptographic extraction capabilities, lay the technical foundations of the group and testify to connections to the CyberVolk collective. This prior technical profile explains the sophistication of the Go payload developed under the name NightSpire a few months later. The exact meaning of the name NightSpire is said to be a reference to the World of Warcraft universe.
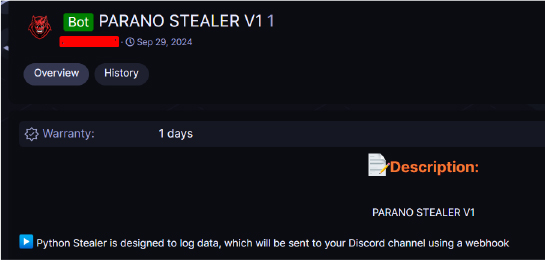
First post by Paranodeus (aka xdragon128) in September 2024, introducing his suite of tools – Source: CYFIRMA
Gmail, Apache versions exposed: the OPSEC errors of a learning group
Despite their sustained activity, by March 2025 the NightSpire operators were displaying several significant breaches of operational security. The most glaring example was the use of a Gmail address to communicate with victims: unlike ProtonMail, a Gmail box leaves a larger digital footprint and can be suspended by the provider.
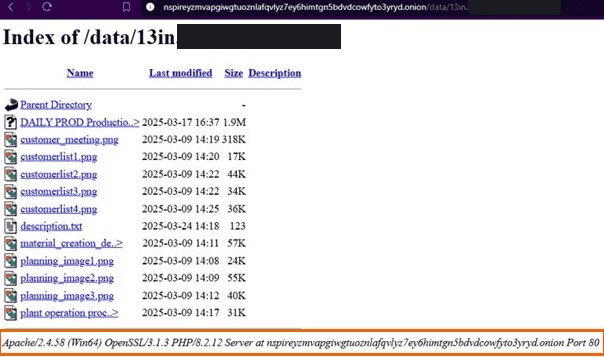
Examination of the leak site revealed directly readable infrastructure fingerprints: versions of Apache, OpenSSL and PHP exposed in the source code of the pages. In one incident analyzed by S-RM, a British firm specializing in incident response, the hostname of the attackers’ machine was XDRAGON-SERVER1 – the operator’s pseudonym written in clear text in the infrastructure.
This immature player profile has practical implications. Inexperienced groups deviate more easily from standard negotiation protocol: lack of proof of decryption, premature publication of data, failure to meet announced deadlines. This unpredictability has made crisis management more complex and demands greater flexibility from response teams.
CVE-2024-55591: the FortiOS flaw that opens all doors
NightSpire’s initial access of choice relies on the exploitation of CVE-2024-55591, a critical vulnerability in the WebSocket Node.js module of FortiOS and FortiProxy. By sending specially crafted requests, an unauthenticated attacker can obtain super-administrator rights on a FortiGate device without providing valid credentials. Fortinet disclosed the flaw on January 14, 2025, but active exploits had already been observed as early as November 2024. At the time of disclosure, hundreds of thousands of devices exposed on the Internet were still running vulnerable versions.
NightSpire also features secondary access methods: brute-force RDP and credential stuffing against exposed remote desktop services, phishing campaigns disguised as browser updates, exploitation of other unpatched VPN appliances, MFA fatigue attacks combined with VPN brute-force, and compromise of MSP providers.
LOLBins, MEGA exfiltration and hybrid encryption: the attack chain deconstructed
Once inside the network, NightSpire follows a structured sequence that reveals a pragmatic understanding of contemporary defenses. The group favors native tools and legitimate services to reduce its traces.
Lateral movement and elevation of privileges rely heavily on LOLBins, the native system binaries that enable them to blend in with normal administrative activity. The observed arsenal mixes native Windows tools (PowerShell, PsExec, WMI) and hijacked third-party utilities: Mimikatz for credential extraction, Everything.exe for rapid mapping of high-value files, AnyDesk for maintaining persistent remote access. Persistence itself involves scheduled tasks and run registry keys.
The exfiltration phase systematically precedes encryption, which significantly alters the victim’s calculation: even before you know whether encryption is in progress, the data has already left the organization. Sensitive files are compressed, encrypted via 7-Zip, then transferred to MEGA cloud storage. The choice of MEGA as destination and legitimate tools (WinSCP, Rclone) for transfer reduces the chances of intrusion detection systems being triggered.
The encryption payload, developed in Go, is distinguished by two defensive features: an RC4/XOR obfuscation that complicates static analysis, and extended sleep intervals between operations to avoid behavioral detection. The encryption strategy itself is calibrated for speed: partial encryption in 1 MB blocks for large files (disk images, backups, databases), full encryption for others. Each file receives a unique AES key protected by the attackers’ RSA public key. Affected files bear the .nspire extension, accompanied by a ransom note readme.txt.
NightSpire has a notable feature: the group also encrypts files stored in OneDrive without modifying their extensions. Files appear normal but become inaccessible, delaying detection and extending the attackers’ operational window.
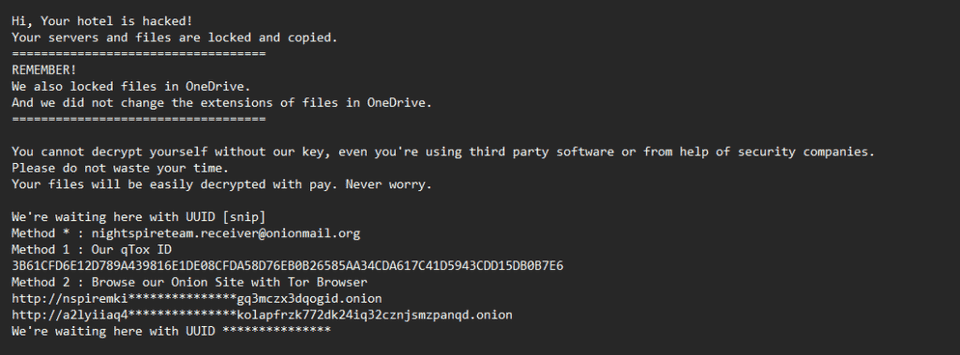
48 hours to pay: double extortion under maximum pressure
Where most groups allow several days or even weeks, NightSpire sometimes imposes just 48 hours between delivery of the ransom note and publication on its leak site. The group uses multiple negotiation channels: ProtonMail, OnionMail, Telegram, qTox and personalized chat portals hosted on Tor. Documented demands range from $150,000 to $2 million.
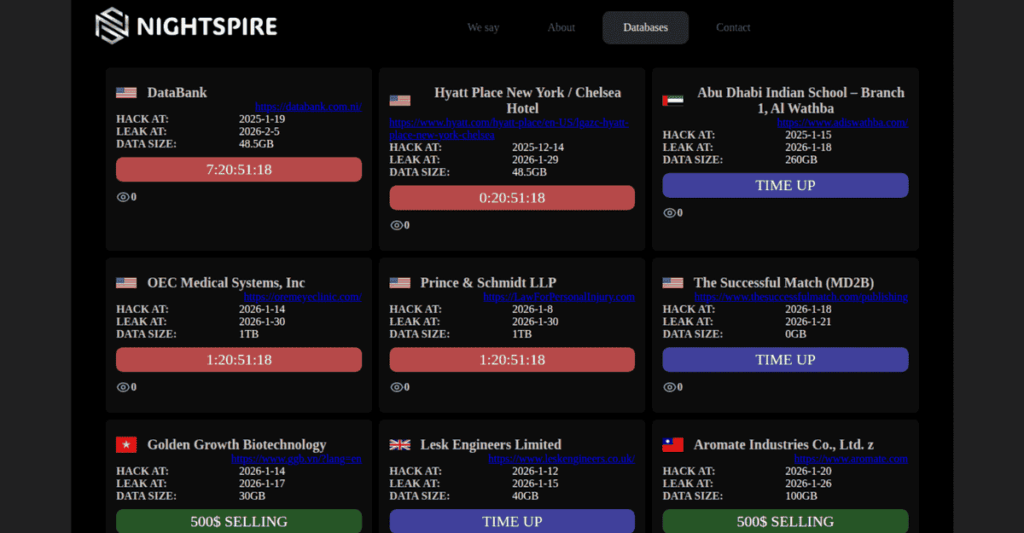
Pressure tactics go beyond the mere threat of publication: emails have been sent directly to employees of victim companies, excerpts from negotiation transcripts have been published after refusal of payment, and the group maintains a “We say” page listing non-payers with links to free downloads of the stolen data. S-RM noted in its March 2025 analysis, however, that the group’s approach to the actual publication of data is inconsistent – a further marker of an organization still in the process of structuring itself.
Manufacturing, healthcare, technology: 200 victims without sector discrimination
NightSpire targets opportunistically, without sectoral predilection. The group attacks organizations exposing vulnerable perimeter assets, whatever their industry. Manufacturing, technology and healthcare are among the most affected sectors according to Ransomware Live data (March 2026), but the dispersion over some 30 sectors confirms the lack of specialization. The majority of victims are SMEs with fewer than 1,000 employees, often lacking dedicated security teams, a profile that corresponds precisely to the group’s initial method of access.
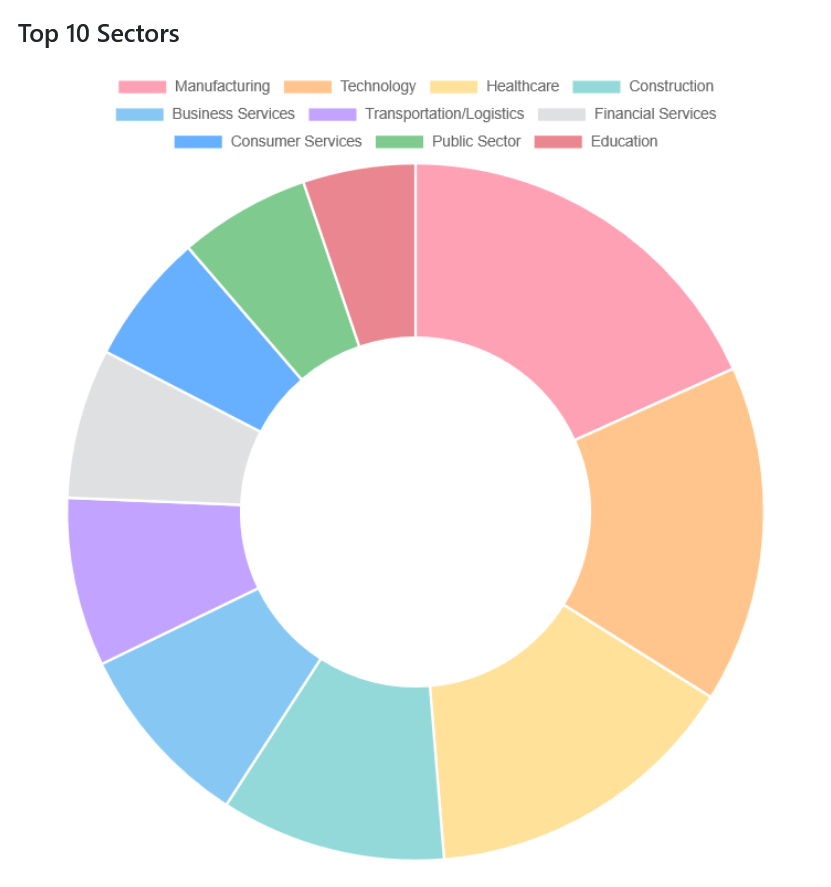
Geographically, the United States accounts for the largest share of known victims, followed by Asian countries (India, Taiwan, Japan, Hong Kong). Attacks cover more than 30 countries on all continents, including healthcare facilities in the United Arab Emirates and Peru, and government entities in South Africa and Taiwan.
Notable incidents include the attack on the Hyatt Place Chelsea New York hotel claimed in January 2026: NightSpire released as a free download 48.5 GB of data (see NightSpire dark web leak site screenshot above) allegedly stolen, including invoices, expense reports with full names and contact details of employees, signatures and partner company information. Cybernews analysis of the samples suggests that the files originated from the hotel’s internal CMS.
The fourth quarter of 2025 marked a clear acceleration: Ransomware Live recorded 23 publications on the leak site in November and December alone, with some days counting three to four simultaneous victims. The pace continued in 2026, with victims spread across the USA, Germany, Japan, Hungary, the Czech Republic, Brazil and the United Arab Emirates in February alone.
From closed group to draft RaaS: a changing business model
At its inception in March 2025, NightSpire operated as a closed structure managing the entire attack chain in-house. The evolution to full double extortion, adding encryption to the initial exfiltration, took place within just a few weeks of opening the leak site. The recruitment of a trading specialist on BreachForums 2, with an advertised remuneration of 20% of profits, signalled a desire for structuring from the outset.
Since early 2026, concrete signals of a transition to a RaaS model have been appearing. This development therefore seems likely, but awaits confirmation. Data from ransomware.live show several onion RaaS domains branded NightSpire, with “RaaS Service Started” pages listing membership conditions from February-March 2026. This trajectory is reminiscent of other emerging groups such as KillSec, which have also moved from closed operations to a service model. Cyble notes that NightSpire’s communications platform includes Telegram channels used both for public shaming and to attract potential affiliates.

Cyble also identifies groups with similar tactics or overlapping infrastructures, Storm-1567, UNC4393 and TA2101, although the precise nature of these connections remains under investigation.
Indicators of compromise
The following indicators have been observed in confirmed intrusions attributed to NightSpire.
Encryption artifacts: .nspire extension on encrypted files, OneDrive files inaccessible without visible extension change, readme.txt note containing links to Tor portals and a qTox ID.
Attacker infrastructure: hostnames WINDOWS-DTX-8GB and XDRAGON-SERVER1, remote WinSCP IP address 14.139.185[.]60, qTox ID 3B61CFD6E12D789A439816E1DE08CFDA58D76EB0B26585AA34CDA617C41D5943CDD15DB0B7E6, contact email addresses including Gmail accounts, main onion leak site a2lyiiaq4n74tlgz4fk3ft4akolapfrzk772dk24iq32cznjsmzpanqd[.]onion (replacing the original address nspireyzmvapgiwgtuoznlafqvlyz7ey6himtgn5bdvdcowfyto3yryd[.]onion which went offline in June 2025).
Hash Everything.exe observed: 35cefe4bc4a98ad73dda4444c700aac9f749efde8f9de6a643a57a5b605bd4e7.
Detection sequences: three alert sequences should trigger immediate investigation. Creation of an unauthorized admin account on a FortiGate, followed by VPN access from an unknown source (initial compromise). File enumeration via Everything.exe followed by creation of 7-Zip archives and outgoing connections to MEGA (exfiltration in progress). LSASS memory access on a domain controller followed by PsExec executions targeting several endpoints in rapid succession (encryption deployment imminent).
Protecting against NightSpire: controls that count
Patch FortiOS and FortiProxy as a priority. Apply Fortinet patches for CVE-2024-55591 (FortiOS version 7.0.17 or later). Audit FortiGate devices for unauthorized administrator accounts and unexplained configuration changes.
Restrict remote access. Disable unused RDP services, impose multi-factor authentication on all VPN and RDP access points, restrict RDP to dedicated jump hosts. Block WinSCP and MEGAC® on workstations where they are not required for business purposes.
Harden endpoints. Deploy EDR/XDR solutions capable of detecting unauthorized tool execution and encryption behavior. Use application control policies (AppLocker or WDAC) to block unsigned Go binaries. Monitor the creation of .nspire files and readme.txt repositories. Implement LSASS protection and monitor Mimikatz usage indicators.
Control lateral movement. Apply the principle of least privilege to all accounts, segment critical network zones, monitor and restrict the execution of PowerShell, PsExec and WMI.
Protect backups and cloud storage. Maintain backups according to the 3-2-1-1-0 strategy: three copies, two media types, one offsite, one offline, zero unverified restores. Monitor OneDrive accounts for unauthorized encryption activity and verify that version history is active with sufficient retention. Block connections to MEGA cloud on proxy or firewall layers.
In case of infection. Isolate affected systems immediately. No public decryptors are currently available. Confirmed incidents show that NightSpire did not systematically delete shadow copies (Volume Shadow Copies), making partial recovery from VSS snapshots possible. Microsoft 365 version history can also be used to recover compromised cloud files. Preserve all evidence for forensic investigations and the authorities.
RaaS transition will decide NightSpire’s future
No legal action or dismantling operations targeting NightSpire have been reported to date. The operational errors of spring 2025 have no doubt been corrected, but the group is still active, more prolific than ever, and probably in transition to a RaaS model that could further strengthen its capacity to cause harm. The window opened by its initial flaws is closing. What NightSpire has built up over the past year is enough to make it a serious threat, with or without amateurism.
Sources:
S-RM Inform: Ransomware in focus: Meet NightSpire
Cyble: Threat Actor Profile: NightSpire Ransomware Group
Proven Data: NightSpire Ransomware: How It Works and How to Defend Against It
SOCRadar: Dark Web Profile: NightSpire Ransomware
SC Media: NightSpire ransomware gang alleges Hyatt breach, leaks data
CYFIRMA: Exploration of Parano – Multiple Hacking Tools’ Capabilities
Ransomware Live: Nightspire Group Profile
