Having an EDR is no longer a guarantee. In recent attacks, Qilin affiliates have deployed a dedicated module capable of disabling over 300 threat detection and response (EDR) solutions, covering almost every vendor on the market. Cisco Talos, which published an in-depth technical analysis on April 2, 2026, describes not just a simple bypass tool, but a four-stage infection chain. The component doesn’t improvise itself during an attack: it operates entirely in memory, exploits legitimate signed drivers to get down to the Windows kernel level, and shuts down EDR monitoring mechanisms before data theft or encryption has even begun. Security processes are terminated, their telemetry reports interrupted, all without a single alert being generated.
Qilin, also tracked under the names Agenda, Gold Feather and Water Galura, has been operating in RaaS since July 2022. The group has established itself as one of the most active players in the ransomware landscape, with a marked international presence and a focus on the manufacturing and professional services sectors. Its RaaS infrastructure is attracting a growing number of affiliates with a wide range of technical skills.
Talos’ analysis highlights a reality that victimology statistics alone cannot express: when an attacker neutralizes the defensive layer itself at kernel level, the issue is no longer the detection capability of BDUs, but the existence of independent defenses capable of operating without them.
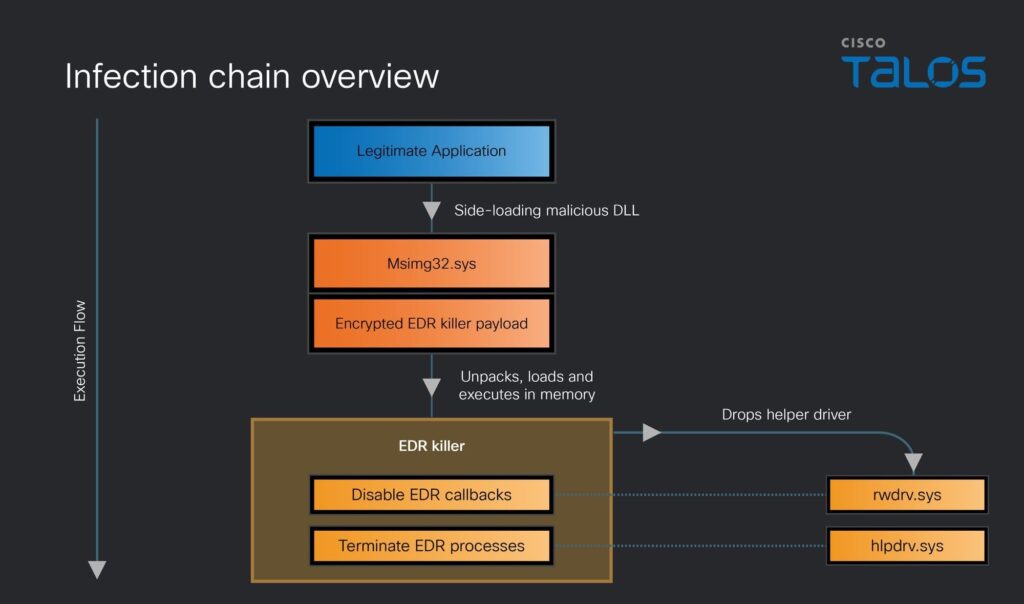
Table des matières
ToggleNeutralizing EDRs: a prerequisite for ransomware operations
Disabling endpoint defenses is no longer improvised during an attack. For several ransomware operators, it is planned and integrated into the infection chain right from the initial access. The Play Group, for example, has abandoned conventional process termination methods in favor of physically deleting security agent files via legitimate disk management utilities, thus bypassing process termination telemetry without triggering the signals usually monitored. Other operations, such as BlackSanta, target HR workstations via application decoys to neutralize EDRs before any exfiltration. Each group adapts its EDR killer to its attack vector.
What Qilin has developed is of a different nature. The architecture runs entirely in memory for critical stages, exploits signed drivers to get down to kernel level, and disables watchdog callbacks (functions that EDRs register with the Windows kernel to be alerted to each process creation, thread or module loading). Once these callbacks have been neutralized, security solutions no longer have any visibility of what’s happening on the system, and the operator can freely initiate the exfiltration or encryption phase.
Stage 1: how the booby-trapped DLL foils EDR monitoring
Side-loading msimg32.dll: a silent entry point
It all starts with a malicious DLL named msimg32.dll, side-loaded (loaded in place of the legitimate library) by an application that normally imports this Windows system library. Legitimate calls to the original API are redirected to the real msimg32.dll in C:WindowsSystem32, preserving the expected behavior of the host application, while the malicious logic is executed as soon as it is loaded via the DllMain function. This first stage touches no binary on disk: it prepares the execution environment entirely in memory for subsequent stages.
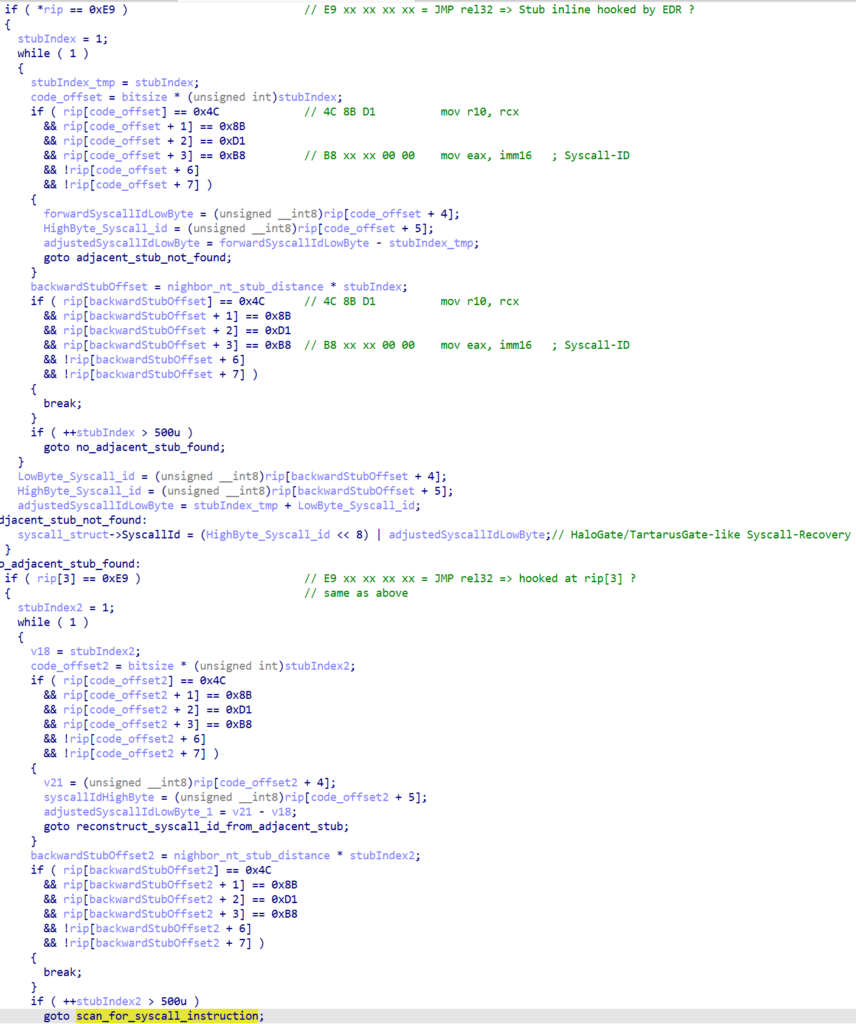
Halo’s Gate: bypassing EDR hooks without modifying them
To avoid EDR hooks, the PE loader (the in-memory execution module) implements a variant of the Halo’s Gate technique. Rather than modifying hooked stubs (entry points) in ntdll.dll, it scans forwards and backwards to locate nearby intact syscall stubs, retrieves the correct syscall identifier from the eax registry, then transits directly to kernel mode via the syscall instruction of a clean stub. The Windows kernel only evaluates the identifier in eax and does not check from which exported function the call was initiated, an architectural flaw that the malware methodically exploits.
Telemetry neutralization and control flow masking
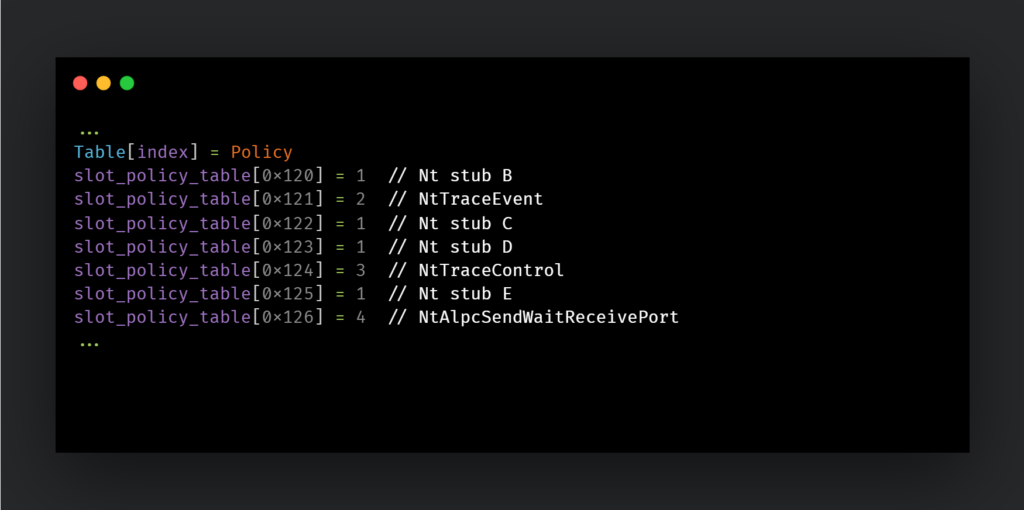
ETW (Event Tracing for Windows) telemetry is neutralized by specifically targeting NtTraceEvent, NtTraceControl and NtAlpcSendWaitReceivePort stubs. Without this telemetry, EDRs lose their main source of information on system activity.
To hide the control flow, the loader hijacks the ntdll.dll exception handler by making the .mrdata section writable via ntdll!LdrProtectMrdata, a non-exported function that the malware indirectly locates from another function used as an anchor. It substitutes its own handler, so that each exception triggers its own code. The SEH (Structured Exception Handling) and VEH (Vectored Exception Handling) mechanisms are thus hijacked to conceal API call patterns, a technique that makes dynamic analysis considerably more complex for defenders and researchers alike.
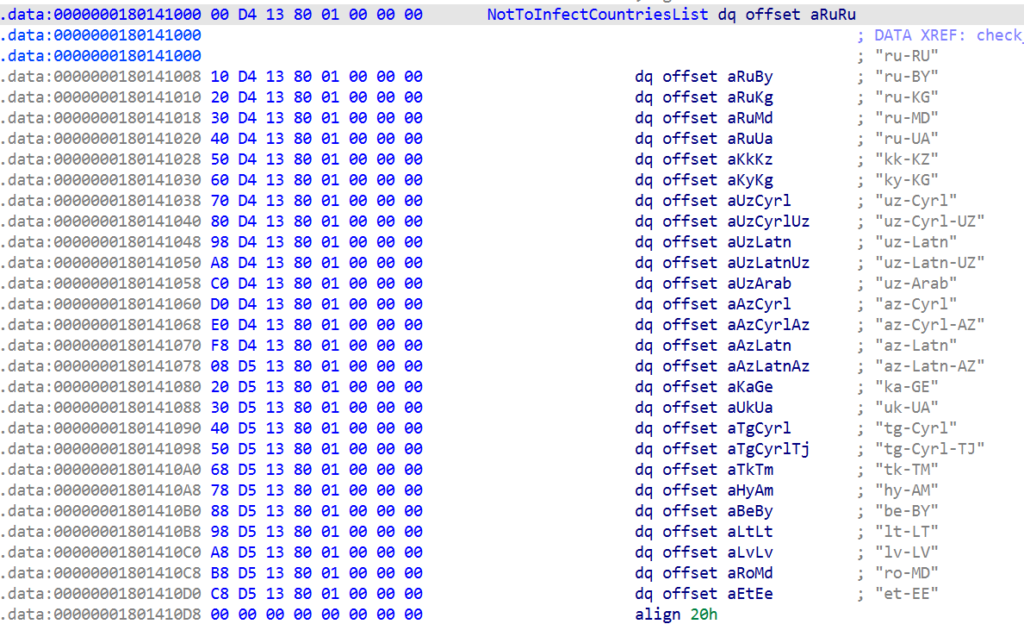
The loader also includes a geo-targeting mechanism: it terminates execution if the system is configured for a language from the countries of the former Soviet Union, a signal characteristic of a Russian-speaking actor.
Stages 2 and 3: from silent hijacking to memory loading
Stage 2: a discrete hook on process termination
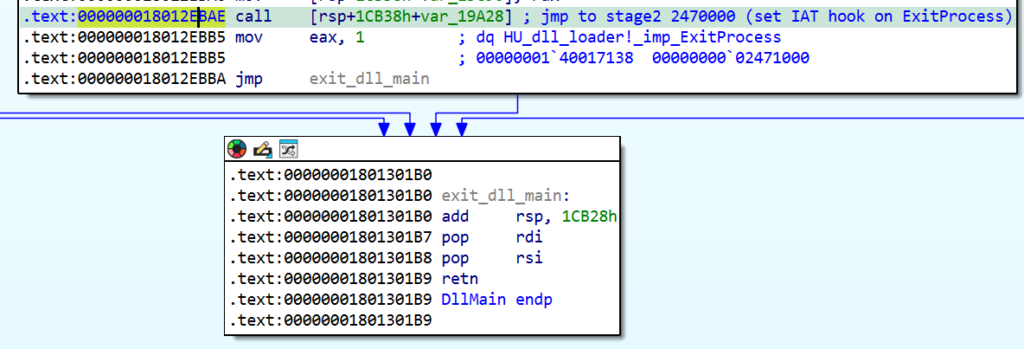
The second stage is minimalist but critical: it hooks the ExitProcess entry in the main process’s IAT (Import Address Table) to redirect execution to stage 3 on process termination. DllMain terminates normally, with no visible anomalies. The payload only activates later, a design choice that makes the malicious behavior invisible to analysis tools that focus on the initial loading phase.
Stage 3: a PE loaded entirely into memory
The third stage decompresses and loads a PE image (Portable Executable, the standard format for Windows programs) entirely in memory, without ever writing it to disk. The technique is particularly sophisticated: rather than loading the PE directly, the malware maps shell32.dll into memory, overwrites its contents with the decoded PE image, then uses hardware breakpoints on ntdll!NtOpenSection and ntdll!NtMapViewOfSection to hijack the internal mechanisms of the Windows loader(LdrpMinimalMapModule). The result: a complete executable runs in memory under the guise of a legitimate system library.
In an anecdotal note, the malware author deliberately named the dummy DLL call after a well-known security researcher, a gesture that Talos interprets as an intentional provocation. The loaded image constitutes stage 4: the EDR killer itself.
Stage 4: the BDU killer, from vulnerable pilot to defense neutralizer
BYOVD and rwdrv.sys: accessing physical memory via a signed driver
Once the EDR killer PE is in memory, the tactics change. The component relies on the BYOVD (Bring Your Own Vulnerable Driver) technique and loads a renamed version of rwdrv.sys, a driver developed by TechPowerUp LLC for its ThrottleStop hardware diagnostic tool. This driver, digitally signed with a valid certificate, is also used by the GPU-Z utility, giving it apparent legitimacy in the eyes of Windows signature control systems. Cisco Talos notes that despite its benign origin, this driver exposes highly privileged functionality without imposing any significant security controls.
Via input/output control (IOCTL) interfaces, rwdrv.sys offers direct access to hardware ports, processor-specific registers (MSRs) and, above all, raw physical memory. Herein lies the ingenuity of the approach: rather than modifying EDR processes in virtual space (which would trigger alerts), the malware locates critical EDR driver data structures in physical memory and rewrites them directly, without ever touching the binary images on disk.
In concrete terms, the component iterates through a list of over 300 security drivers covering virtually every vendor on the market. For each one, it locates the callback pointers in physical memory, the process creation, thread creation and image loading callbacks that EDR solutions use to monitor the system, and replaces them with empty pointers or harmless routines. The EDR is rendered inoperable without its process having been affected, a technical distinction which explains why this attack evades conventional process protection mechanisms.
A driver already exploited by other groups
Abuse of rwdrv.sys is not exclusive to Qilin: affiliates of the Akira group have also exploited this same driver to neutralize Microsoft Defender, a technique observed as early as mid-July 2025 according to GuidePoint Security. The vector is shared across the ransomware ecosystem, reinforcing the urgency of blocking this specific driver and, more broadly, of adopting a defense strategy that does not depend on a single layer. Qilin itself diversifies its approaches: the group has also deployed a Linux variant on Windows to bypass single-OS-centric defenses, whereas the EDR killer documented here targets Windows kernel space exclusively.
Process termination and stealth restoration
Once callbacks have been disabled, a second auxiliary driver, hlpdrv.sys, comes into play. Via IOCTL code 0x2222008, this driver forces the termination of active security processes, including Windows Defender, which no longer benefit from callback protection. EDR processes stop without being able to generate alerts or restart themselves.
A final, counter-intuitive step completes the sequence: the malware restores the CiValidateImageHeader callback (the code integrity verification function that Windows uses to validate images loaded into the kernel), which it had previously bypassed by substituting the pointer with a routine that returns true under all circumstances. This restoration reduces the traces left in the kernel and reflects a particular attention to post-exploitation hygiene, a level of discipline rarely seen in common ransomware kits.
A wake-up call for defense in depth
The fact that Qilin manages to disable over 300 EDR solutions via a single malicious DLL is a major red flag. If the entire detection strategy relies on endpoint agents that can be neutralized at the kernel level, the organization is left without visibility precisely when it needs it most. Implementing kernel-level integrity monitoring and network-based behavioral detection is not an optional extra: these are the layers that continue to work when the endpoint agent has been silenced. This is the most direct operational conclusion of the Talos analysis, and the most urgent to implement.
Indicators of compromise published by Cisco Talos
| Component | Type | MD5 | SHA1 | SHA256 |
|---|---|---|---|---|
| msimg32.dll | Malicious DLL (stage 1) | 89ee7235906f7d12737679860264feaf | 01d00d3dd8bc8fd92dae9e04d0f076cb3158dc9c | 7787da25451f5538766240f4a8a2846d0a589c59391e15f188aa077e8b888497 |
| rwdrv.sys | Legitimate driver abused | 6bc8e3505d9f51368ddf323acb6abc49 | 82ed942a52cdcf120a8919730e00ba37619661a3 | 16f83f056177c4ec24c7e99d01ca9d9d6713bd0497eeedb777a3ffefa99c97f0 |
| hlpdrv.sys | Process termination driver | cf7cad39407d8cd93135be42b6bd258f | ce1b9909cef820e5281618a7a0099a27a70643dc | bd1f381e5a3db22e88776b7873d4d2835e9a1ec620571d2b1da0c58f81c84a56 |
| EDRKiller.exe | Memory dump (stage 4) | 1305e8b0f9c459d5ed85e7e474fbebb1 | 84e2d2084fe08262c2c378a377963a1482b35ac5 | 12fcde06ddadf1b48a61b12596e6286316fd33e850687fe4153dfd9383f0a4a0 |
EDRKiller.exe (additional metadata) :
ImpHash 05aa031a007e2f51e3f48ae2ed1e1fcb – Compile timestamp: June 14, 2025, 08:33:52 UTC
The compilation timestamp indicates that the component was developed almost ten months before its public documentation in April 2026, confirming a significant period of operational use.
ClamAV detects this component under the signatures Win.Malware.Bumblebee-10056548-0, Win.Tool.EdrKiller-10059833-0 and Win.Tool.ThrottleStop-10059849-0. Snort2 rules SIDs 1:66181 and 1:66180, as well as Snort3 rule SID 1:301456, cover this threat.
How to protect yourself against a kernel-based attack
Faced with an infection chain designed to operate entirely in memory and bypass EDR hooks, defense in depth is not an abstract principle.
1. Block the loading of known vulnerable drivers
Microsoft publishes and updates a list of vulnerable drivers as part of its Vulnerable Driver Blocklist program. Its deployment via Windows Defender Application Control (WDAC) or signed driver policies significantly reduces the BYOVD surface. The list should include rwdrv.sys and its known hashes.
2. Enable HVCI to prevent BYOVD attacks
Hypervisor-Protected Code Integrity (HVCI) prevents the loading of unsigned or block-listed drivers at hypervisor level, making BYOVD attacks considerably more difficult even in the event of local compromise. This is the most direct measure against the vector exploited by Qilin.
3. Monitor DLL side-loading
The loading of msimg32.dll from a directory other than C:WindowsSystem32 by a legitimate application is an early attack signal, and potentially the only one observable before the infection chain switches to memory. The Snort detection rules published by Talos cover this indicator.
4. Maintain endpoint-agent-independent visibility
Cisco Talos explicitly recommends a multi-layered approach. Centralized logging (SIEM), network behavioral monitoring and segmentation are independent safety nets that retain their usefulness even if the EDR is neutralized. When the endpoint layer is compromised, it is these devices that make the difference between late detection and a total absence of visibility.
5. Limit local administrator rights
The entire Qilin infection chain requires administrator privileges to run. Reducing the number of accounts with these rights via PAM (Privileged Access Management) directly limits the exploitation surface, and is the simplest preventive lever to activate.
The war on EDRs, a structural trend in ransomware
The module documented by Cisco Talos is part of a major trend in which the neutralization of security agents has become a prerequisite for any serious ransomware operation. The EDR killer component’s compilation timestamp (June 2025) indicates that this capability was developed and refined over several months before its public documentation.
The escalation is structural: as modern EDRs improve their behavioral detection, ransomware groups move up a level by directly targeting the defensive layer rather than dodging it. The technical sophistication illustrated by the four-stage chain of Qilin, Halo’s Gate, SEH/VEH hooks, BYOVD via physical memory, testifies to R&D investments that go far beyond the scope of a simple standard RaaS kit. For security teams, the question is no longer whether their BDUs can be targeted, but what defenses remain as a last resort.
Sources
- Cisco Talos: Qilin EDR killer infection chain
- LeMagIT: Qilin ransomware: a tool to blind over 300 EDRs
